Secure YourZoom Collaboration
Protect your Zoom environment from attackers.
See a Demo

Zoom Is a Growing Target for Attackers
220k+
enterprise customers use Zoom, with hundreds of millions of daily meeting participants.
Source: Zoom
30%
of security teams struggle to see all security settings for SaaS apps.
Source: Cloud Security Alliance
$4.5 M
in losses incurred through data breaches resulting from compromised accounts.
Source: IBM, 2023
How Abnormal Secures Your Zoom Platform
Integrates via API
Connect Abnormal’s cloud-native API architecture directly with Zoom. Automatically ingest and normalize access data for every human that signs in to Zoom.
See the Architecture

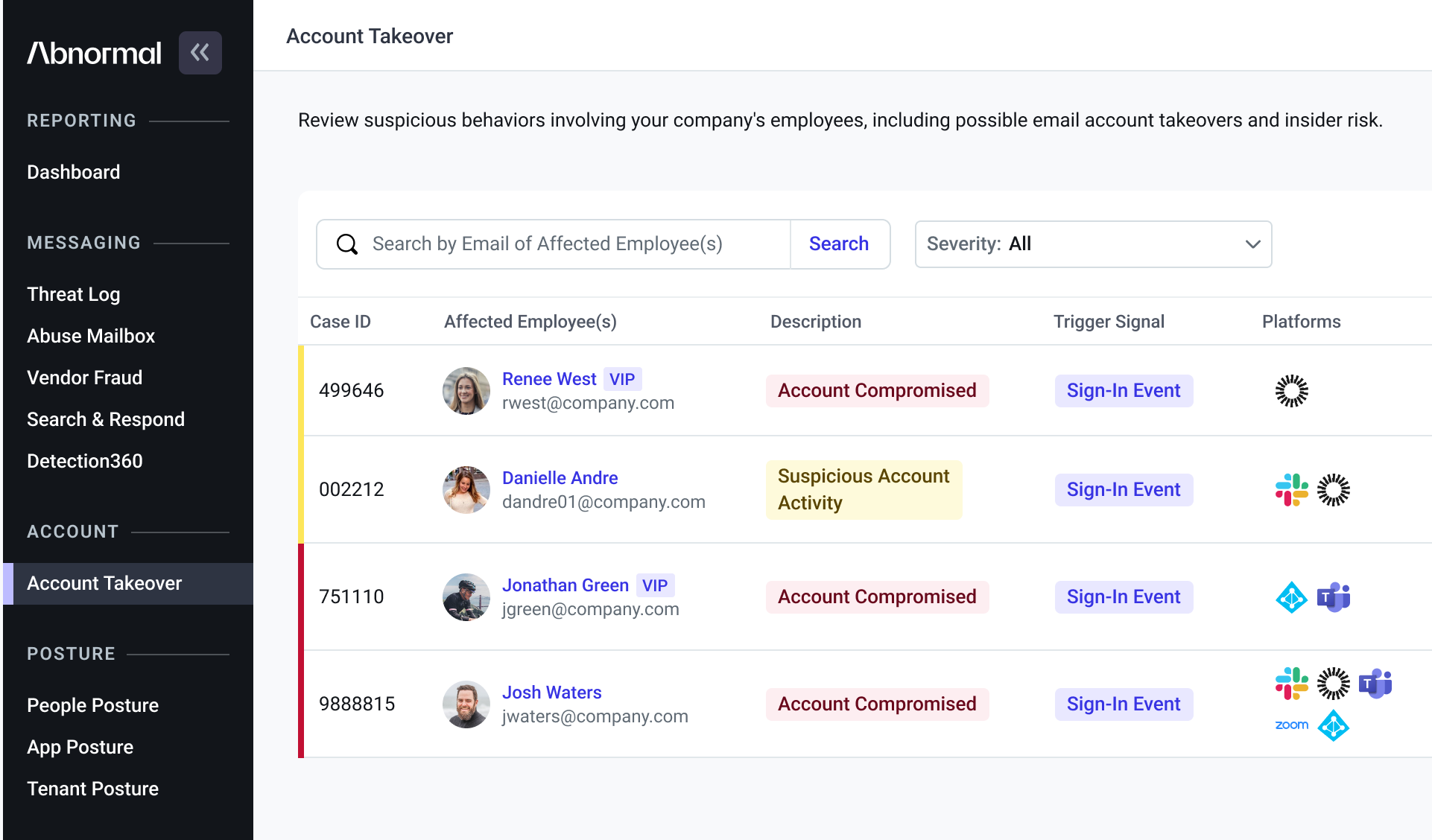
Detects Account Takeovers
Analyze user login activity and identify compromised accounts with authenticated Zoom access using Abnormal Human Behavior AI. Alerts give you the right threat information and context to investigate and remediate accounts.
Stop Account Takeovers

Reduces Privilege-Related Risk
Gain insight into user permissions and privileges with an understanding of every human in the Zoom ecosystem. Receive alerts if a high-risk change occurs that may indicate an attack.
Improve Your Security Posture

Detects Malicious Messages
Stop suspicious URLs with AI understanding that detects malicious content with high accuracy. If a malicious link is clicked, security teams can easily and quickly investigate the spread of an attack because Zoom events are logged alongside email alerts.
Discover Messaging Security

Simple, Effective Security for Zoom
High-Efficacy Threat Detection
Confidently identify suspicious sign-in activity and user privilege risks.
Unified Zoom and Email Insights
View suspicious activities from Zoom in the same pane as those stemming from your email platform.
Rich Context for Attack Investigation
See necessary context to investigate and remediate a potential threat from Zoom.
Abnormal is one of those few products in IT that actually does what it says it's going to do. The efficacy is so much higher, incorporating that decision-making into their AI. The biggest thing that stands out for us is the low false positives and the amount of time that you can actually save.”
— Vincenzo Baldwin, Executive Director of IT Infrastructure,
Kroenke Sports & Entertainment
Frequently Asked Questions
“Our executives and Board of Directors are commonly hit with significant amounts of phishing and BEC email attacks. Abnormal’s behavioral-based modeling and pattern recognition have been great in detecting and stopping those attacks. We are confident we have the right solution in place.”
— Jeremy Smith, CISO, Avery Dennison
Detect Signs of Compromise Across Zoom
Catch attacks in your collaboration apps with a Human Behavior AI platform.
Request a Demo
Request a Demo