Account Takeover Protection
Autonomous AI detection and response across cloud platforms.
See a Demo
PROBLEM
Cloud Breaches are on the Rise and Hard to Stop
Subheading text goes here
Account Compromise Is the Root of Cloud Breaches
With malicious generative AI tools and novel social engineering tactics, compromising cloud accounts has never been easier.
Security Teams Have Limited Cloud Visibility
Security teams don’t have the necessary visibility into the activities of every employee to continuously validate cloud identities.
Traditional Tools Fail to Provide Uniform Protection
86% of security teams feel current tools are inefficient at stopping account takeovers.
How Abnormal Dynamically Detects Cloud Account Compromise
Centralizes Security Visibility Across the Cloud Environment
Abnormal’s cloud-native API architecture allows security teams to integrate and ingest data from cloud platforms in under five minutes with only a few clicks. Security teams can then easily and immediately view activities, roles, and permissions for every employee across cloud platforms through PeopleBase.
Builds a Behavioral Baseline for Humans via AI
Abnormal’s human behavior AI monitors authentication events and notable activity across all integrated platforms. These data streams continuously enhance behavioral models, understanding access and usage patterns across platforms. This analysis requires zero manual rule or policy creation, unlocking valuable security analyst resources.

Detects and Remediates Cross-Platform Account Compromise with Autonomous AI
Abnormal’s Human Behavior AI automatically evaluates the risk across every employee based on the user’s activities such as sign-in events, IP addresses, and more. When notable anomalous activities are detected the platform automatically remediates the account for connected identities, reducing incident response times by >10x.
AI Delivers Unified Account Takeover Protection
Security teams can easily visualize the cross-platform notable events that led to the remediation action in one single place through the case timeline. Security teams can achieve uniformity and parity of account takeover protection across all cloud platforms.

Abnormal Account Takeover Protection Features
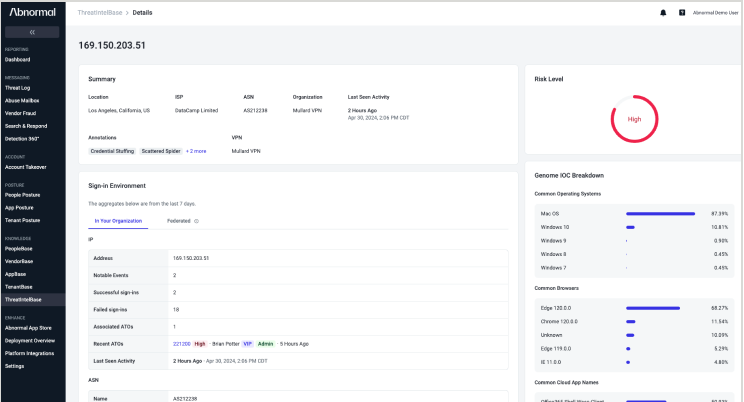
ThreatIntelBase
Surface and aggregate behaviorally-derived threat intelligence to improve threat hunting and incident response efforts and streamline SOC processes.
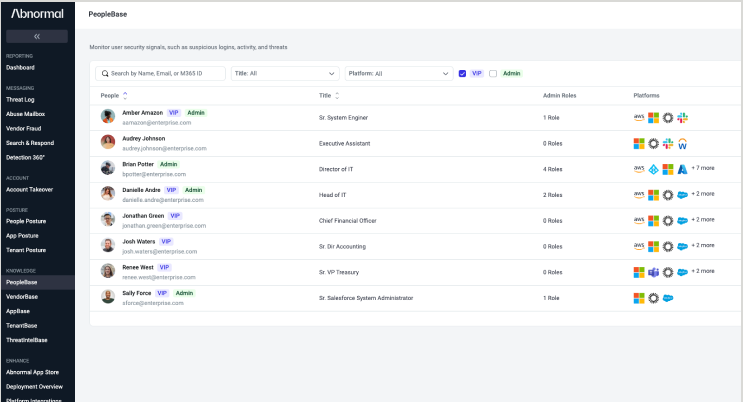
PeopleBase
Gain visibility into cross-application privileges, derived insights from Abnormal AI, and a cross-platform identity timeline of notable events for every employee.
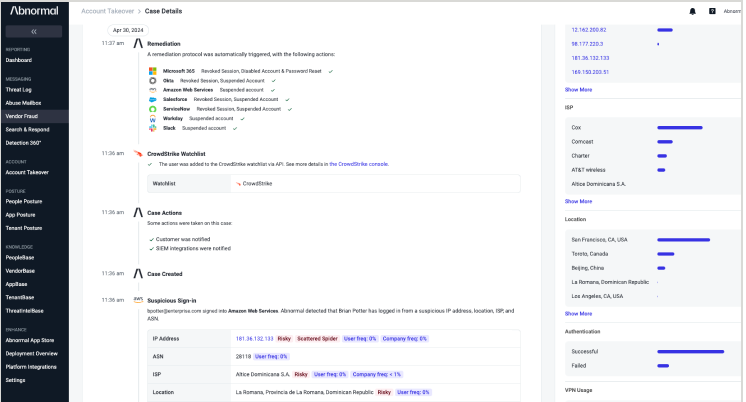
Behavioral Case Timeline
View a contextual timeline of suspicious human behavior that rolls up cross–cloud user activity into a singular Abnormal Behavior Case Timeline.
See Related Products
“Modern breaches are rooted in cloud account compromises and detecting them consistently across critical cloud apps and platforms is a significant challenge for us today. Abnormal is the only solution in the market that leverages a behavioral AI approach to deliver a uniform cross-platform account takeover protection. "
— Deputy CISO, Global Insurance Organization
Related Resources
Detect, Disable, and Remediate Compromised Accounts
Catch account takeover attempts that other solutions miss with human behavior AI.
Request a Demo
See a Demo




