HR Termination on Zoom Leads to Credential Theft
The work landscape is changing as employees move to working remotely because of COVID-19 shelter-in-place orders. As a result, people are switching from in-person meetings to online video conferencing software such as Zoom.
In this attack, attackers pose as a Zoom meeting notification, asking recipients to join a Zoom meeting regarding their performance review and potential termination.
Summary of Attack Target
- Platform: Office 365
- Email Gateway: MessageLabs
- Victims: Employees
- Payload: Malicious Link
- Technique: Impersonation
Overview of the Zoom Impersonation Attack
This attacker impersonates Zoom by crafting a convincing email and landing page that mimics meeting notifications from Zoom. The email masquerades as an automated notification for an important meeting with HR regarding the recipient’s performance review and termination.
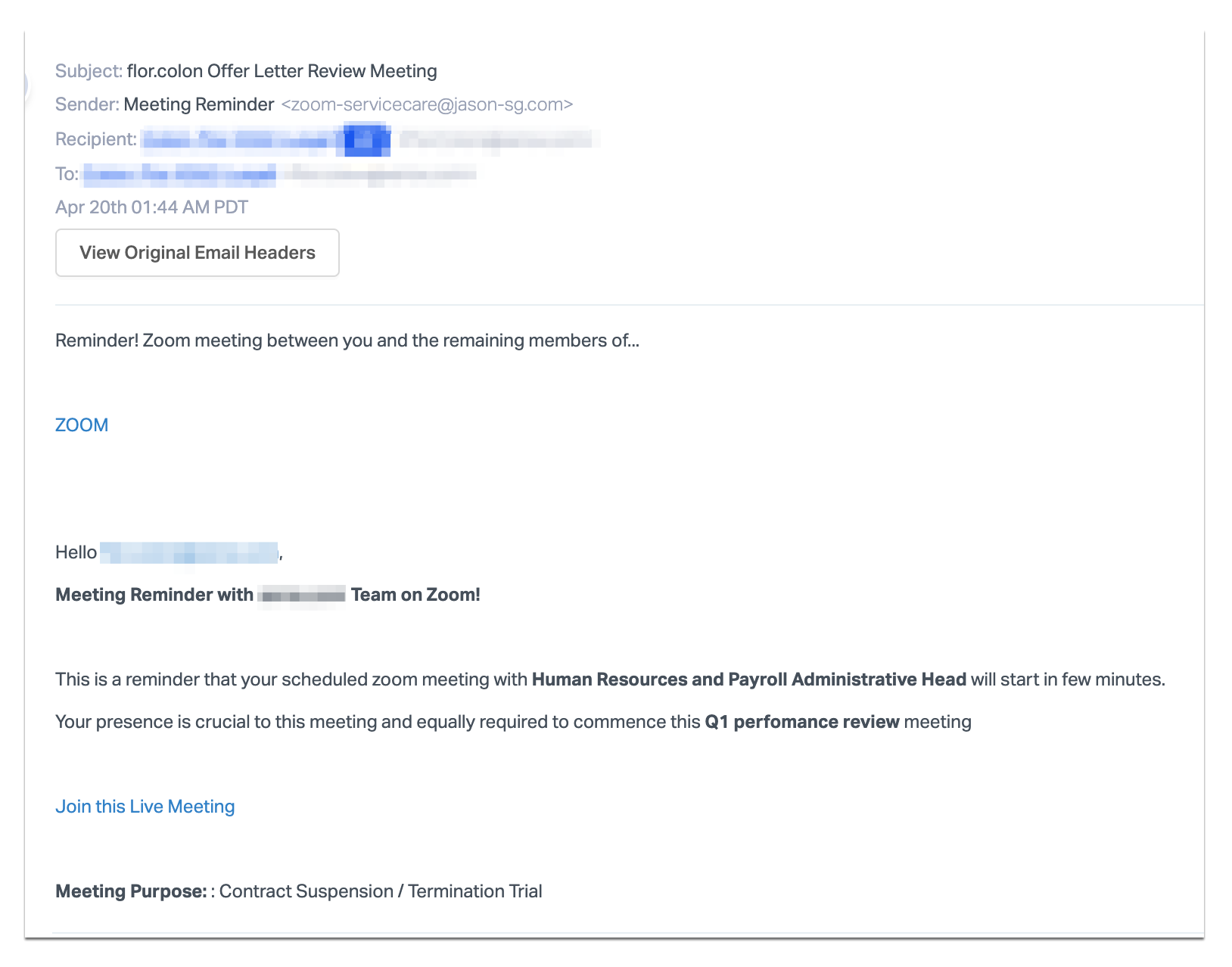
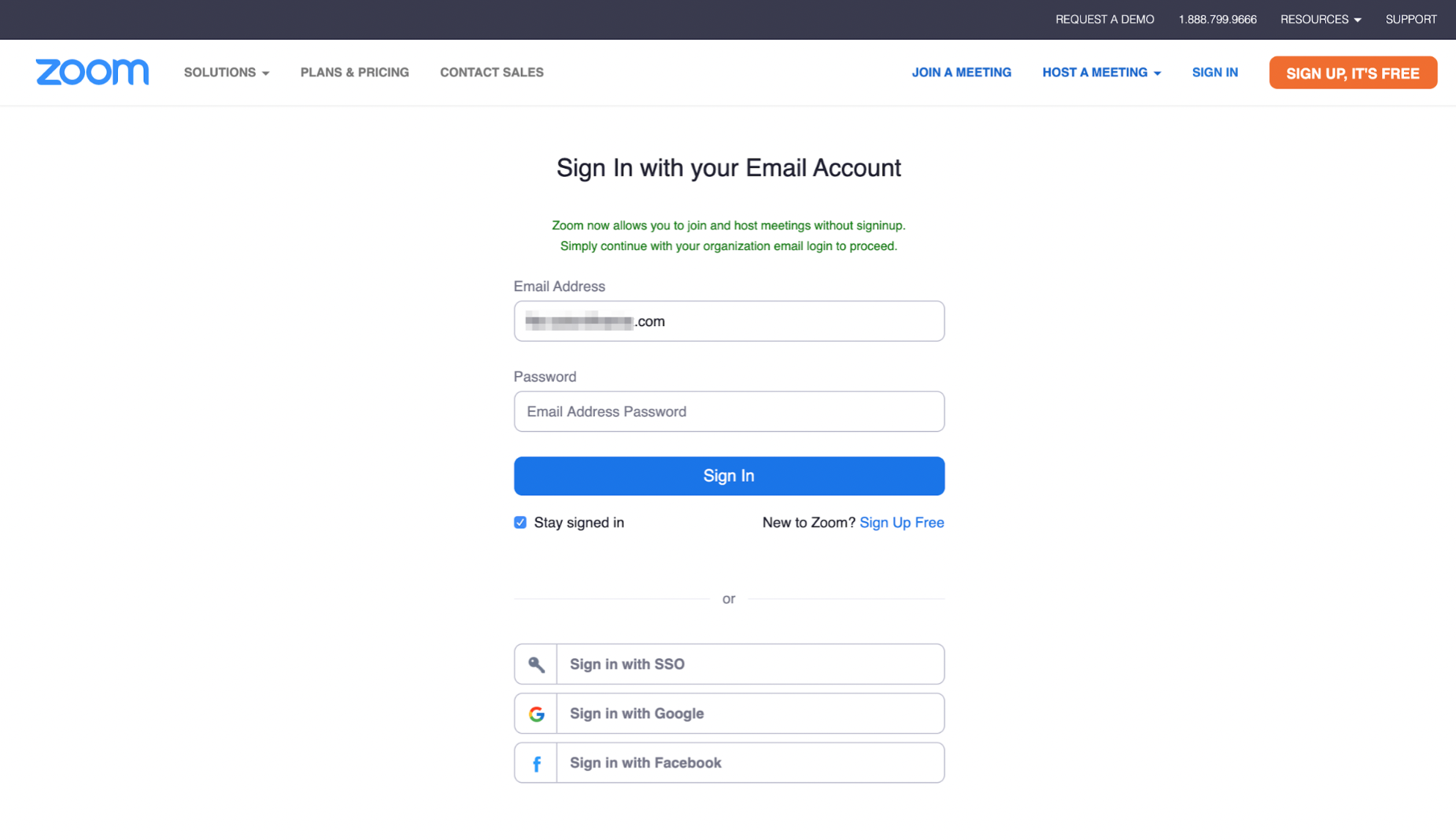
The email contains a link to a fake Zoom login page hosted on “zoom-emergency.myftp.org," which asks for the user's Zoom login credentials.
Should recipients fall victim to this attack, their login credentials and any other information stored on Zoom will be compromised. Additionally, ttackers are likely hoping that these credentials are reused across sites so they can use them to access Office 365 and other, more valuable applications.
Why the Zoom Impersonation Attack is Effective
This email masquerades as a reminder that the recipient has a meeting with HR regarding their termination. When the victim reads the email they will panic, click on the phishing link, and hurriedly attempt to log into this fake meeting. Instead, their credentials will be stolen by the attacker. In addition to relying on urgency, the email looks and is formatted like a legitimate meeting reminder commonly used by Zoom. The landing page is also a carbon copy of the Zoom login page; except the only functionality on the phishing page is that the login fields are used to steal credentials. Recipients would be hard-pressed to understand that this was, in fact, a site designed specifically to steal their credentials.
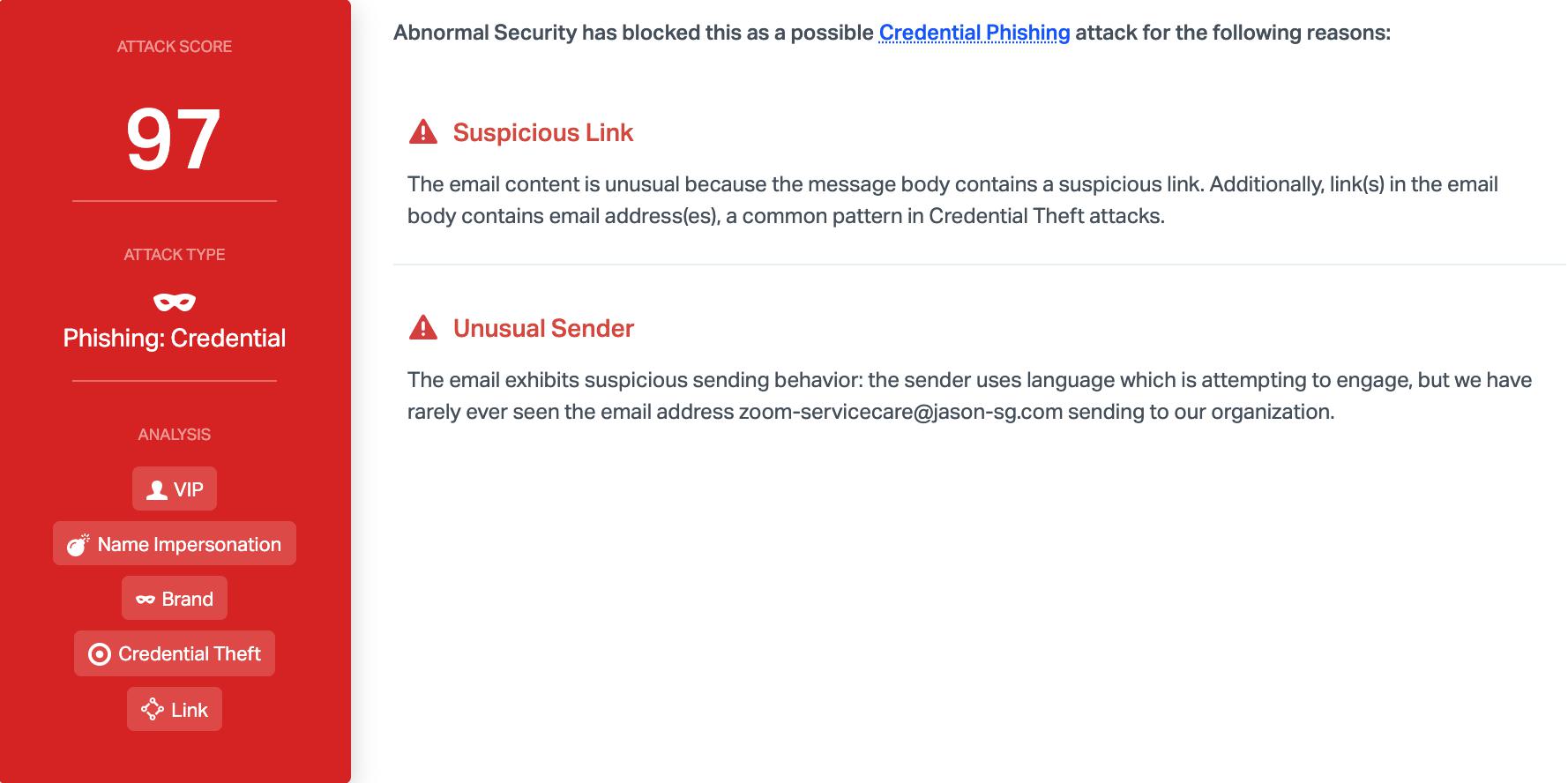
Abnormal detected this attack due to the suspicious sender email and the suspicious link. Combined, these two elements show that the email is malicious and the platform blocks it before it causes panic among end users, who may all believe that they are being terminated.
To learn how to stop brand impersonation and credential phishing emails from harming your organization, request a demo of the Abnormal platform today.






