CoreAccount Takeover Protection
Analyze human behavior to detect and mitigate email account takeovers in real time.
See a Demo
PROBLEM
Account Takeovers Lead to Costly Data Breaches
Subheading text goes here
Common
Nearly 80% of Fortune 1000 organizations have at least one compromised account.
Frequent
1 in 4 organizations is targeted by an account takeover attempt every week.
Costly
Data breaches caused by compromised credentials cost organizations an average of $4.5M.
How Abnormal Stops Email Account Takeovers in Real Time
Detects Compromised Email Accounts
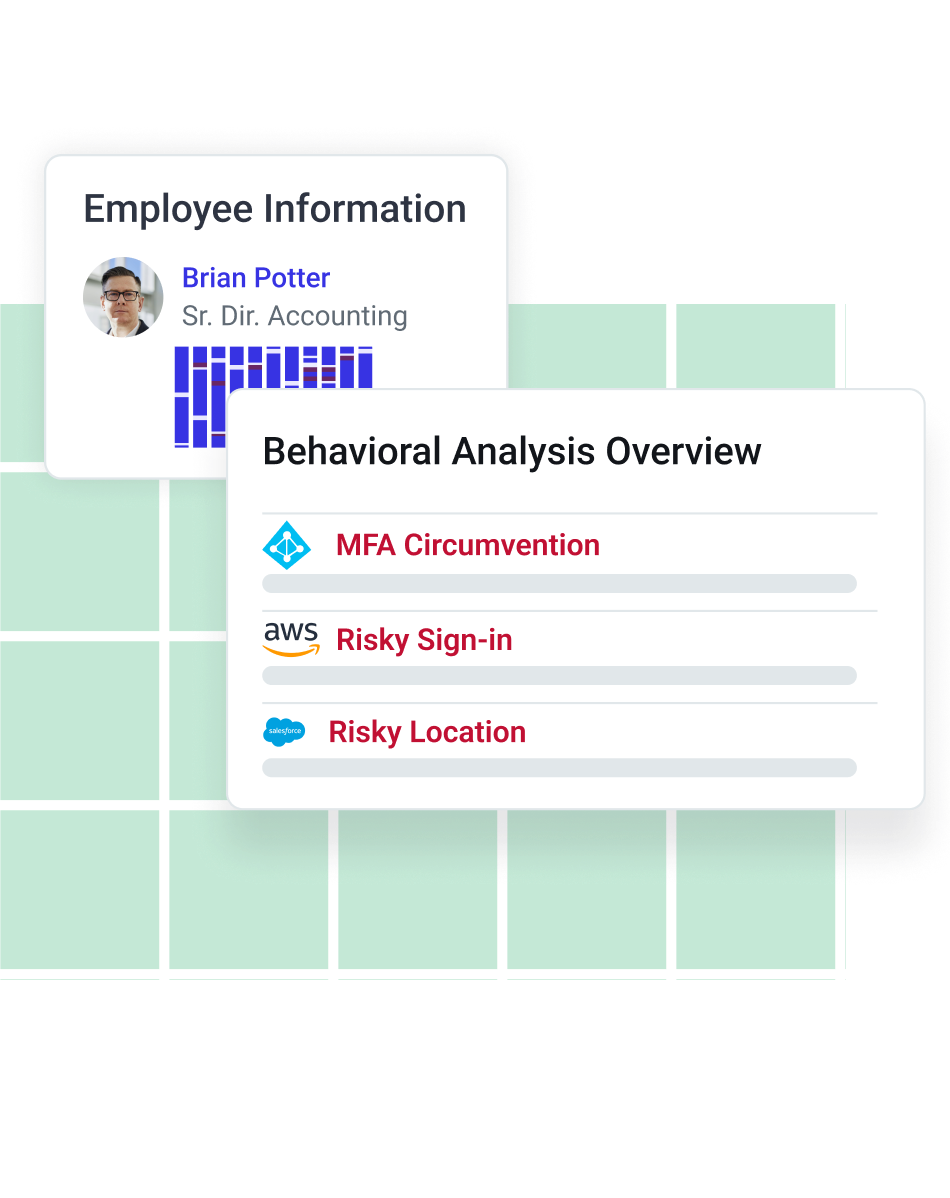
Abnormal’s cloud-native API architecture easily integrates with Google Workspace, Microsoft 365 and its 85+ associated apps like OneDrive, Intune, Sharepoint, Outlook, Teams, and Dynamics—as well as XDR tools and identity providers like CrowdStrike, Okta, and Azure Active Directory. Leveraging the identity signals provided by these platforms, Abnormal uses human behavior AI to correlate sign-in signals with communication behavior (including internal-to-internal messages) to detect compromised accounts.
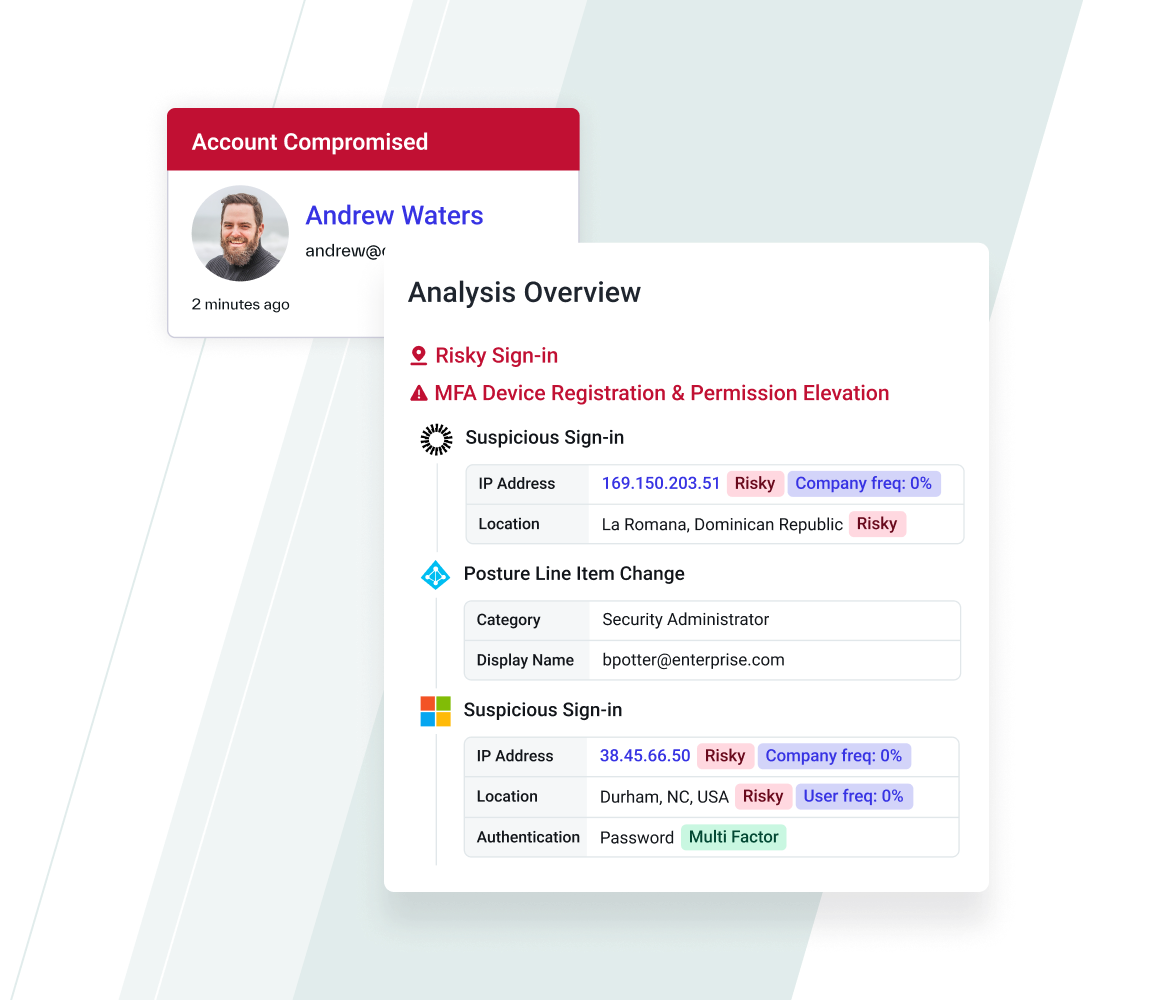
Recreates the Crime Scene in Detail
When a compromise is detected, Abnormal creates a Case for review, enriched with suspicious human behavior across email systems, identity platforms, devices, browsers, and integrated applications to provide a conclusive judgment and enable security teams to mitigate impact.
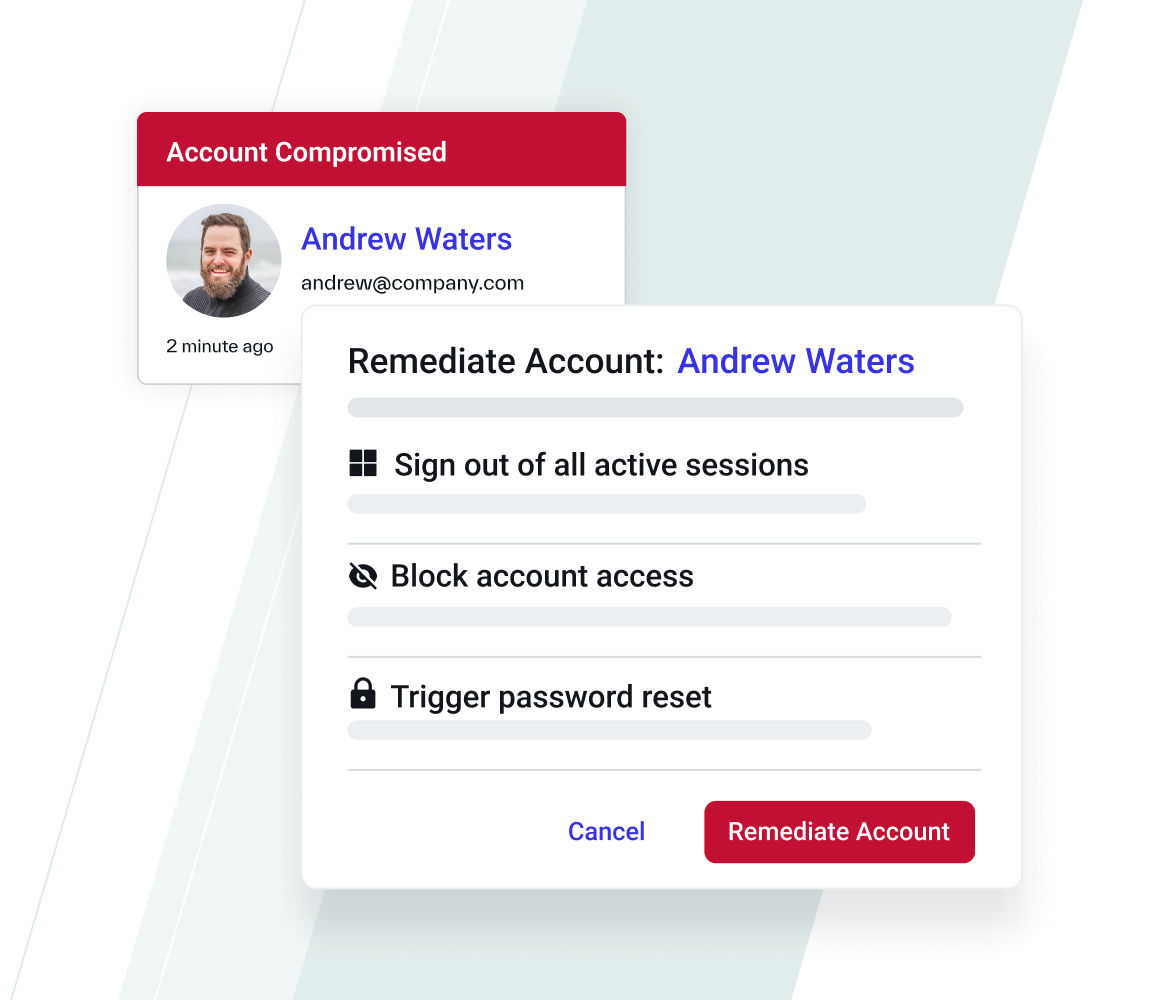
Kicks Attackers Out of Hijacked Accounts
Abnormal ejects suspicious humans out of compromised email accounts by automatically blocking access, forcing a password reset, and ending all active sessions. Administrators can choose to auto-remediate or manually review cases.
Email Account Takeover Protection Features
Account Takeover Discovery
Quickly detect compromised accounts by assessing abnormalities in locations, devices, email content, and mail rules.
Real-Time Disarming
Automatically remediate accounts by signing out of all open sessions, blocking access, and forcing a password reset.
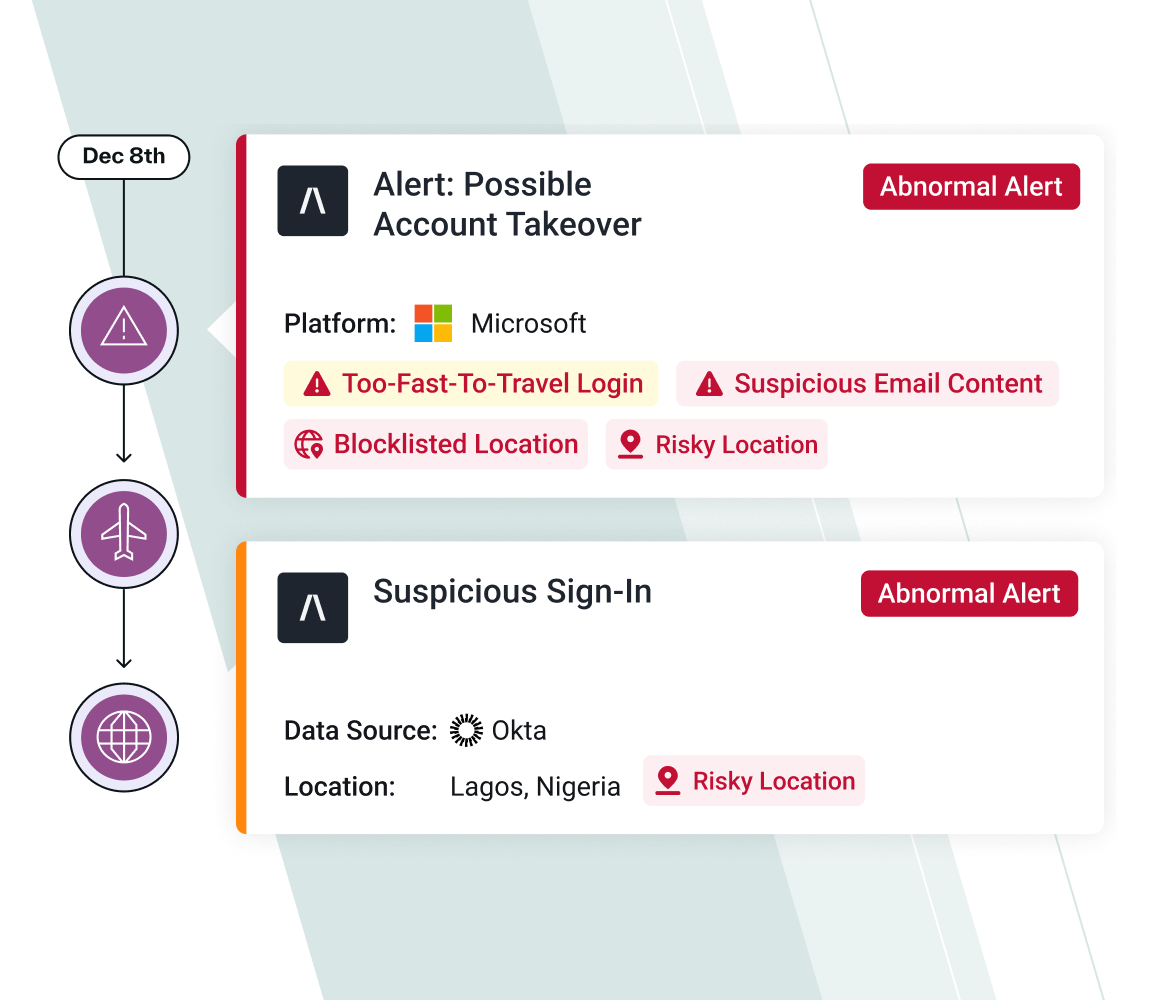
Behavioral Case Timeline
Investigate a contextual timeline of suspicious human behavior on the email platform and see the remediation steps taken.
I really like the account compromise feature that auto-detects threats and locks users out of those mailboxes. That was the real cherry on top for me, because it gives me peace of mind that not only is Abnormal blocking all the attacks, but also that if one actually succeeded, Abnormal auto-remediates that mailbox.”
— Jim Robinson, CIO, SuperConcepts
Related Resources
Detect, Disable, and Remediate Compromised Accounts
Catch account takeover attempts that other solutions miss with human behavior AI.
Request a Demo
See a Demo