Generative AI Attacks
Stop new attacks created by Generative AI tools like ChatGPT, Google Gemini, and WormGPT.
See a Demo
Discover AI-Generated Attacks

PROBLEM
The Rising Threat of Generative AI
Tools like ChatGPT and Google Gemini have made it possible for bad actors to increase the volume and sophistication of their attacks seemingly overnight. Attackers can now trick more people in less time—resulting in the potential for exponential losses.

SOLUTION
How Abnormal Stops AI-Generated Attacks
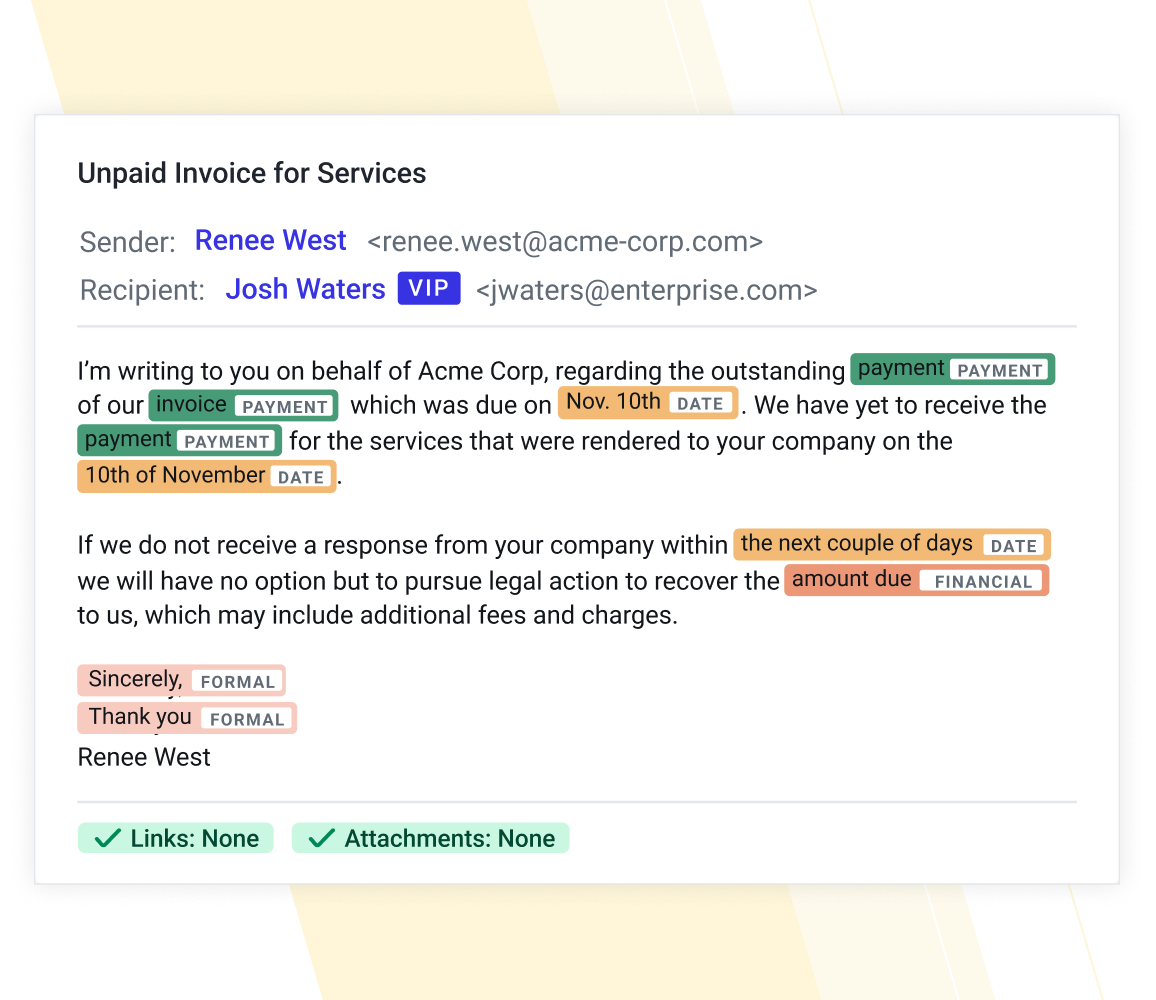
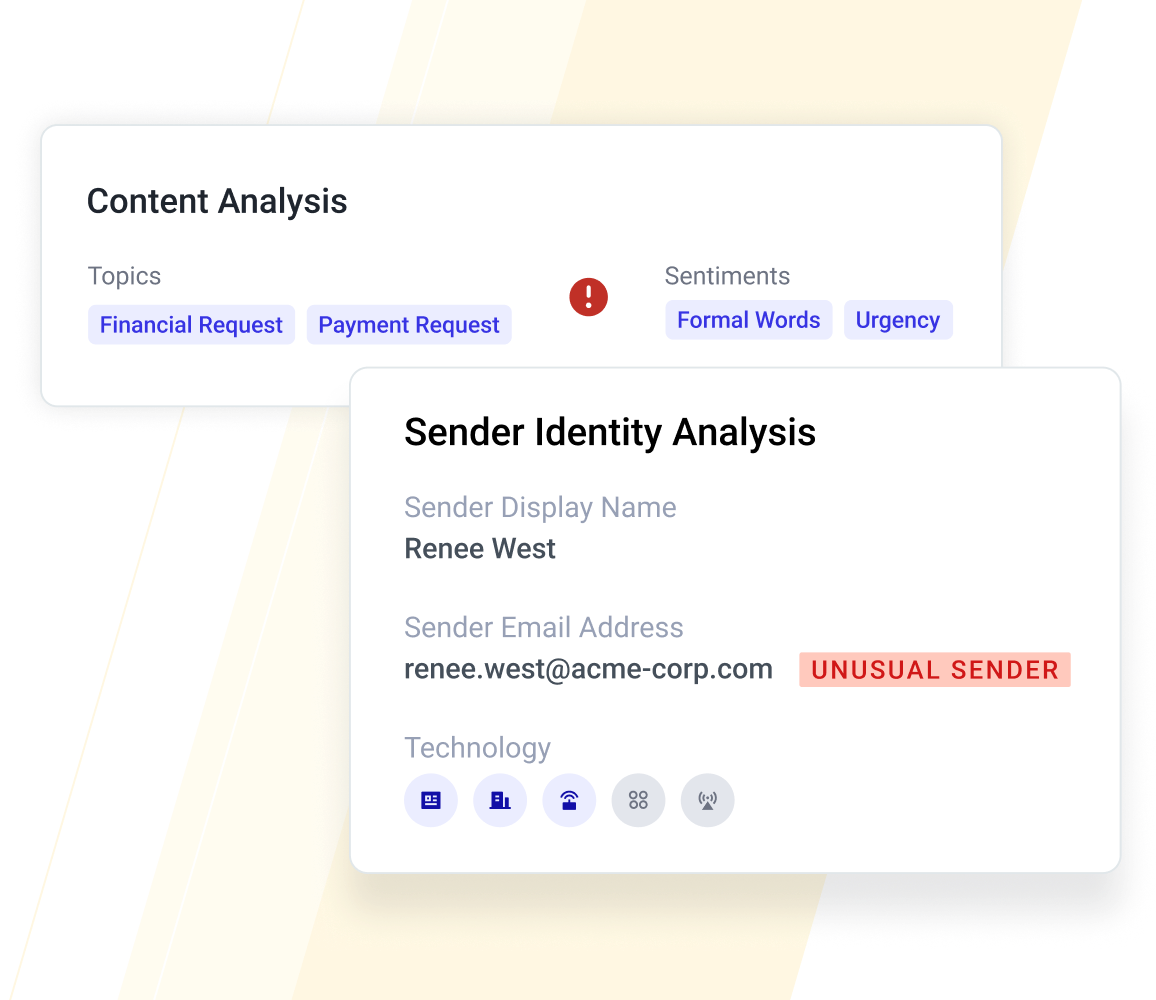
- Employs Human Behavior AI to detect fraudulent topics, tone, and sentiment, including urgency and formality.
- Detects unusual senders by understanding normal business relationships and communication patterns.
- Leverages the API architecture to ingest valuable behavior signals from M365, Okta, CrowdStrike, and multi-channel communication platforms.
WHY ABNORMAL
An AI-Native Approach to Stopping AI-Generated Attacks
- Ingests unique signals about employee behavior and vendor communication patterns that attackers can’t access with publicly available information.
- Trains AI models personalized for each organization to detect anomalous activity across internal users and external partners.
- Remediates AI-generated attacks automatically, preventing employees from viewing or engaging with them.
Adversaries are changing from year to year and toolset to toolset, and we have to shift constantly as well. Our school of thought is if attackers now are using sophisticated techniques like AI, we should be using AI to combat them, and Abnormal delivers that for us."
— Jeff McDonald, Senior VP of Technology Services, Vituity
See an AI-Based Attack
Learn how attackers are using Chat GPT to craft more realistic and convincing email attacks.
Read the Blog
Read the CISO Guide
Learn how to protect your organization from AI-generated attacks.
Read the CISO Guide
Take the ChatGPT vs Human Quiz
See if you can spot what's different about AI-generated attacks.
Take the Quiz
Get AI Protection for Your Human Interactions
Protect your organization from the full spectrum of email and collaboration application attacks with Abnormal.
Request a Demo
Request a Demo