SaaSAccount Takeover Protection
Stop account takeovers in your SaaS apps with
autonomous AI.
See a Demo
PROBLEM
Cloud Breaches are on the Rise and Hard to Stop
Subheading text goes here
Evolved Threats
Evolved Threats
Malicious AI and sophisticated social engineering make compromising cloud accounts easier than ever.
Limited Visibility
Limited Visibility
Security teams lack the continuous oversight needed to validate identities across a vast and interconnected cloud ecosystem.
Ineffective Tools
Ineffective Tools
86% of security teams report current solutions are inefficient against account takeovers, leaving a critical gap in cloud security.
How Abnormal Dynamically Detects SaaS Account Compromise
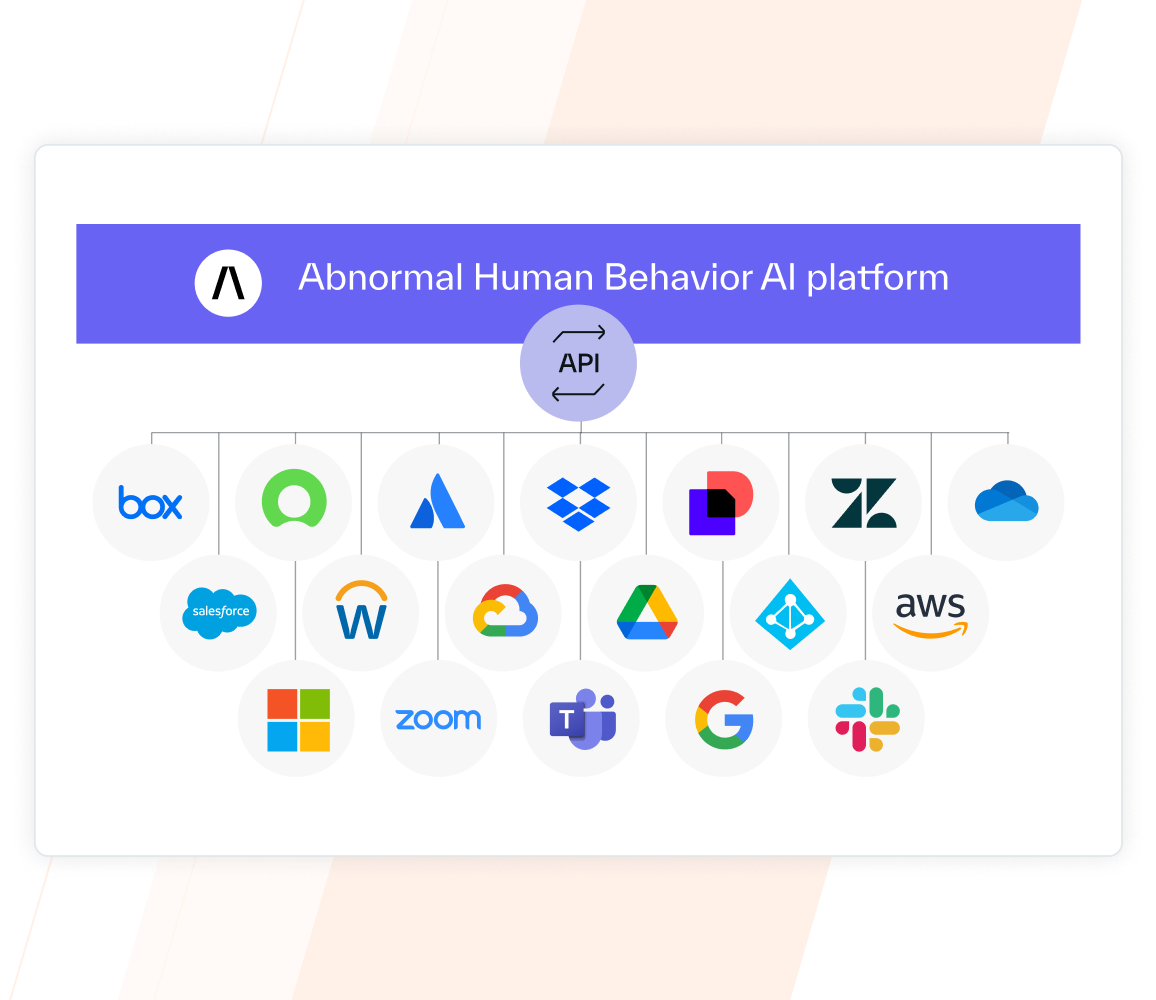
Centralizes Security Visibility Across the SaaS Environment
Cloud-native API architecture centralizes cloud visibility by enabling simple integration to any SaaS app in under five minutes with only a few clicks. Simple integration, an easily scalable platform, and automatic learning means minimal SOC overhead and little manual effort.
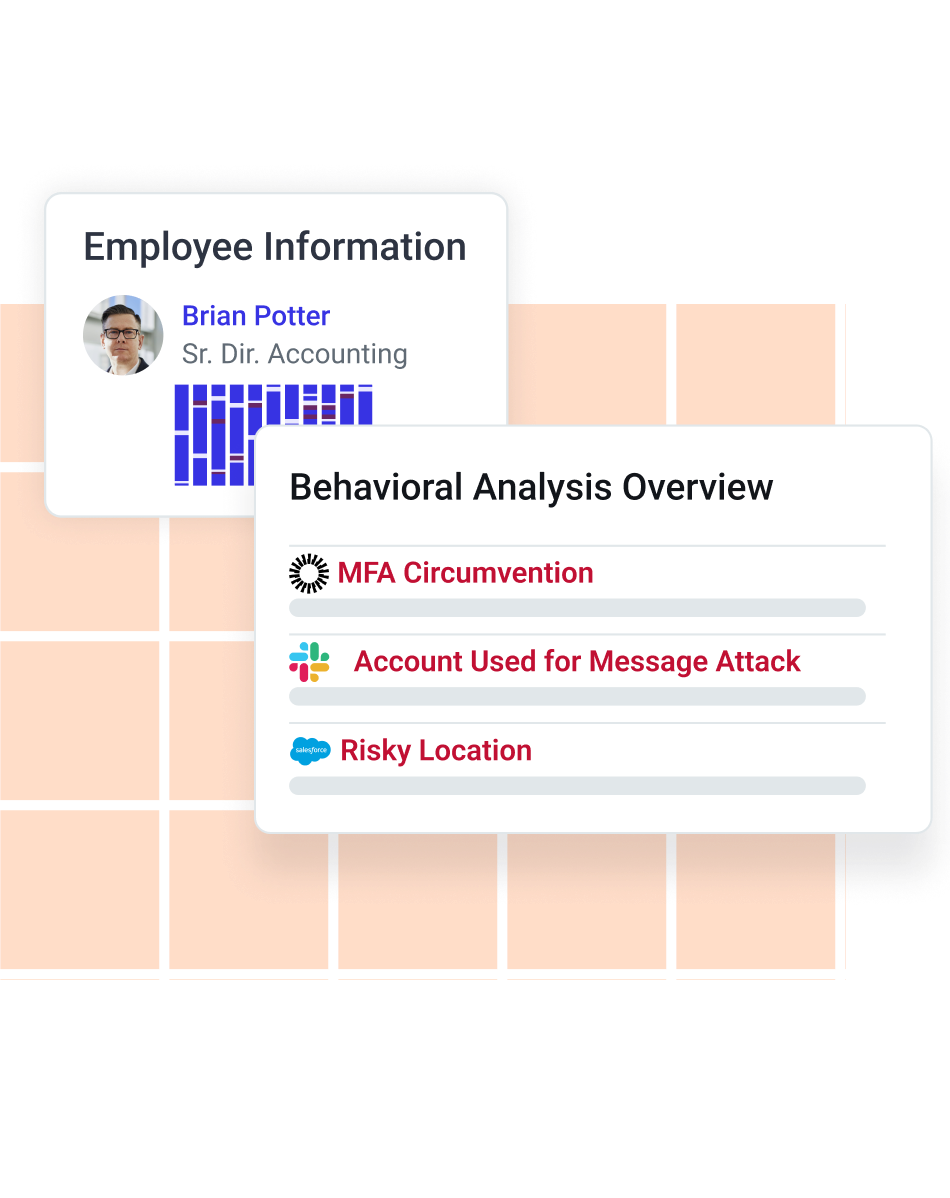
Builds a Behavioral Baseline for Humans via AI
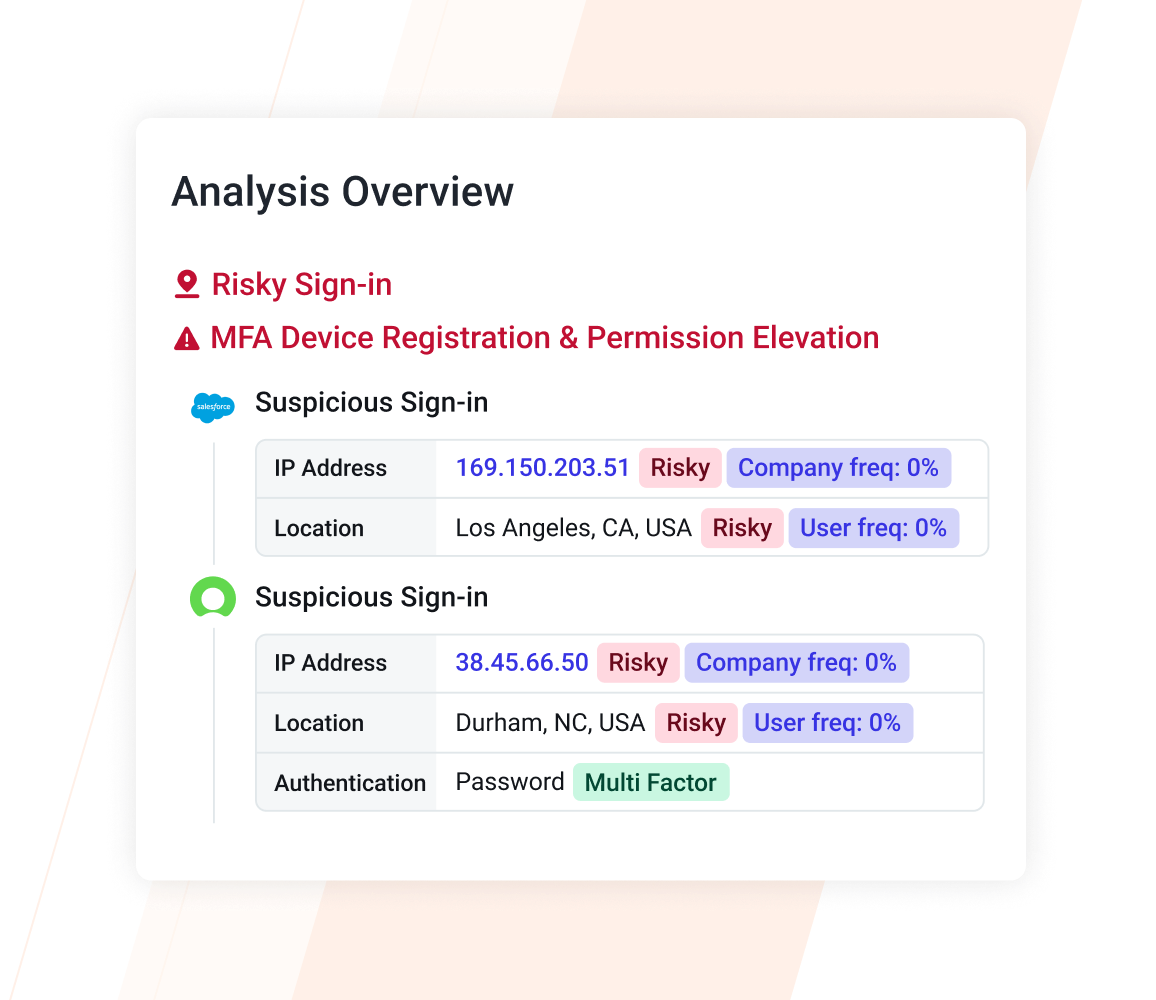
Human behavior AI automatically monitors authentication signals, communications, and notable activity, such as unusual locations, IPs, or VPNs or new MFA device registrations, across all integrated platforms—enhancing behavioral models without the need for rule or policy creation. Abnormal bases detection and analysis off of the dynamic behavioral baseline built for each user, rather than predefined rules and detections.
Detects and Remediates Cross-Platform Account Compromise with Autonomous AI
Abnormal automatically identifies compromised identities, generating a contextual behavioral case timeline to enable investigation of notable events.
Delivers AI-Powered Unified Account Takeover Protection
Account Takeover Protection automates remediation, immediately terminating sessions and revoking account access across cloud entities once an account takeover is confirmed, massively reducing the time spent responding to account takeover incidents.
Account Takeover Protection Features
ThreatIntelBase
Surface and aggregate behaviorally-derived threat intelligence to improve threat hunting and incident response efforts and streamline SOC processes.
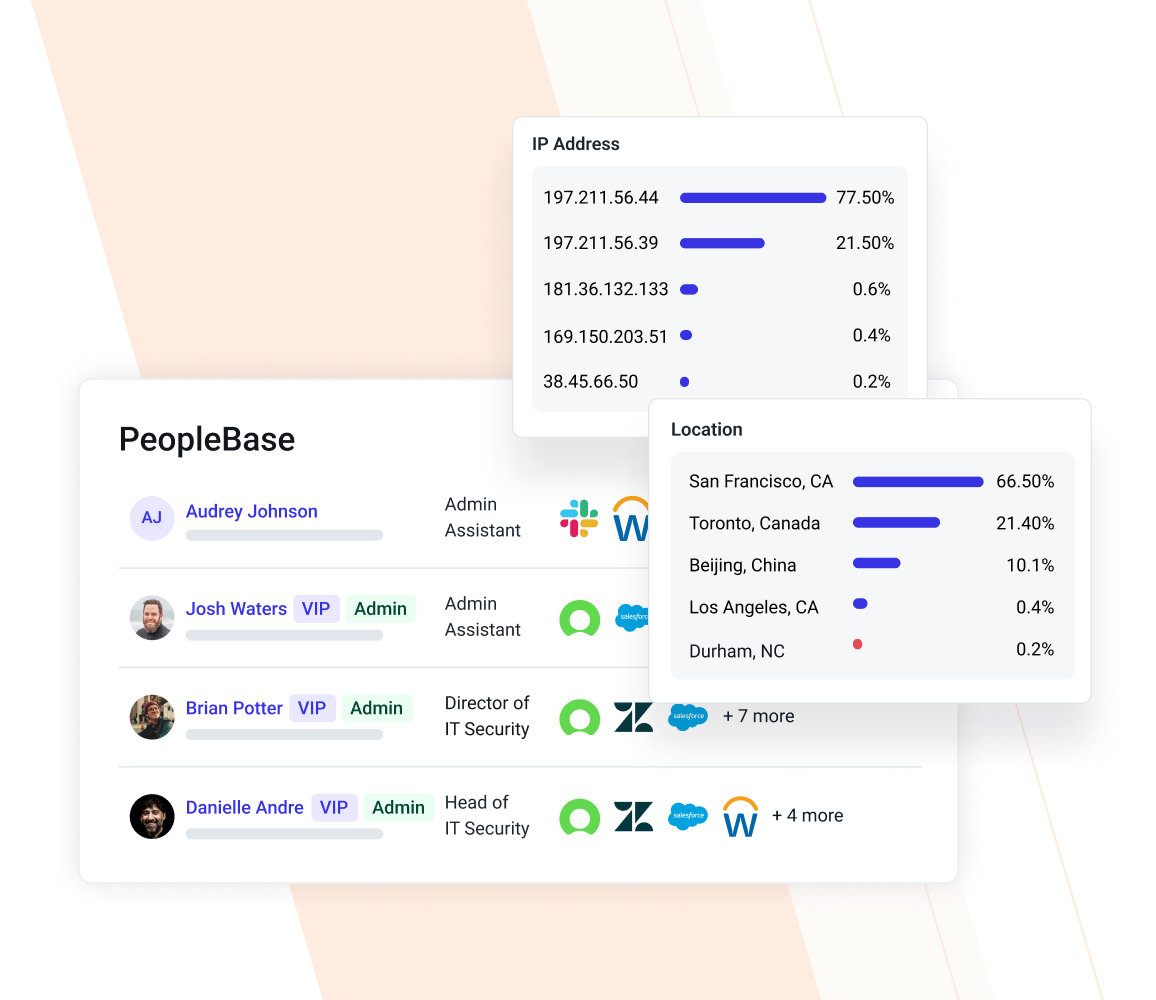
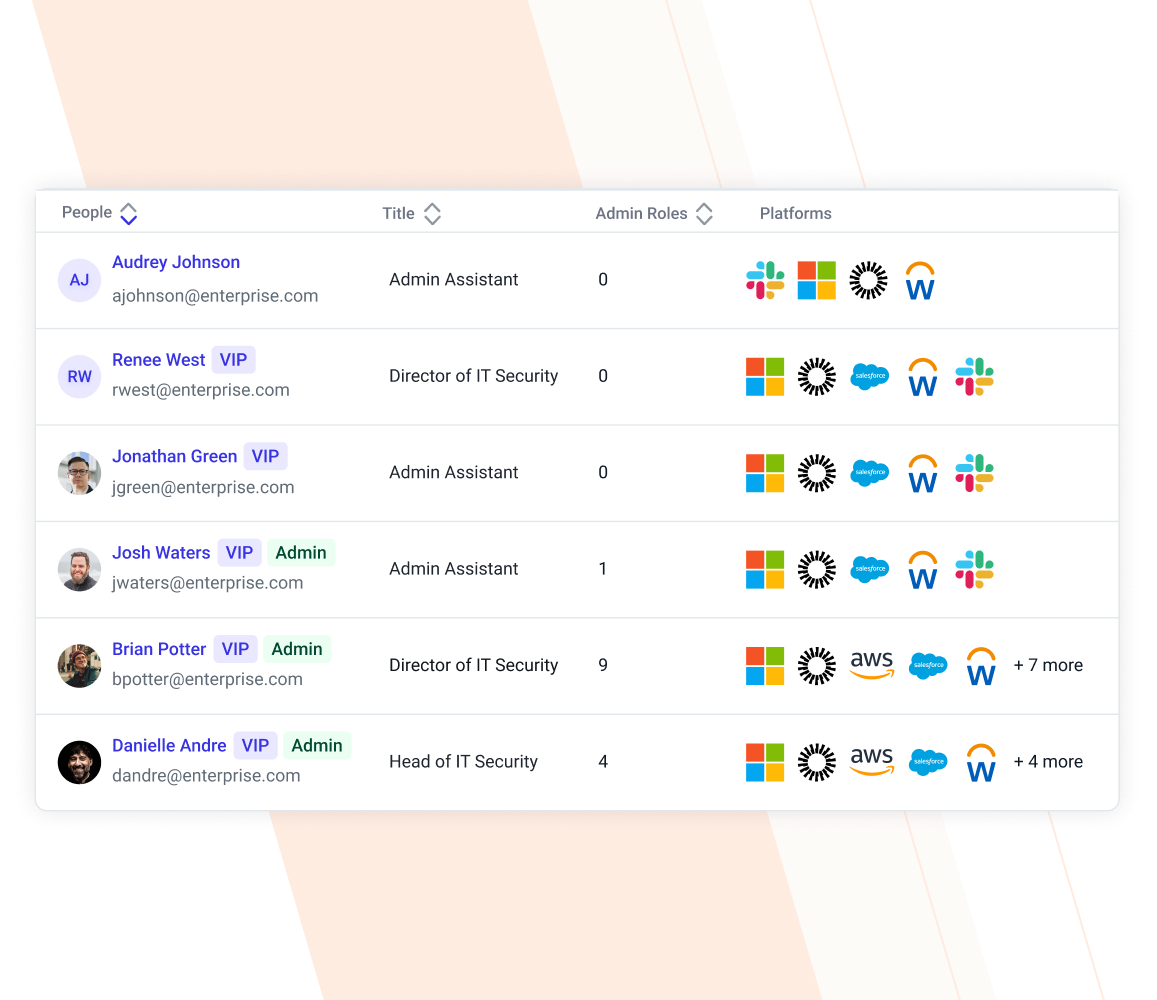
PeopleBase
Gain visibility into cross-application privileges, derived insights from Abnormal AI, and a cross-platform identity timeline of notable events for every employee.
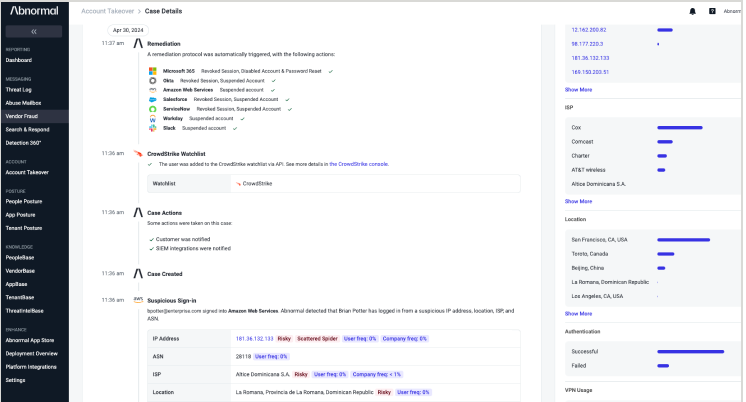
Behavioral Case Timeline
View a contextual timeline of suspicious human behavior that rolls up cross–cloud user activity into a singular Abnormal Behavior Case Timeline.
When we first started looking, Abnormal’s API-based approach really interested us. Abnormal also offered automation capabilities that could reduce the amount of manual work we had to do on investigations and remediation.”
—Jeremy Smith, CISO, Avery Dennison
Related Resources
Detect, Disable, and Remediate Compromised Accounts
Catch account takeover attempts that other solutions miss with human behavior AI.
Request a Demo
See a Demo









