AI Security
Mailbox
Your AI coworker for email security operations.
Watch a Demo
See the Product Tour
PROBLEM
Security Teams are Operationally Burdened
Subheading text goes here
Time-Consuming Operations
An endless queue of employee-reported emails requires manual triaging which diverts resources from other key priorities.
Security Awareness
Current tools prohibit the delivery of customized and targeted security coaching for every employee and efforts to personalize training are tedious.
Security Team Fatigue
CISOs need AI to enhance resource efficiency and optimize security workflows to mitigate burnout.
How Abnormal Enhances Security Operations
AI Coworker for the Security Operations team
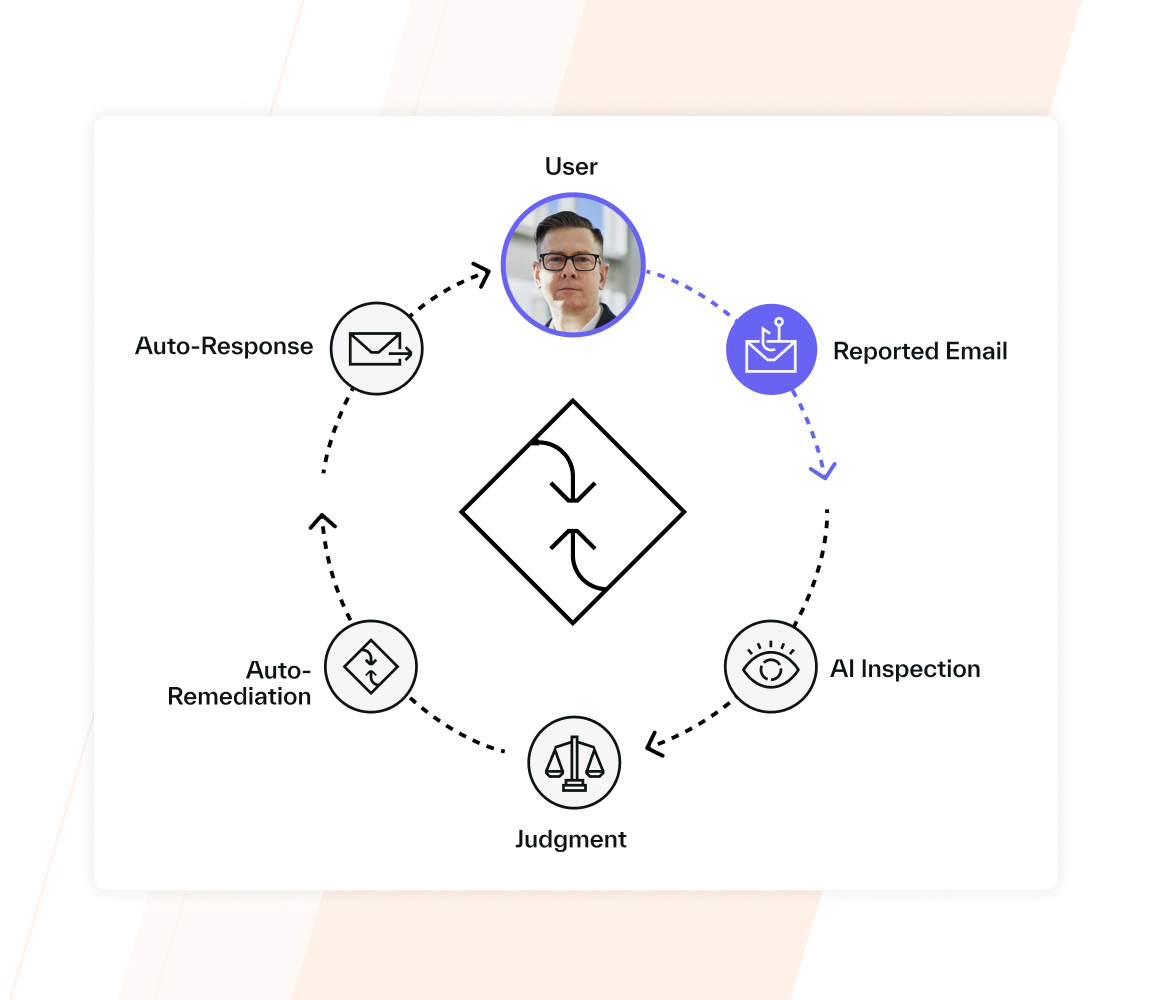
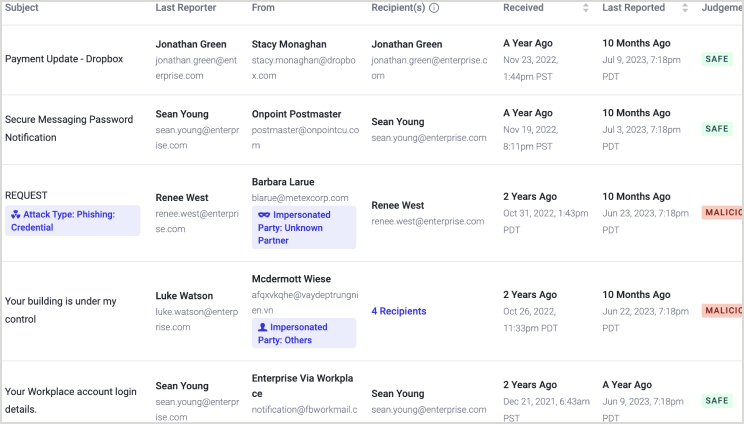
Abnormal AI provides 24/7 AI triage to autonomously inspect and judge user-reported emails as malicious, spam, safe, or a phishing simulation. If an email is found malicious or spam, AI Security Mailbox provides AI-assisted investigation, identifies similar messages across all mailboxes, tracks email engagement and can bulk-remediate messages across multiple tenants.
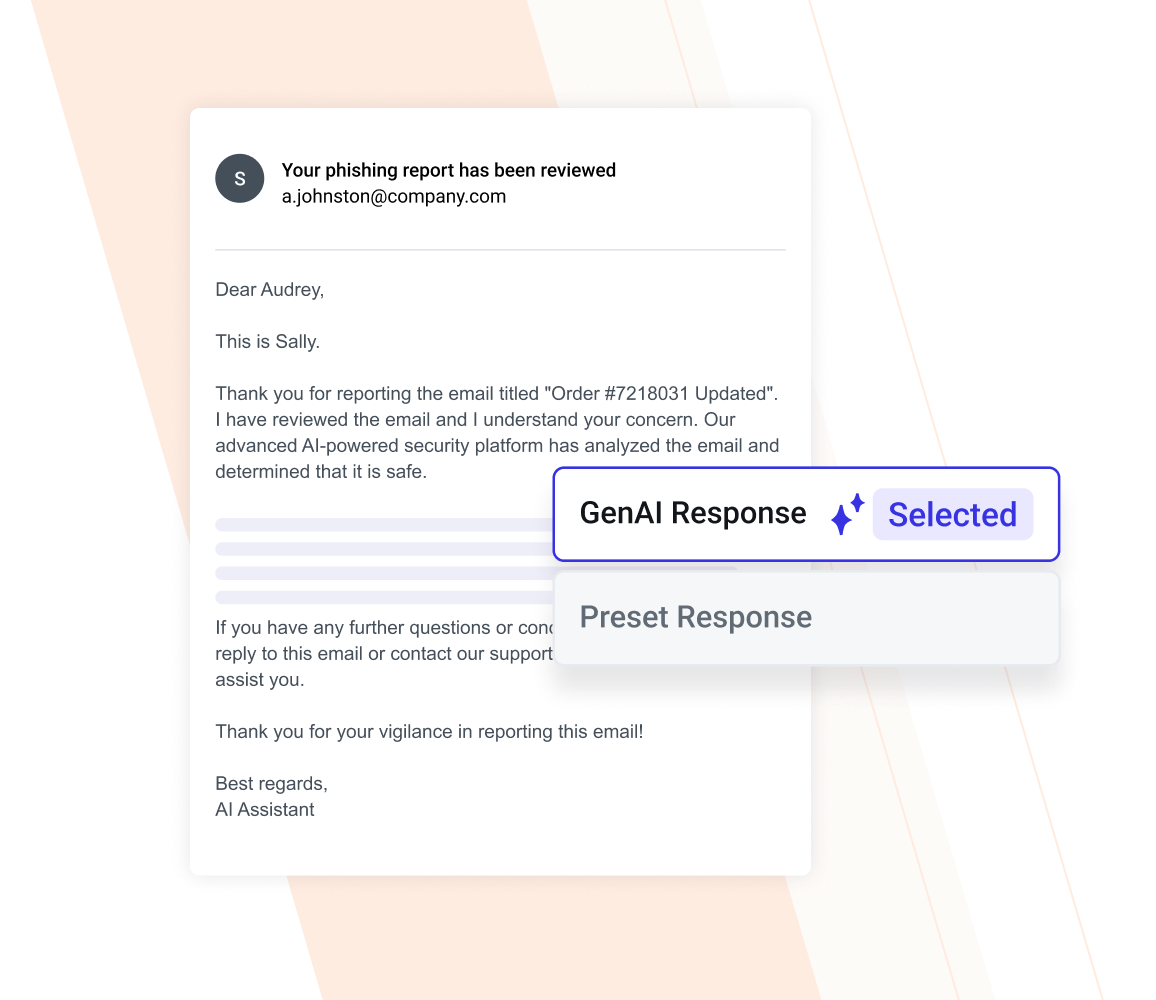
Personal AI Cyber Assistant for Every Employee
AI Security Mailbox automatically responds to every employee-reported email, providing remediation action and detailed explanations on whether the email was safe or malicious. It comes pre-trained with enterprise security best practices, specifically tailored to your environment. Employees can also ask follow-up or other security-related questions. It offers a delightful and helpful experience that elevates your security brand.
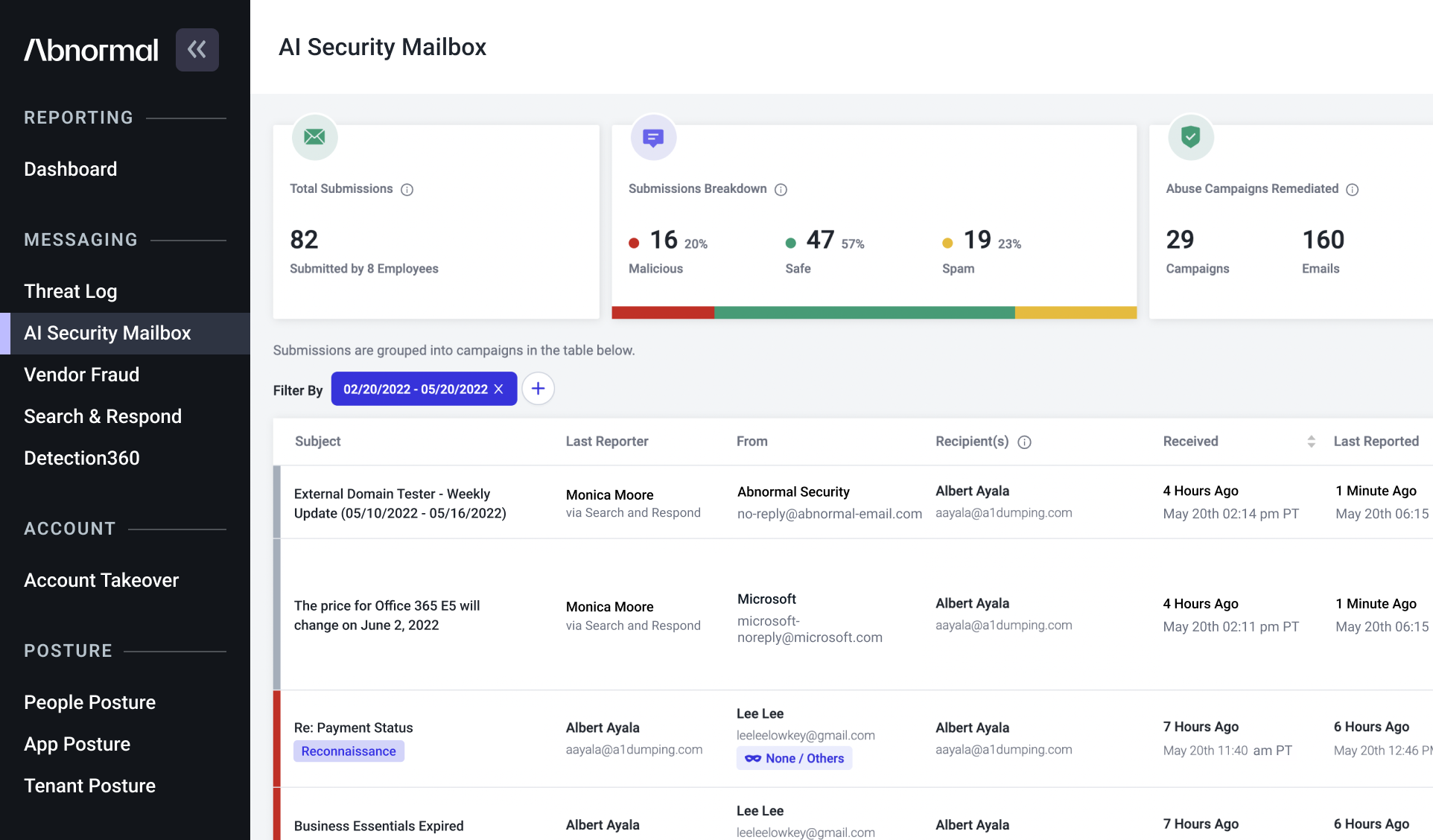
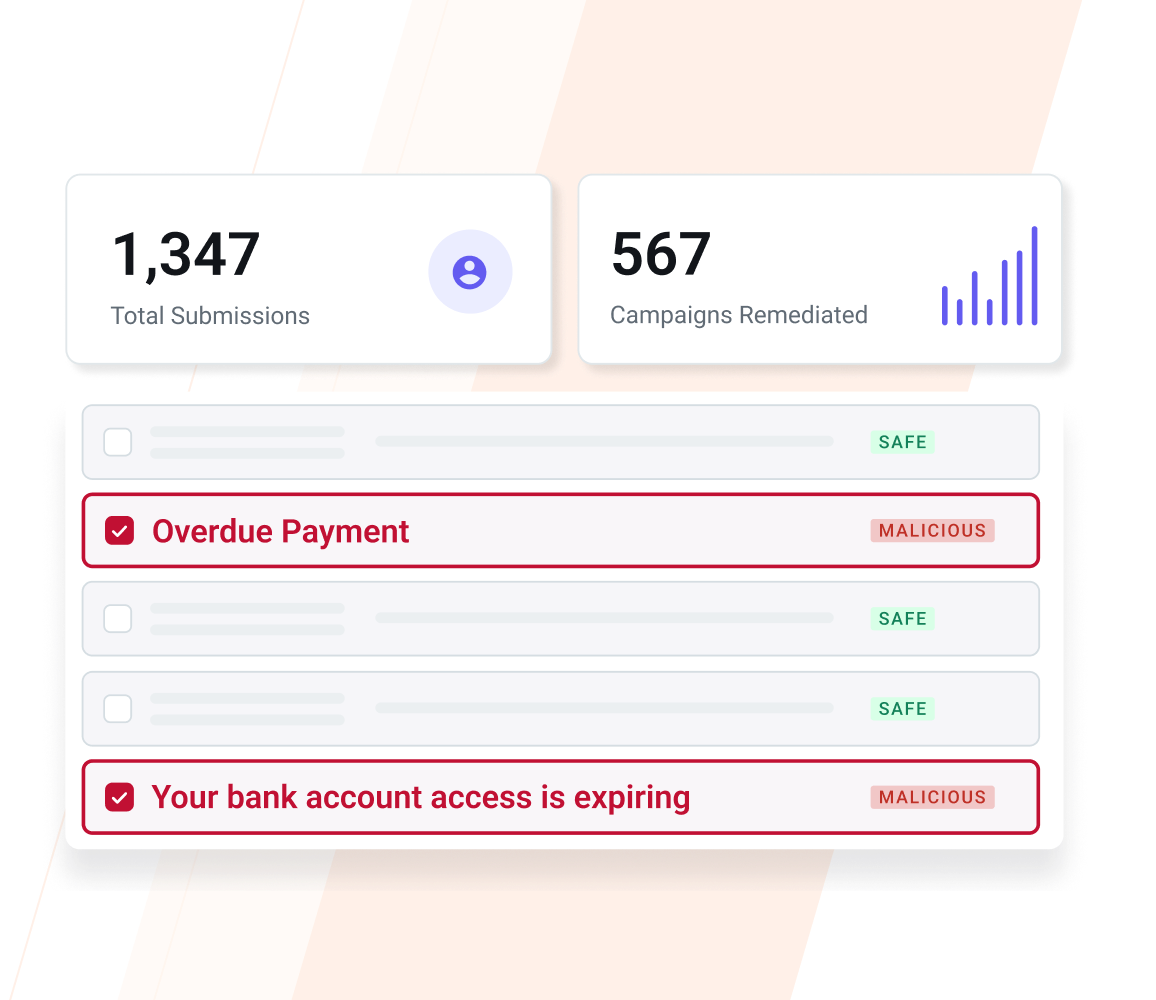
Centralize Visibility and Reporting of User-Reported Emails
AI organizes all user-reported emails into a consolidated view and provides full visibility into each submission. Administrators can see the full attack context for each campaign and every email.
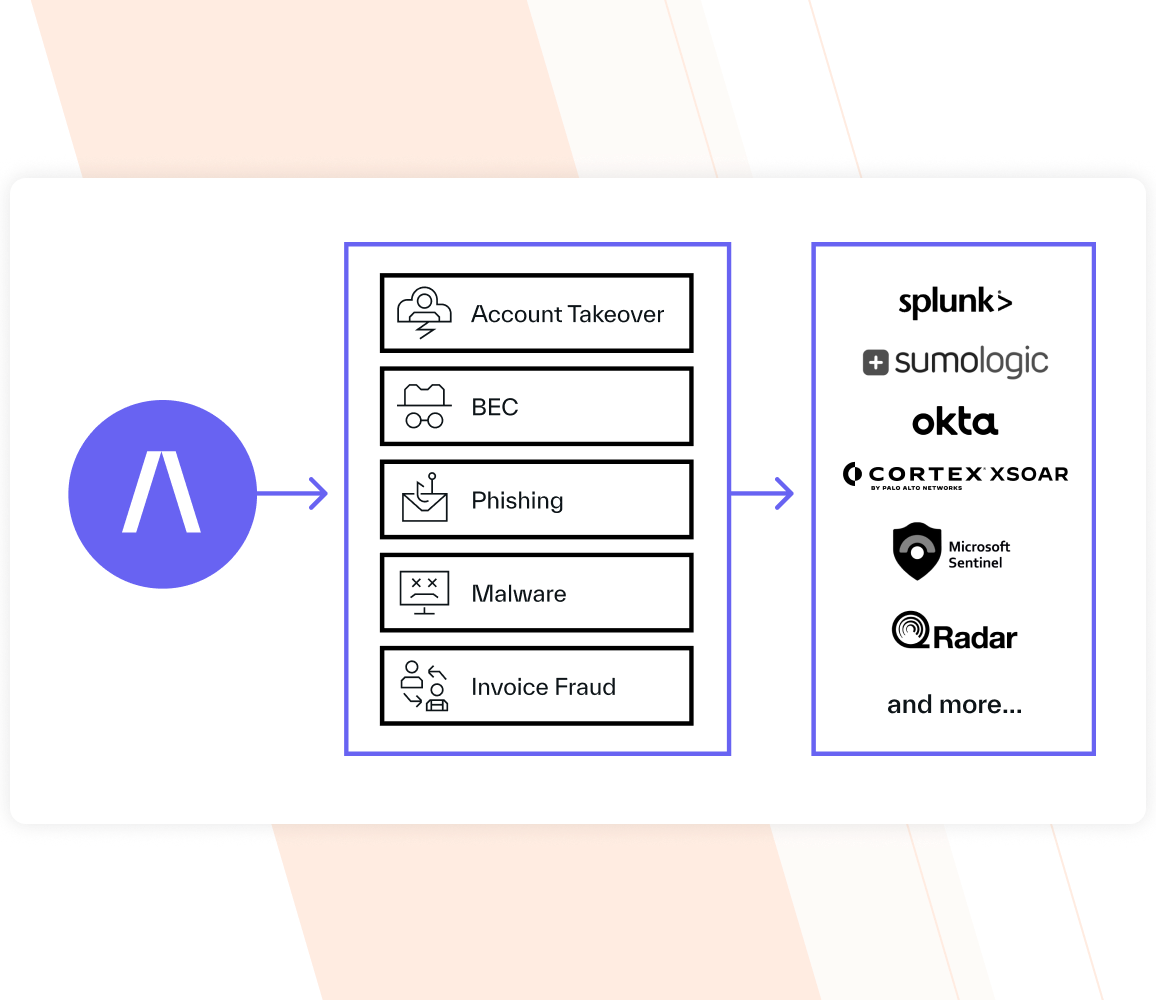
Integrate with Existing Workflows and SIEM/SOAR Solutions
Abnormal integrates with existing end-user phishing reporting buttons, SIEM/SOAR solutions, and ticketing system workflows to enable centralized alerts for SOC analysts.
See How AI Security Mailbox Works
Campaign Remediation
Inspects and evaluates user-reported emails. If malicious, removes other unreported emails within the same campaign.
AI-Powered Conversational Mailbox
Automated responses to inform reporters. Chooses from preset templates or enrich responses with
generative AI.
AI Security Analyst
Security teams can customize and chat with the AI Security Analyst to see how it interacts with employees.
We’ve heard feedback from our users that report potential spam, and they appreciate the timely feedback that Abnormal delivers.”
— Mike Freeman, Cybersecurity Manager at Sentara Healthcare
Related Resources
Accelerate Security Operations with AI Security Mailbox
Learn how you can empower analysts while keeping employees informed, engaged, and delighted with your new AI coworker.
Request a Demo
See a Demo