Abnormal for Amazon Web Services
Analyze human behavior across your AWS environment.
See a Demo

PROBLEM
Navigating the Threats to AWS
Subheading text goes here
Attackers Are Targeting AWS Credentials
With over 100 trillion objects stored in AWS environments, sophisticated threat groups aim to compromise user accounts and steal sensitive data.
Security Teams Lack Visibility into AWS
AWS environments, hosting hundreds of containers and DBs like ECS and Aurora, can be highly complex and owned by a variety of different teams within the organization, which limits security’s visibility.
Traditional Solutions
Fall Short
Traditional Solutions
Fall Short
Even with strong native security offered through AWS GuardDuty, 86% of security leaders feel they do not have sufficient tools to stop threats like account compromise in the cloud.
How Abnormal Secures AWS
Gain Visibility Across the Entire AWS Environment
Abnormal leverages API connectivity to AWS Cloudtrail to ingest and synthesize sign-in event data across the entire AWS environment—from Lambda to S3. The solution applies human behavior AI to establish a behavioral baseline and identify irregularities, ensuring continuous protection.

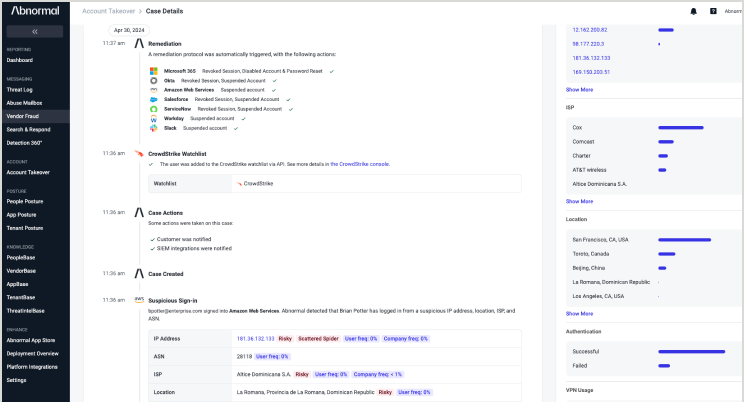
Detect Threats to AWS DBs, Containers, and Other Services
Your AWS environment houses some of your most critical assets and infrastructure. When suspicious behavioral deviations are detected, Abnormal’s Human Behavior AI automatically triggers and builds a contextual timeline of user activity that includes suspicious cross-AWS events, correlating against cross-platform behavior that also spans email, cloud, and SaaS applications to bolster detection confidence and support investigation—ensuring the SOC team can immediately investigate.

Simple, Effective Security for AWS
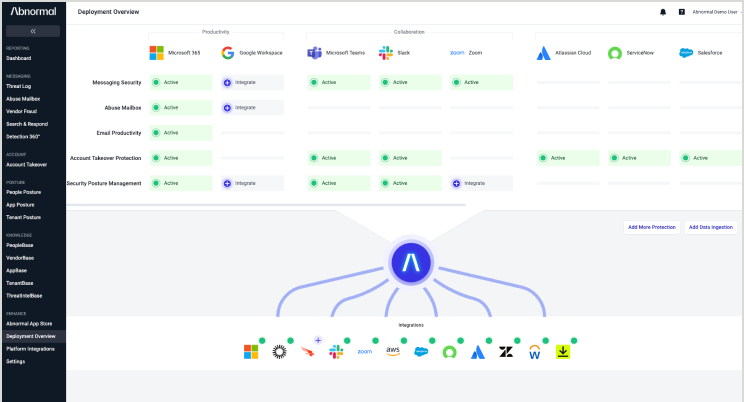
Data Integration Platform
Easily integrate and ingest behavioral signals from multiple cloud applications and services, including AWS, with a cloud-native API architecture.
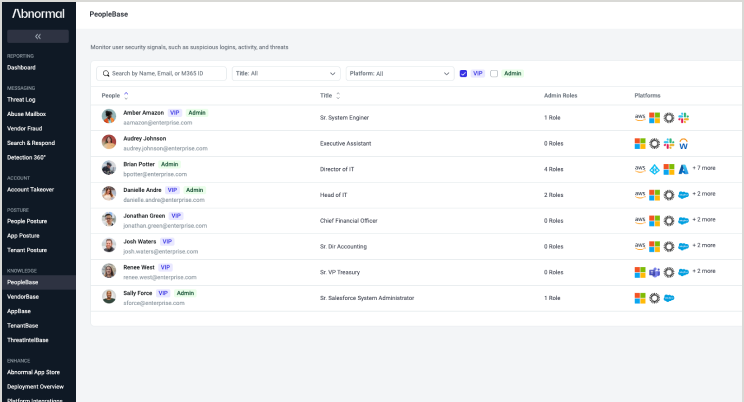
PeopleBase
Explore sign-in activity, permissions, and admin roles across AWS for every person in your cloud environment through comprehensive behavioral profiles.
Account
Takeover Protection
Extend uniform protection from account takeovers across multiple cloud applications and services, including AWS.
“When we first started looking, Abnormal’s API-based approach really interested us. Abnormal also offered automation capabilities that could reduce the amount of manual work we had to do on investigations and remediation.”
—Jeremy Smith, CISO, Avery Dennison
Related Resources
Understand Human Behavior in Your Cloud Environment
Gain dynamic visibility into how humans in your organization are accessing your most important cloud applications and services.
Request a Demo
Request a Demo




