CoreSecurity Posture Management
Discover and fix key security configuration risks across your cloud email environment.
Watch a Demo
Get the CISO Guide to Email Platform Attacks

PROBLEM
Cloud Configurations are an Email Security Blind Spot
Subheading text goes here
New Risks
Attackers are exploiting configuration gaps across user accounts, third-party apps, and mail tenants.
Lack of Visibility
Security teams struggle to get a centralized view of posture changes and to determine risk.
Time-Consuming
Security teams must manually audit and track posture in an increasingly complex environment.
How Abnormal Empowers Security Teams with Posture Insights
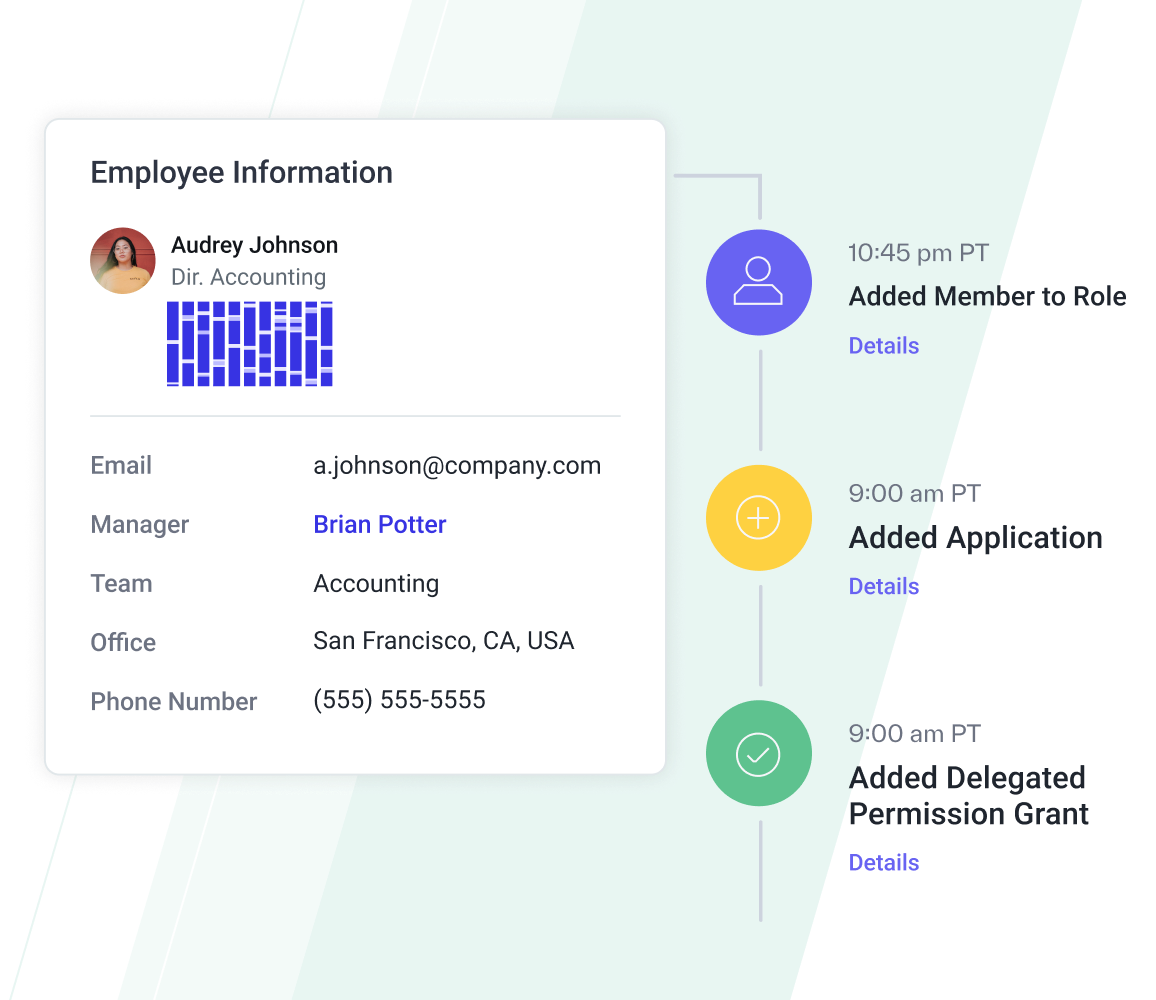
Builds Behavioral Profiles Across the Environment
Human Behavioral AI in Abnormal Knowledge Bases builds unique profiles of all humans, connected third-party applications, and email tenants in your cloud email environment.
Abnormal operationalizes this data to surface risky changes to user privileges, app permissions, and tenant security policies that could lead to increased risk.
Continuously Monitors for Configuration Drifts
Abnormal continuously surfaces high-impact changes for accounts, tenants, and applications, scoring each based on risk. With one click, security teams can see the context of the change and identify the appropriate next steps.
No more quarterly audits, spreadsheets, or PowerShell scripts to identify new risks in your environment.
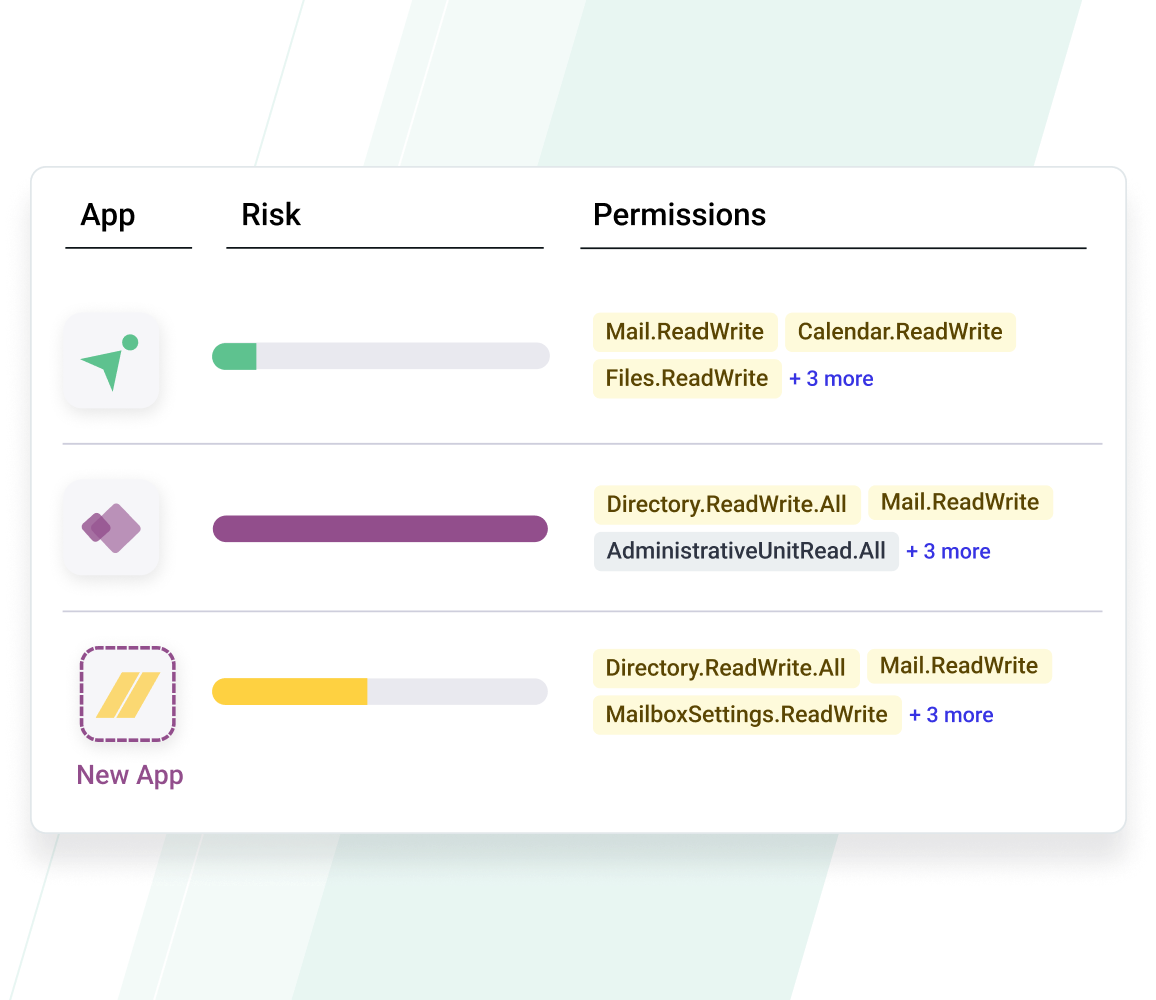
Alerts on High-Risk Activity
Abnormal provides immediate alerts on high-risk posture changes, including integrated applications gaining read/write access to VIP mailboxes, new administrators added to the environment, and changes to mail tenant conditional access policies.
With this information, security teams can take the appropriate downstream action to mitigate potential risks.
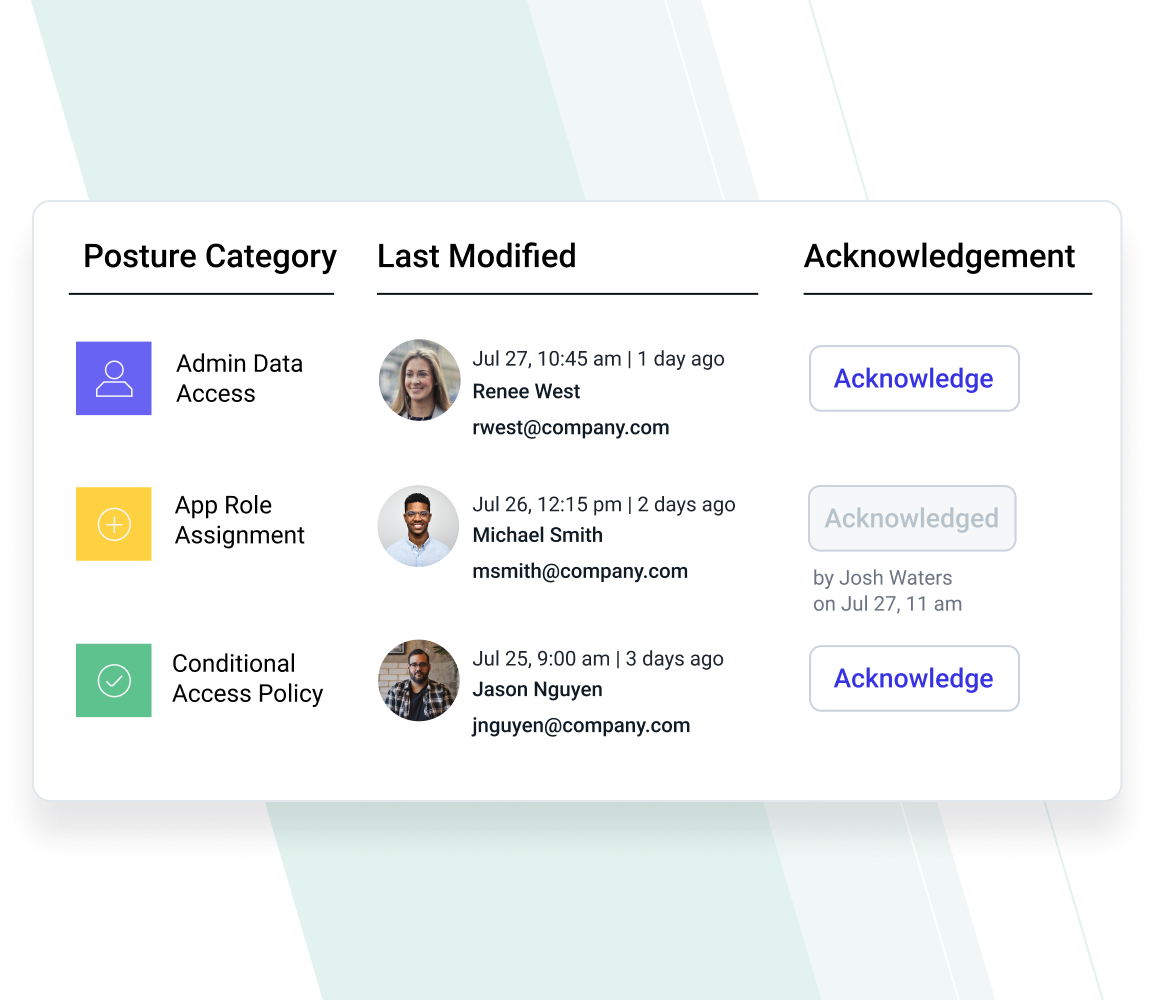
Facilitates Focused Action on Posture Gaps
Abnormal provides a dashboard where analysts can review new configuration changes and clear those that are relatively low risk or expected. Additionally, through cross-product integration, any changes associated with a compromised user are analyzed in Abnormal Account Takeover Protection Cases to bolster threat investigation and response.
See How Email Security Posture Management Works
Dynamic Monitoring
Surface high-impact changes
to the users, apps, and mail
tenants that make up the cloud
email environment.
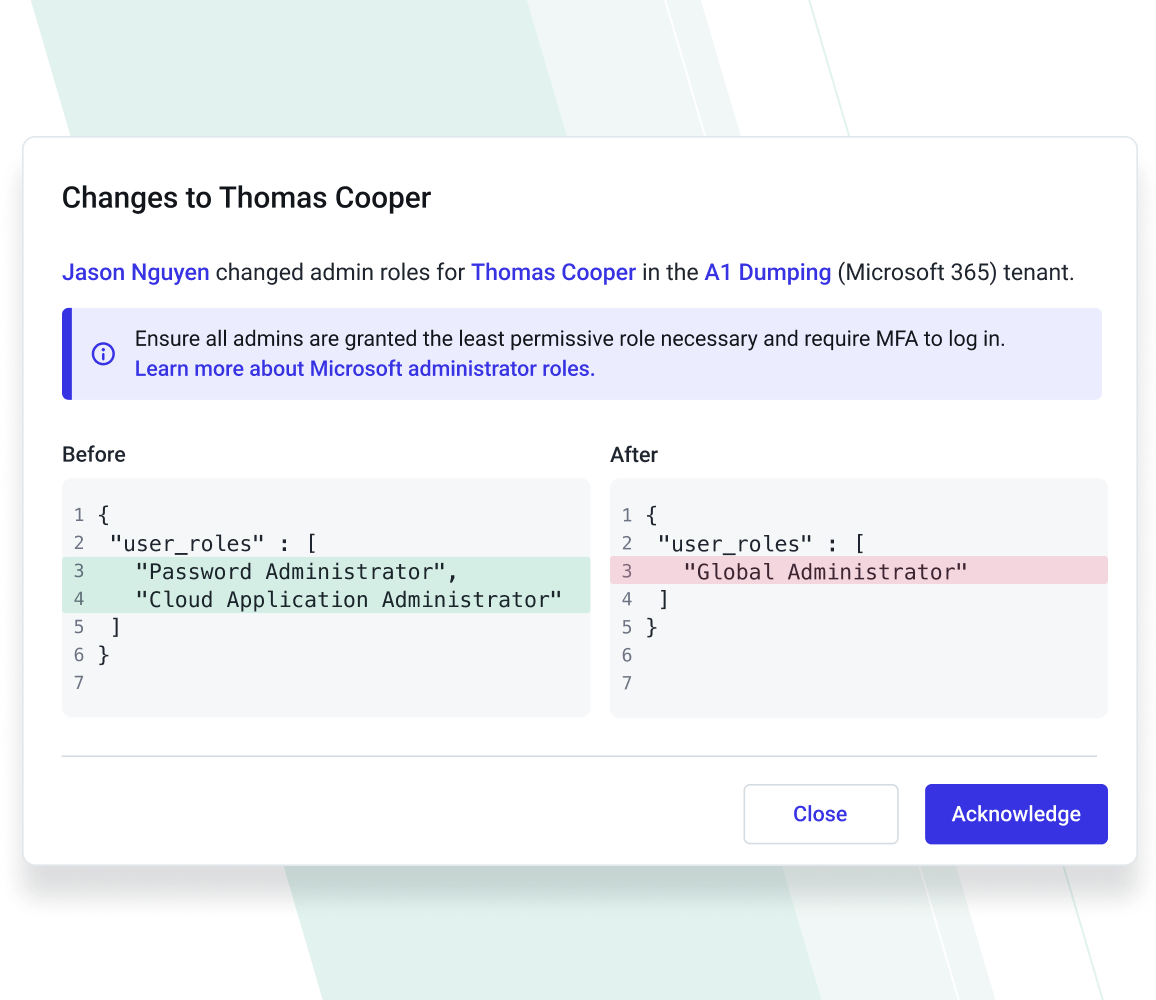
Contextual Change Insights
Drill down into changes to get a before-and-after view and links to Knowledge Base entries for affected entities.
Response Workflows
Mark each change in an acknowledgment workflow, schedule email notifications, and export events to the SIEM.
I love the fact that the Security Posture Management solution quickly and easily reduces our security risks in our cloud email tenant with continuous behavioral monitoring of changes made by our people and third-party application permissions that may be too broad."
— Matt Manire, Executive Director of Information Security, Gateway Church
Related Resources
Get Visibility into Your Security Posture
Find and fix configuration gaps in your email platform.
Request a Demo
See a Demo





