Displace Your Secure Email Gateway
Replace your add-on SEG with Abnormal for AI-native protection against today's most sophisticated socially-engineered attacks.
Demo: Replace Your SEG
Get CISO Resource Kit
PROBLEM
SEG Shortcomings Put Your Business at Risk
Exposed to Advanced Attacks
Misses sophisticated attacks that don’t have known indicators of compromise.
Burdened by Manual Operations
Tedious management combined with manual processes drain productivity.
Limited to Email Visibility
Doesn’t see activity or user behavior beyond one-time inbound email checks.
SOLUTION
Abnormal + Microsoft
Abnormal complements Microsoft’s native email security, allowing organizations to replace add-on SEGs with a future-proofed solution that completely automates workflows and increases protection against the full spectrum of attacks.
70% of Abnormal customers have chosen to go without a legacy secure email gateway, and more security teams deprecate their SEG every day.
Discover Abnormal for Microsoft
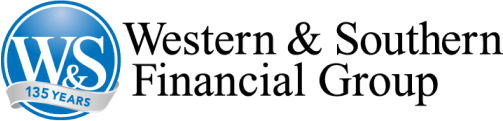
WHY ABNORMAL
Providing the Best SEG Displacement Solution
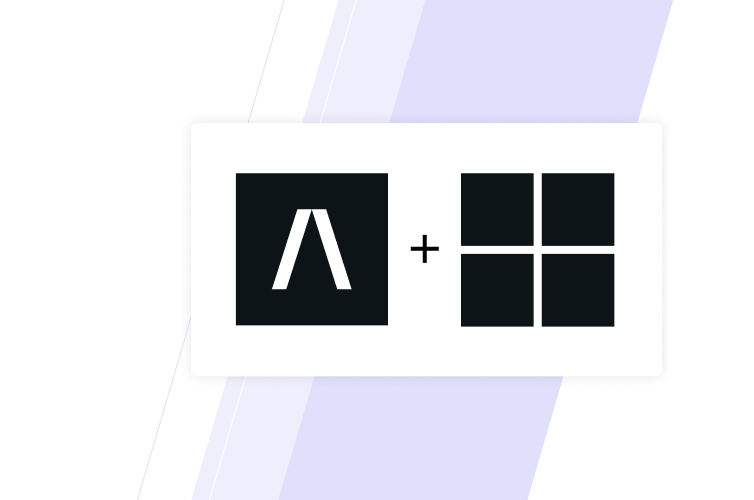
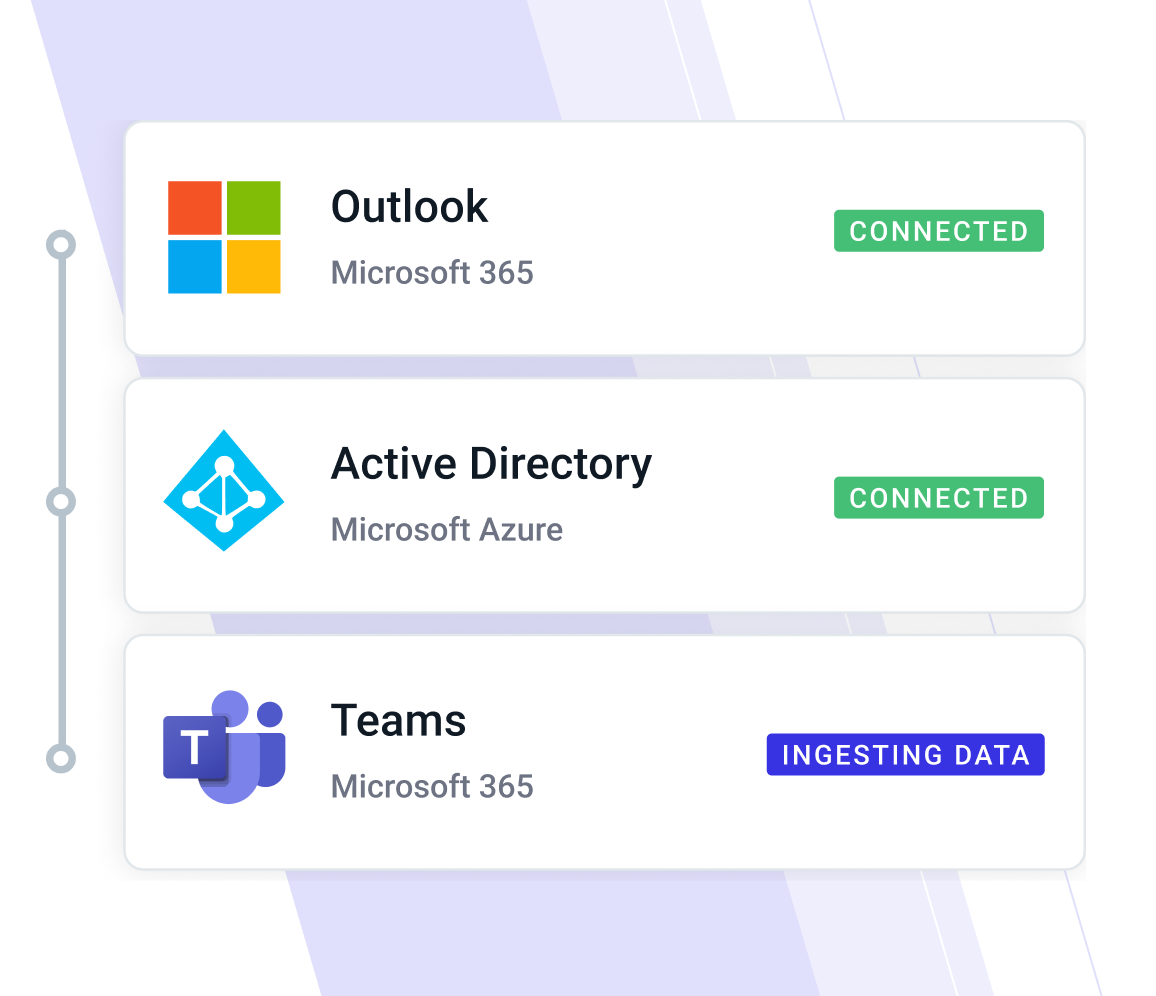
Ingests Unique Behavioral Data
Accesses tens of thousands of human behavior signals from Entra ID, Okta, CrowdStrike, and more via the API architecture. It's easy to connect in only three clicks, with no tuning or additional setup required.
Stops More Attacks with Human Behavior AI
Instantly builds per-user and per-organization AI detection models to deeply understand normal activity for every employee and vendor. Each message is compared to these baselines based on identity, behavior, and conversational context analysis.

Protects Across Channels
Extends protection capabilities beyond traditional email, securing communications and user accounts across cloud applications and infrastructure. Native API integrations connect attack visibility to support security workflows.
Benefits of Displacing Your SEG with Abnormal
Holistic Email Protection
Behavioral AI adds deep understanding of what’s normal, detects nuanced threats, and identifies anomalies in communication patterns.
Block Modern Attacks
Accelerated AI Automation
Fully automates security across the cloud-based email platform using advanced AI for threat detection and remediation.
Improve Automation
Uniform Cross-Platform Defense
Extends multi-layered security measures for consistent protection across communication channels and eliminates the need for redundant SEGs.
Apply Uniform Protection
“I didn’t see the value that a SEG would provide on top of [our enterprise email] and Abnormal Security. We haven’t noticed any loss by not having a SEG, we just noticed gain. So I basically redeployed the budget I used to spend on the SEG to Abnormal Security.”
— Global Technology Services Director, Commodities
Read Forrester Total Economic Impact Study
“Our executives and Board of Directors are commonly hit with significant amounts of phishing and BEC email attacks. Abnormal’s behavioral-based modeling and pattern recognition have been great in detecting and stopping those attacks. We are confident we have the right solution in place.”
— Jeremy Smith, CISO, Avery Dennison
Get Started with Abnormal
1
Calculate
Calculate the ROI you can receive by deprecating your secure email gateway today.
See Your ROI
2
Integrate
Deploy Abnormal in minutes via API integration and discover the attacks your SEG may be missing.
Get Your Risk Assessment
3
Deprecate
Migrate away from your SEG with help from the Abnormal team of experts.
Talk to the Experts
Increase Protection and Automation
See how Abnormal protects your organization from attacks that bypass costly secure email gateways.
Request a Demo
Request a Demo