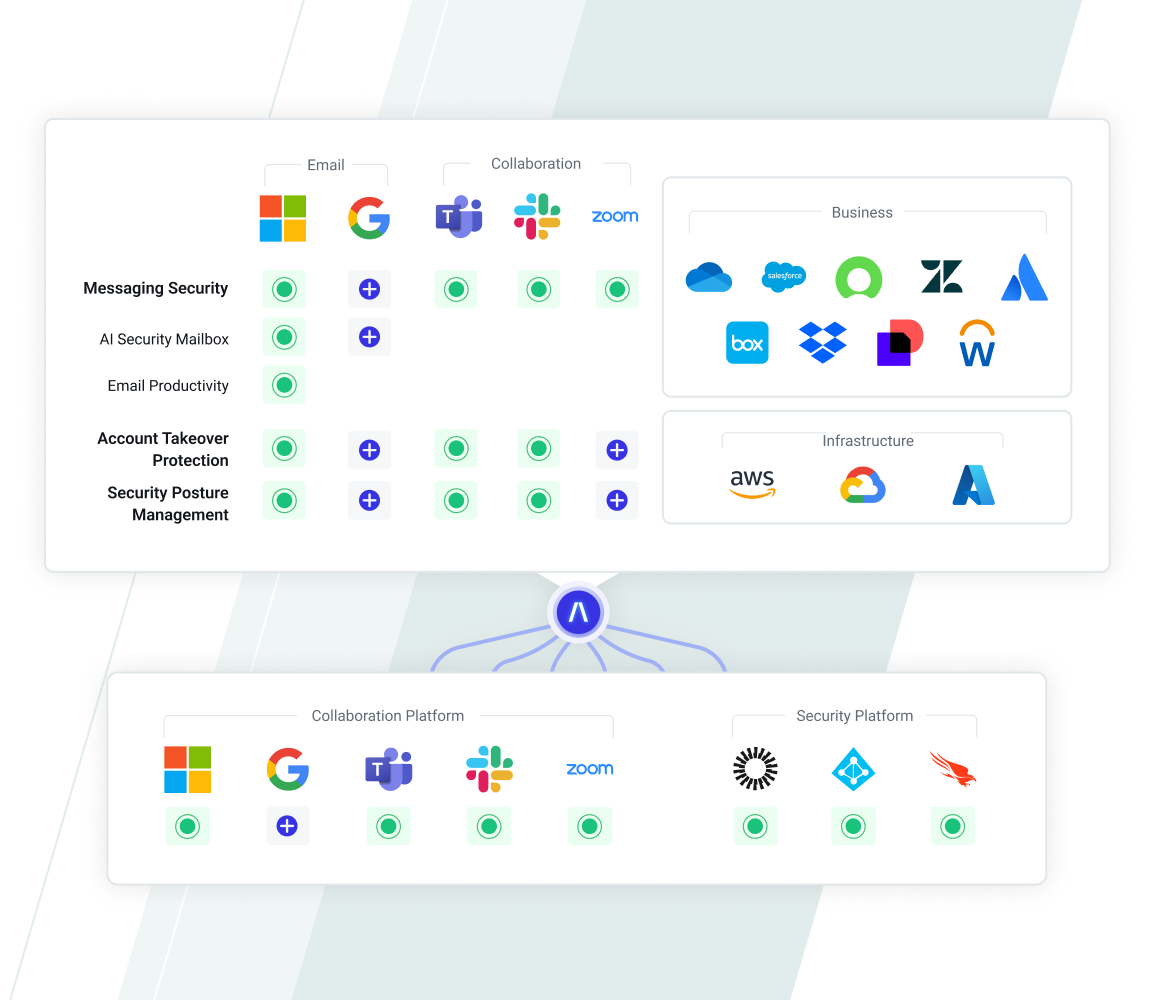
API-Based Architecture
Prevent breaches before they stop your business with Abnormal’s AI-native, API-based human behavior platform, which creates a deep understanding of user behaviors to predict attacks.
See the API Integration
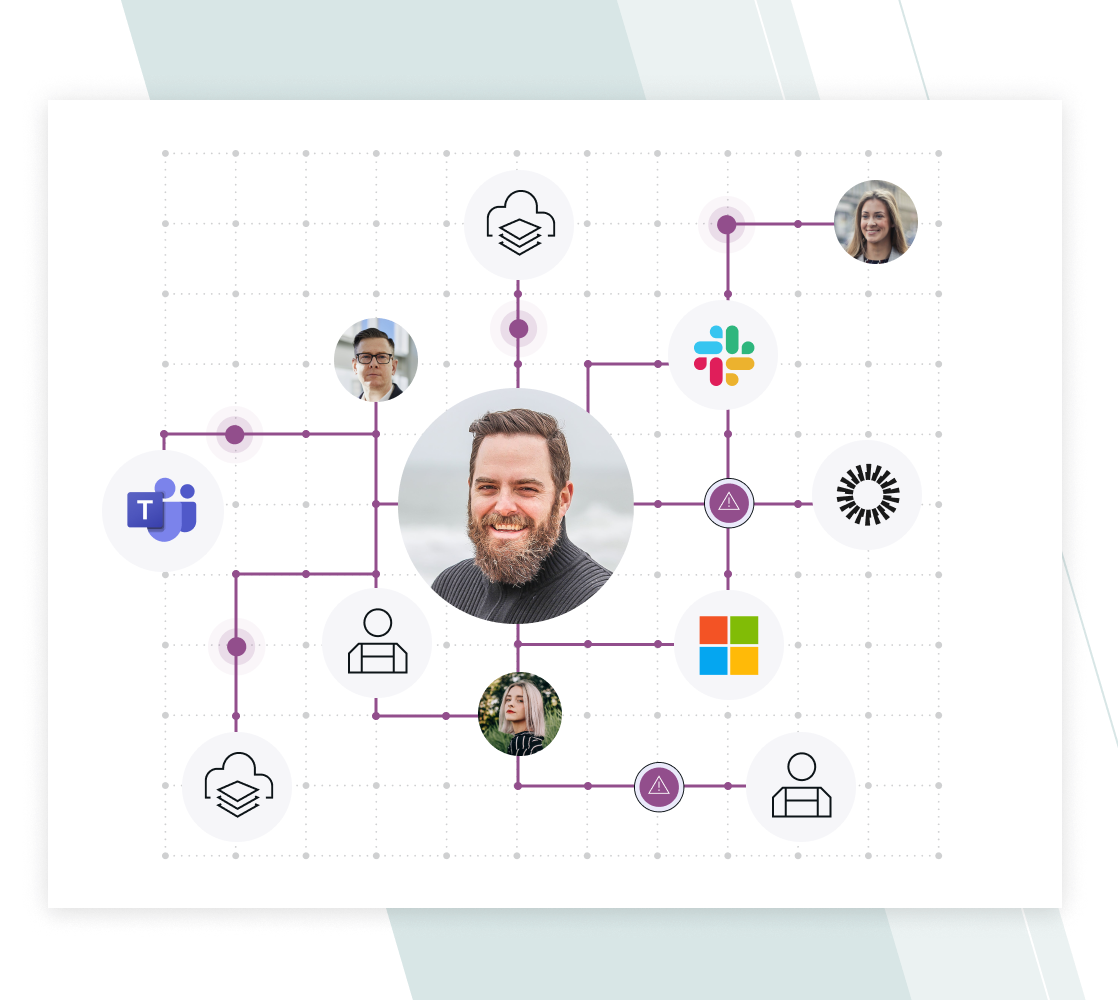
Ingest
Diverse Data Leads to Better Human Understanding
- Uses 10x more behavioral signals across multiple platforms, including identity-centric signals and telemetry from email and messaging apps.
- Models human behavior to deeply understand every employee and vendor.
- Knows the context of business communications, relationships, and processes.
Learn About Abnormal AI
Detect
Behavioral AI Precisely Detects and Stops Attacks
- Analyzes email content from a human lens using computer vision, Natural Language Processing/Understanding.
- Compares personal behaviors relative to historic patterns for every user to detect anomalies, stop attacks, and remediate compromised accounts.
- Continuously evaluates risk within the context of notable account activity to provide ongoing protection.
Discover Our Detection Models
Remediate
Multi-Dimensional Defense Extends Protection and Visibility
- Multi-channel security extends beyond traditional detection across internal, external, and chat messages to ensure comprehensive protection.
- Multi-layered defense for posture management plus autonomous account takeover detection and response provide a holistic security solution that is both broad in scope and deep in its understanding of human behavior.
- Multi-platform protection applies consistent visibility and controls across cloud platforms to ensure security measures are applied universally.
Multiply Your Defense

Abnormal, because of the way they use API and cloud security, was able to look at our entire environment within five minutes. We started getting actionable intelligence within 24 hours, and Abnormal allowed us to see where the specific and targeted attacks were. We weren’t able to see that before.”
— George Insko, CISO at Rubicon
Read Case Study
Frequently Asked Questions
Learn More About AI
Discover the Latest Abnormal AI Insights
See the Abnormal Solution to Email Security
Abnormal's API-based architecture helps you protect more while spending less.Request a Demo
See a Demo




