Abnormal + Google Workspace
Protect against sophisticated socially engineered email attacks and complement native Gmail security.
See a Demo
Leader in Gartner® MQ
PROBLEM
An Increasingly Complex Threat Landscape
Subheading text goes here
$137K
average lost per business email compromise attack.
average lost per business email compromise attack.
Source: 2022 FBI IC3 Report
26%
of companies are targeted by account takeover attempts each week.
of companies are targeted by account takeover attempts each week.
Source: Abnormal Security
$4.45M
lost in the average breach tied to cloud misconfigurations.
lost in the average breach tied to cloud misconfigurations.
Source: IBM Cost of a Data Breach Reportt
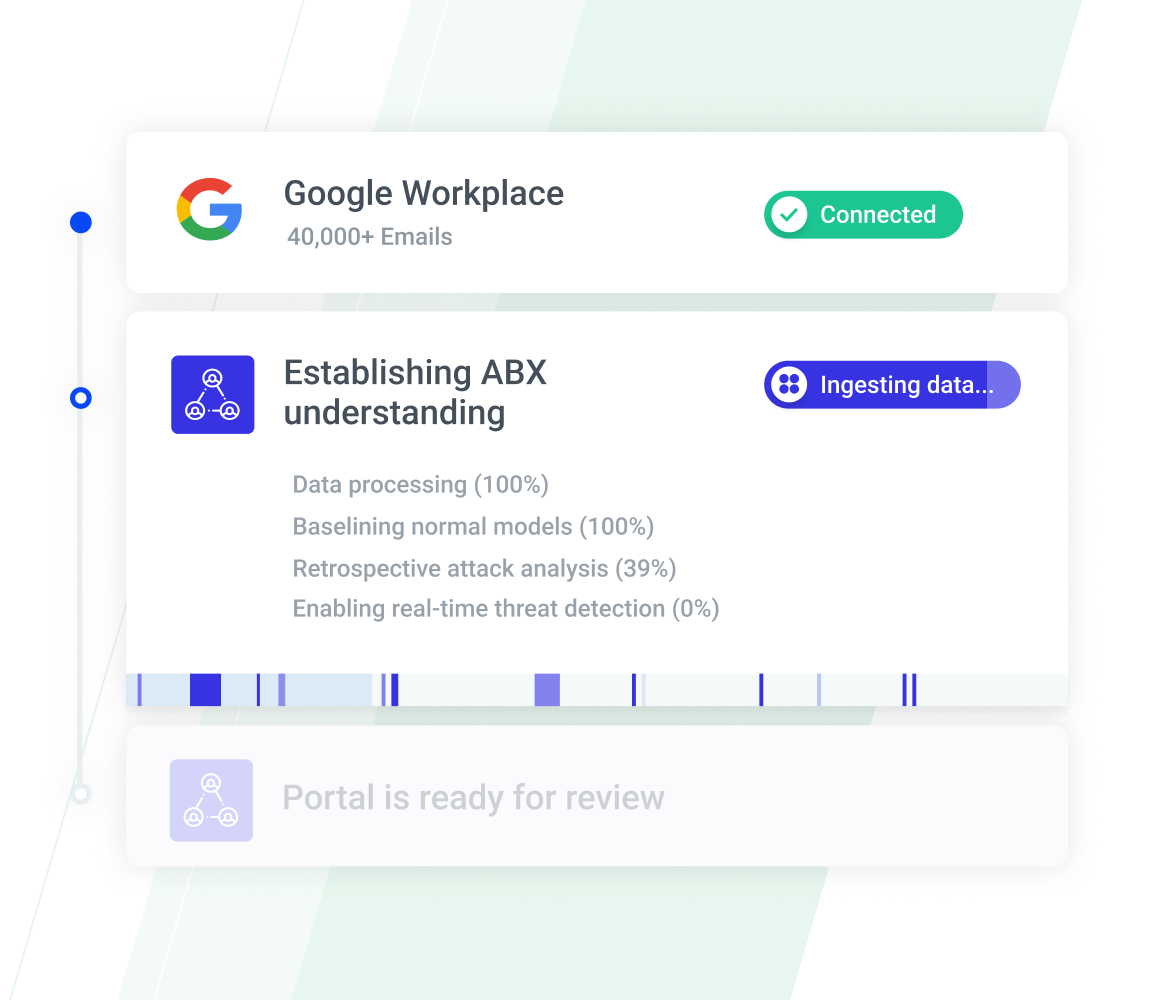
API-Based, AI-Native Protection for Google
Speeds Up Time to Value
Integrate and deploy in minutes with the API-based, cloud-native architecture to start ingesting thousands of behavior signals. There is no need to change configurations or set customer policies and no disruption to email flow.
Discover the Architecture
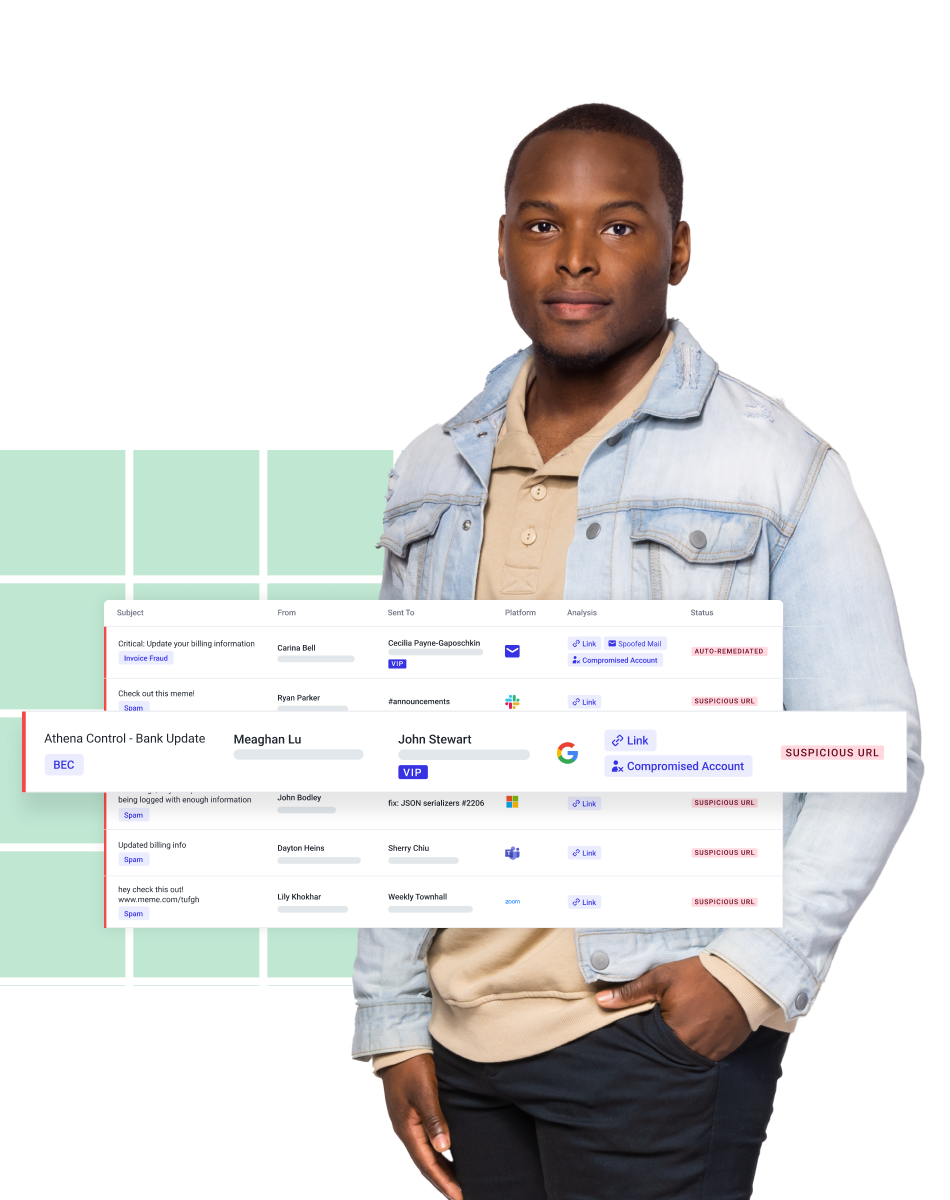
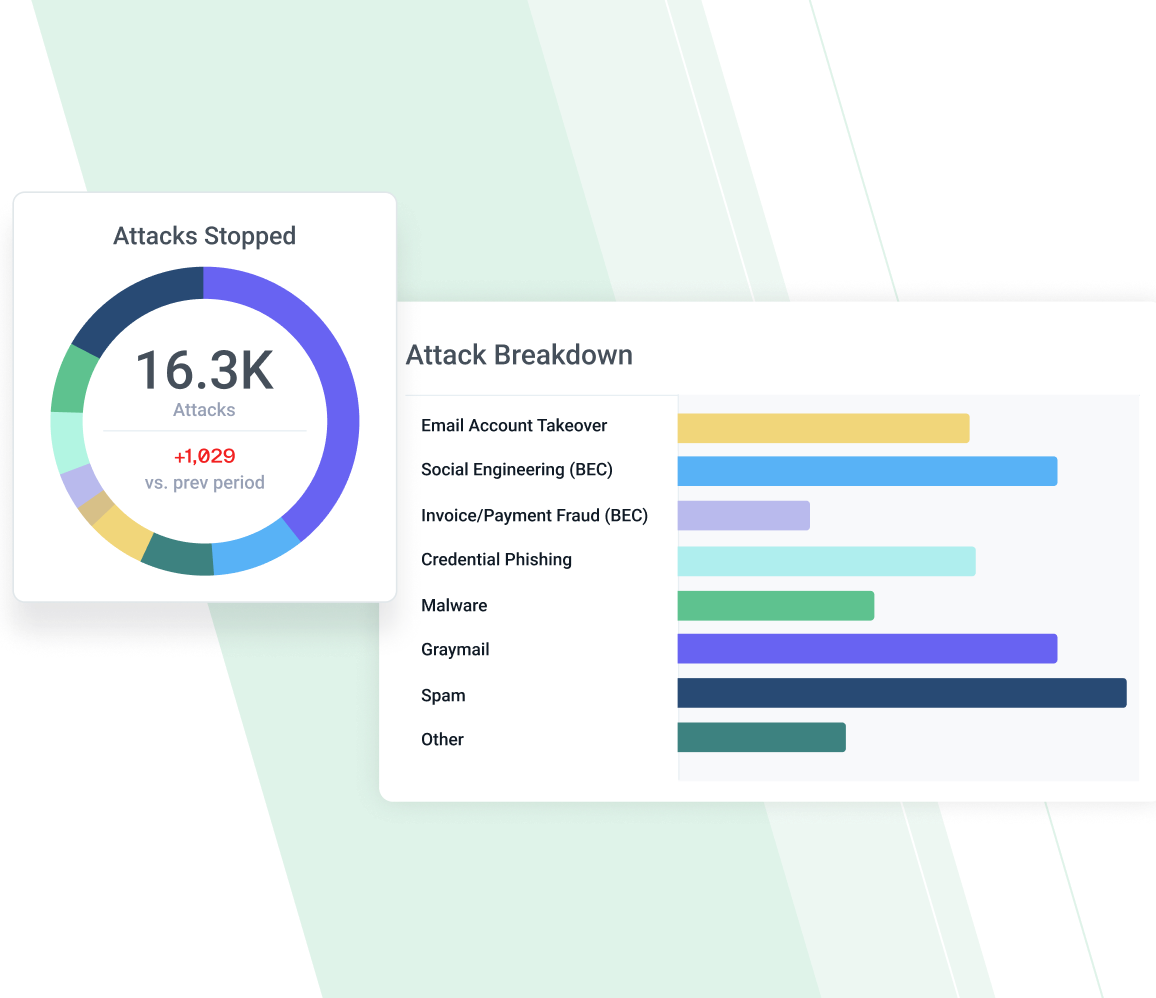
Blocks Sophisticated Email Attacks
Stop all types of malicious email, including business email compromise, account takeovers, and email supply chain attacks, using Abnormal Human Behavior AI to understand what’s normal and stop anything anomalous.
Get Inbound Email Security
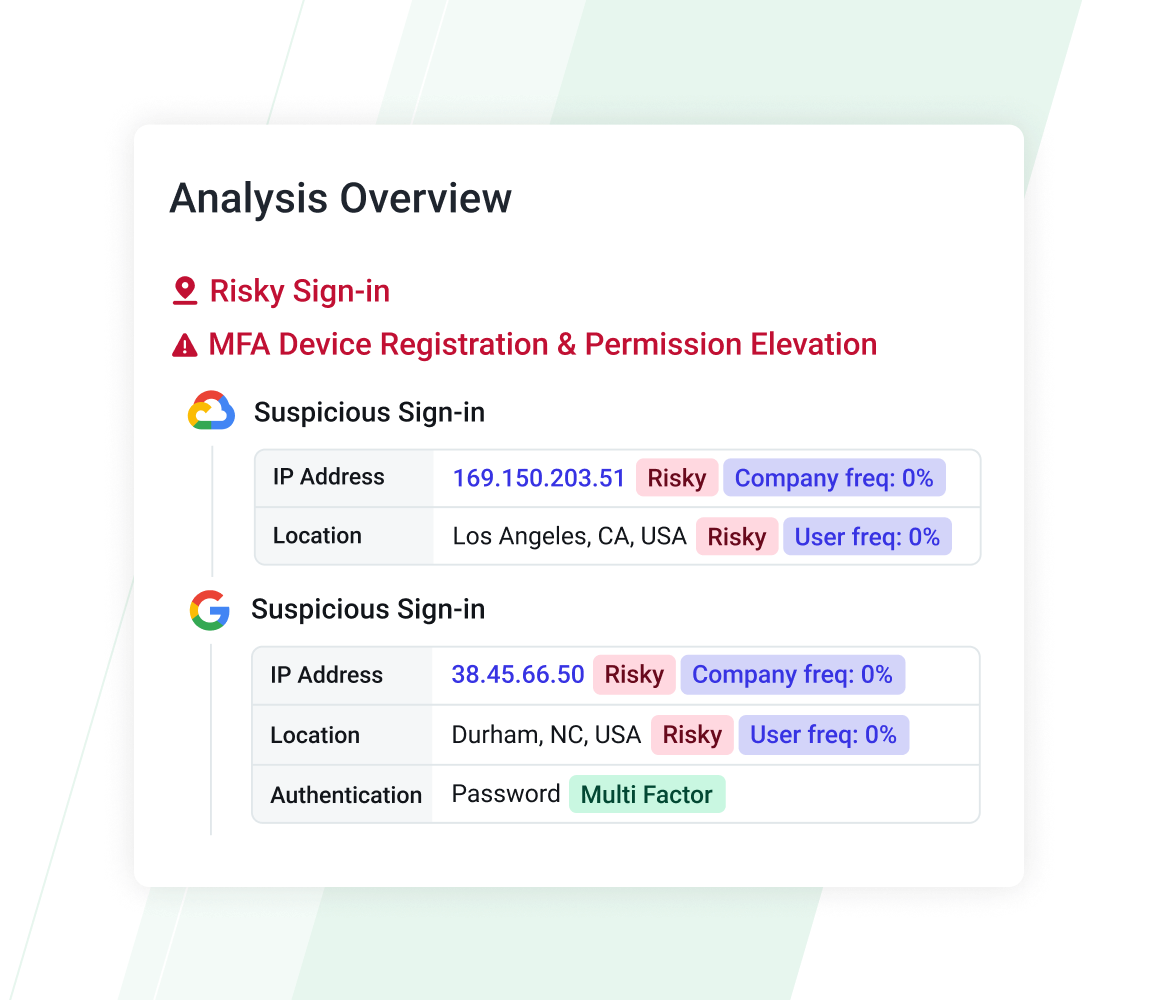
Identifies Account Takeovers
Precisely detect identity takeover attempts across the Google ecosystem, including Google Drive and Google Cloud Platform, with behavioral AI that understands every person in the organization and continuously monitors for abnormal activity to stop attacks.
Stop Account Takeovers
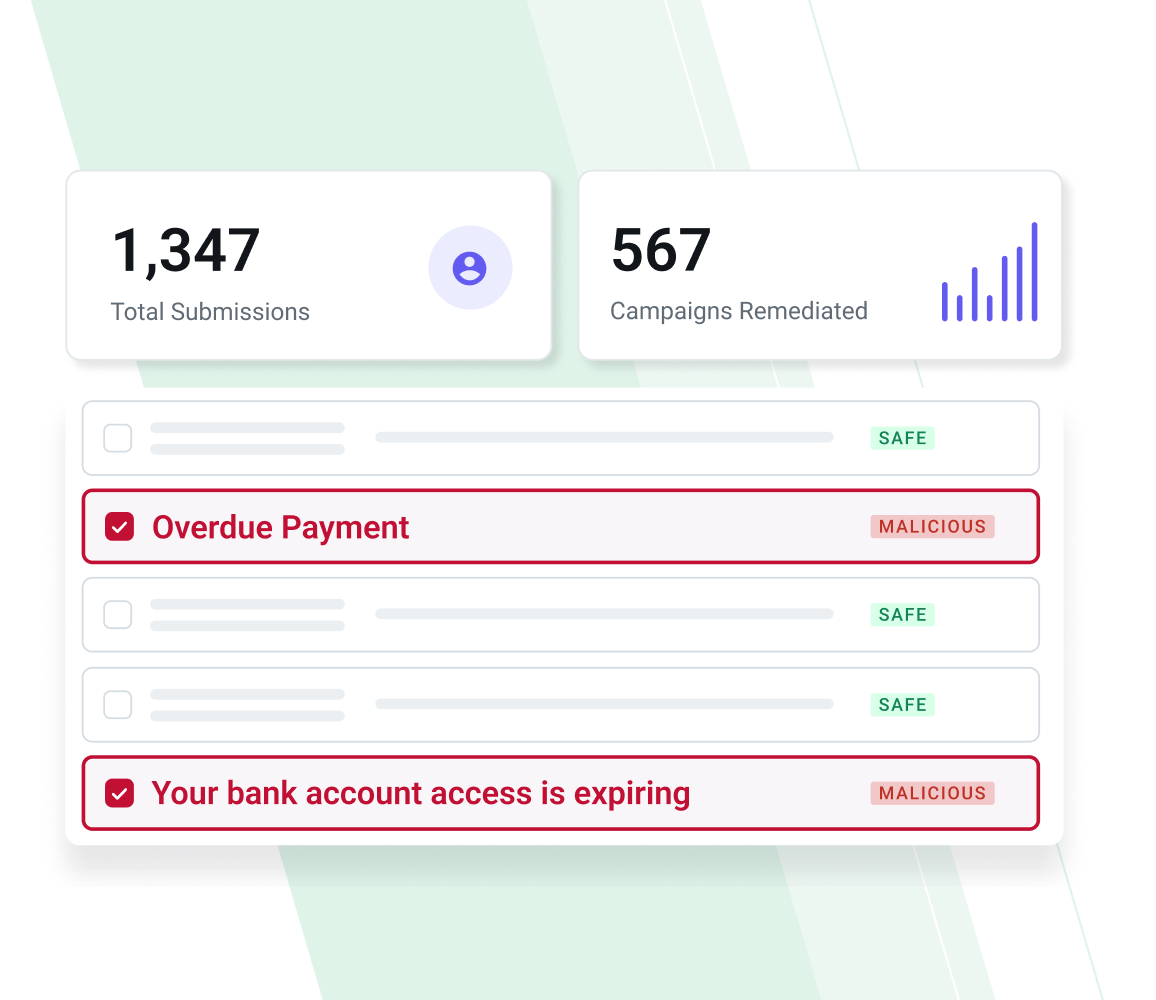
Automates SOC Operations
Save time using AI to automatically triage and remediate user-reported emails and remove related emails associated with the same phishing campaign from all inboxes. Conversational AI responses to user-reported mail provides real-time security training and improves the employee experience.
See AI Security Mailbox
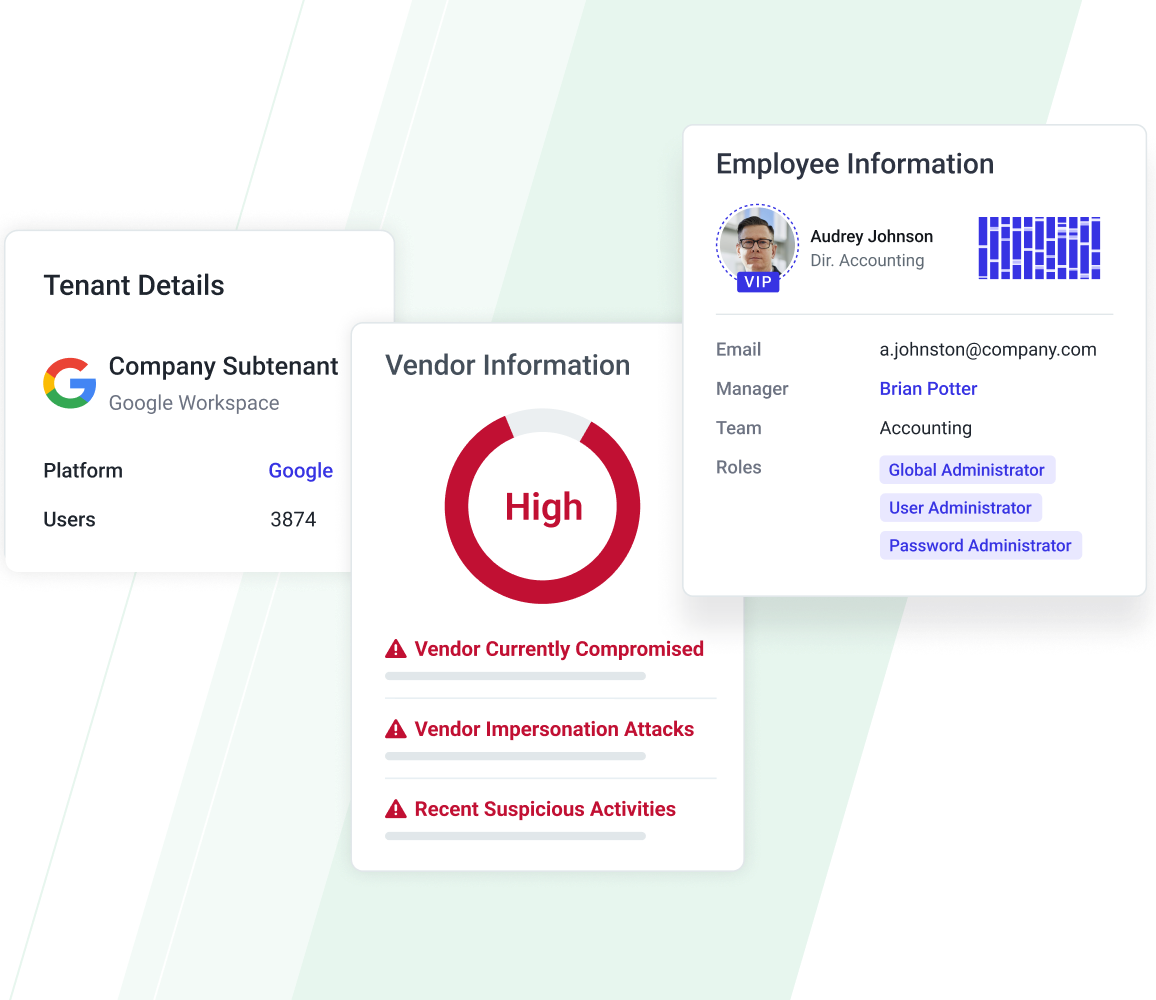
Improves Your Security Visibility
See federated behavioral accounts of people, vendors, threat intelligence, apps, and tenants to help security teams better understand risk and investigate threats within their environment.
Uncover Your Email Security Risk
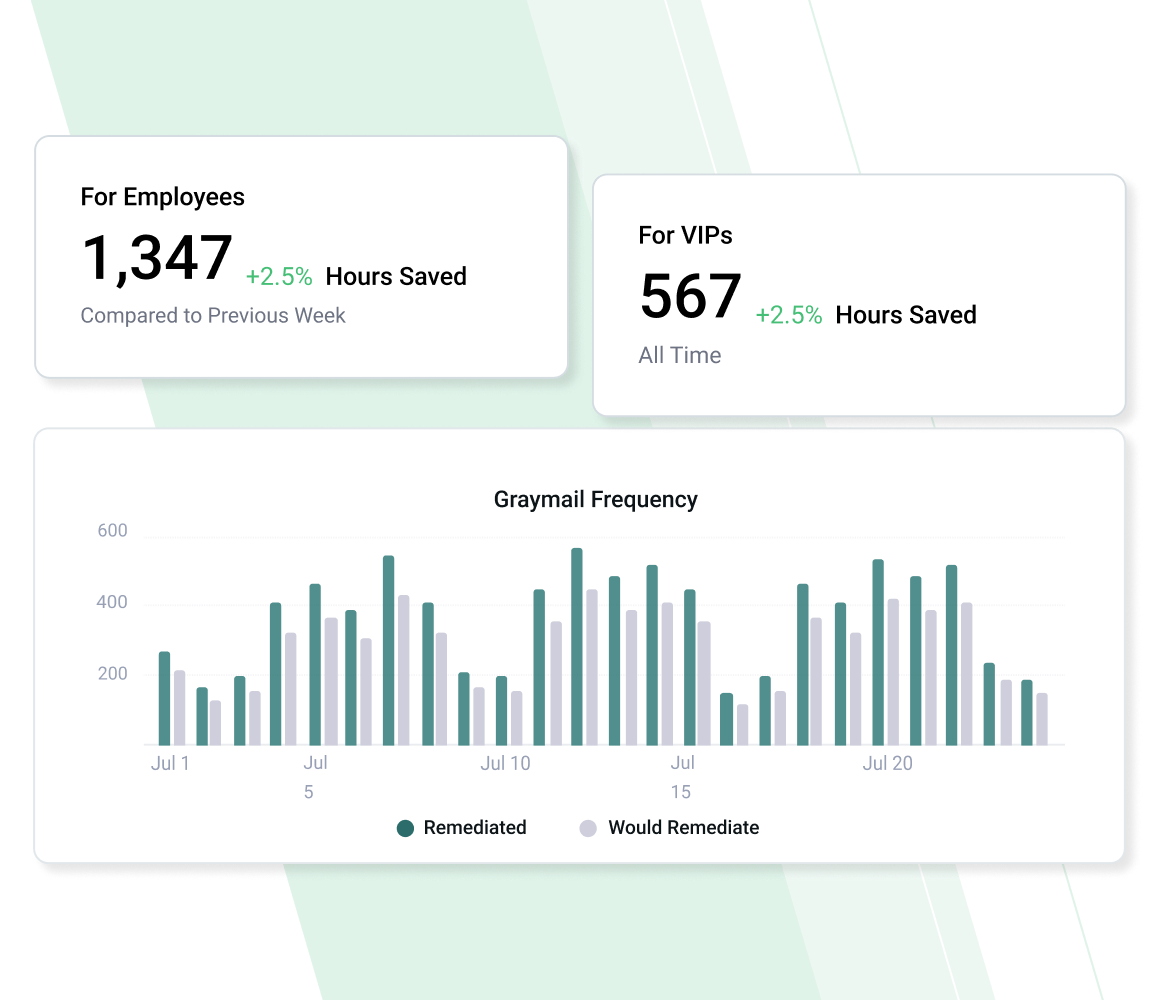
Detects and Remediates Graymail
Personalize unwanted mail sorting for each employee using self-learning AI to precisely and adaptively move messages from employees’ inboxes to a designated graymail label. This personalized approach eliminates end-user digest emails or quarantine portals and leads to quantifiable time-savings.
Uncover Email Productivity
Comprehensive Security for Google
Detect Advanced Attacks
Stop threats your SEG misses, including AI generated and hyper-personalized socially engineered attacks.
Improve Security Posture
Identify high-impact, high-risk activities across users, applications, tenants, and vendors.
Connect & Protect Fast
Integrate and onboard quickly, with minimal ongoing management overhead and a native Outlook experience.
Prior to turning on Abnormal, attackers would create one Gmail address after another to impersonate familiar people—our superintendent, principals, and teachers. We couldn't do much about those attacks before. We have a Google Workspace instance that we use for students, so we couldn't block Gmail addresses. With Abnormal, it catches those impersonation emails automatically, so we don’t have to spend time responding to those threats manually.”
— Shane Snedecor, Information Security Manager,
Virginia Beach City Public Schools
Frequently Asked Questions
Related Resources
Augment Google Workspace with Human Behavior AI Understanding
Protect your organization's Google accounts and applications from attacks targeting your people.
Request a Demo
Request a Demo