PayPal Spoofed in Credential Phishing Attack
PayPal is a well-known money transfer application, used often between friends and family as well as for small businesses. Because PayPal accounts are often linked to credit cards and bank accounts, the company itself is a commonly impersonated brand from attackers hoping to steal that information from unsuspecting victims.
In this attack, attackers use a method known as spoofing to impersonate PayPal, leading recipients to a phishing page.
Summary of Attack
- Platform: Office 365
- Bypassed Email Security: Ironport
- Victims: Employees
- Payload: Malicious Link
- Technique: Spoof
Overview of PayPal Spoofing Attack
This email appears to be sent from PayPal (service@paypal.com, which is a real PayPal domain), telling recipients that their account has been flagged and limited. However, authentication fails for this message and the actual sending domain is ‘dion.ne.jp’, a domain that has no correspondence to PayPal. The attacker is attempting to gain the trust of the recipient by making it appear as though PayPal has sent the email. This method—spoofing a real domain—can deceive the recipient into thinking the email is legitimate and coming from PayPal.
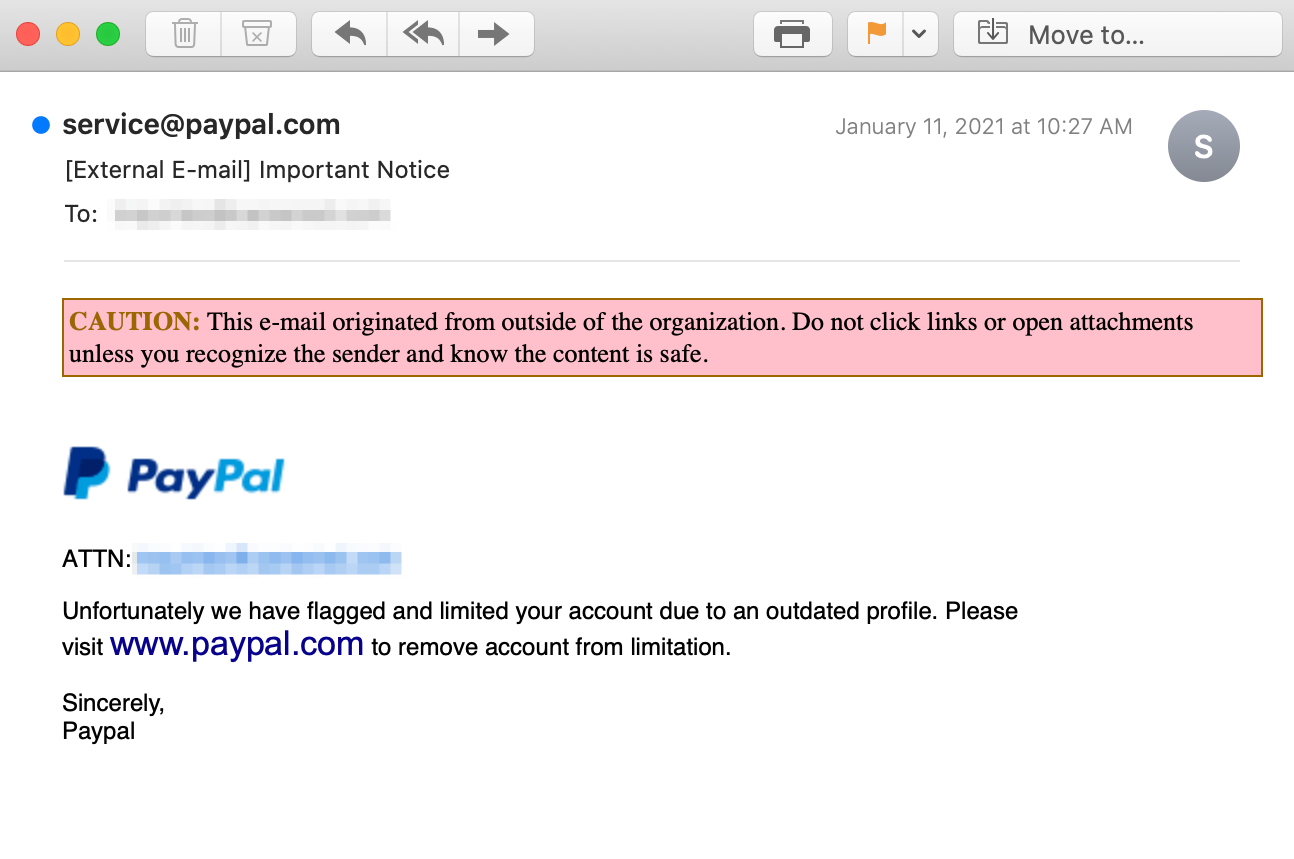
It may look as though the link within this email will take the recipient to paypal.com, but the attacker uses a concealed link in an attempt to fool the recipient. When clicked, the link in the email actually leads the recipient to a phishing page at ‘arferdimpex.biz’. This landing page looks nearly identical to the real paypal.com website and asks the recipient to input their email or phone number and password.
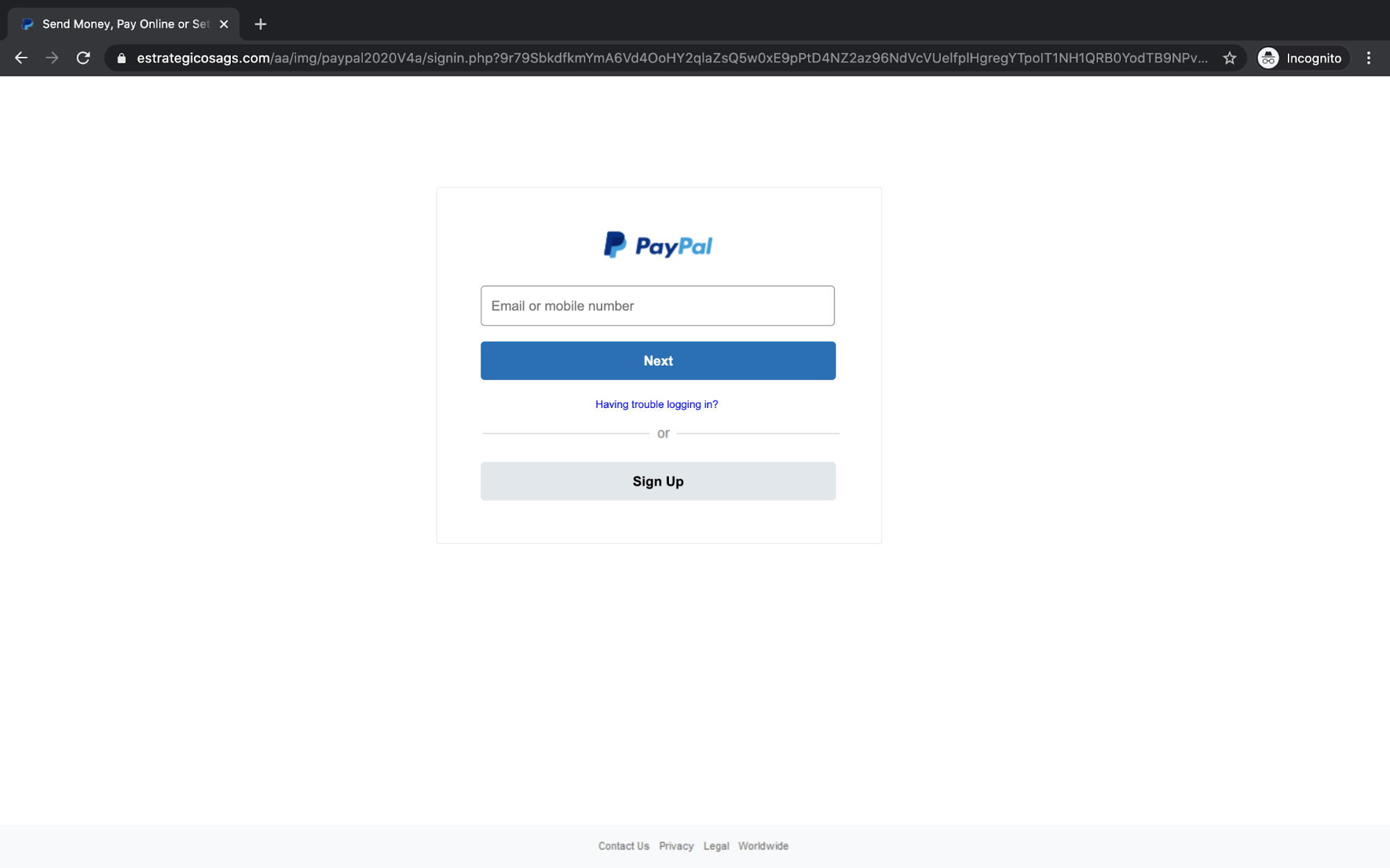
For the casual observer, it'd be difficult to notice that this is a phishing site, as the only true indicator is the suspicious URL. If the recipient does click on the concealed link and input their credentials into this fake PayPal page, the attacker will then gain access to their PayPal account and all of the sensitive, personal information inside. For those unlucky victims with money sitting in the account, the attacker would be able to transfer those funds to an account under their control, or use the banking and credit card details to make purchases.
Why the Spoofed PayPal Attack is Effective
The attacker’s meticulous work in creating this fake PayPal website makes this attack very effective. The landing page may look nearly identical to the actual website, but the domain, ‘arferdimpex.biz’, is, of course, not a PayPal domain. Without scrutinizing the real email address or the domain, the recipient may not notice that these are not actually from PayPal. Furthermore, because PayPal is commonly used for payment across the Internet, recipients who receive this may try to quickly fix their supposedly flagged and limited account, and therefore overlook signals that this is an email attack.
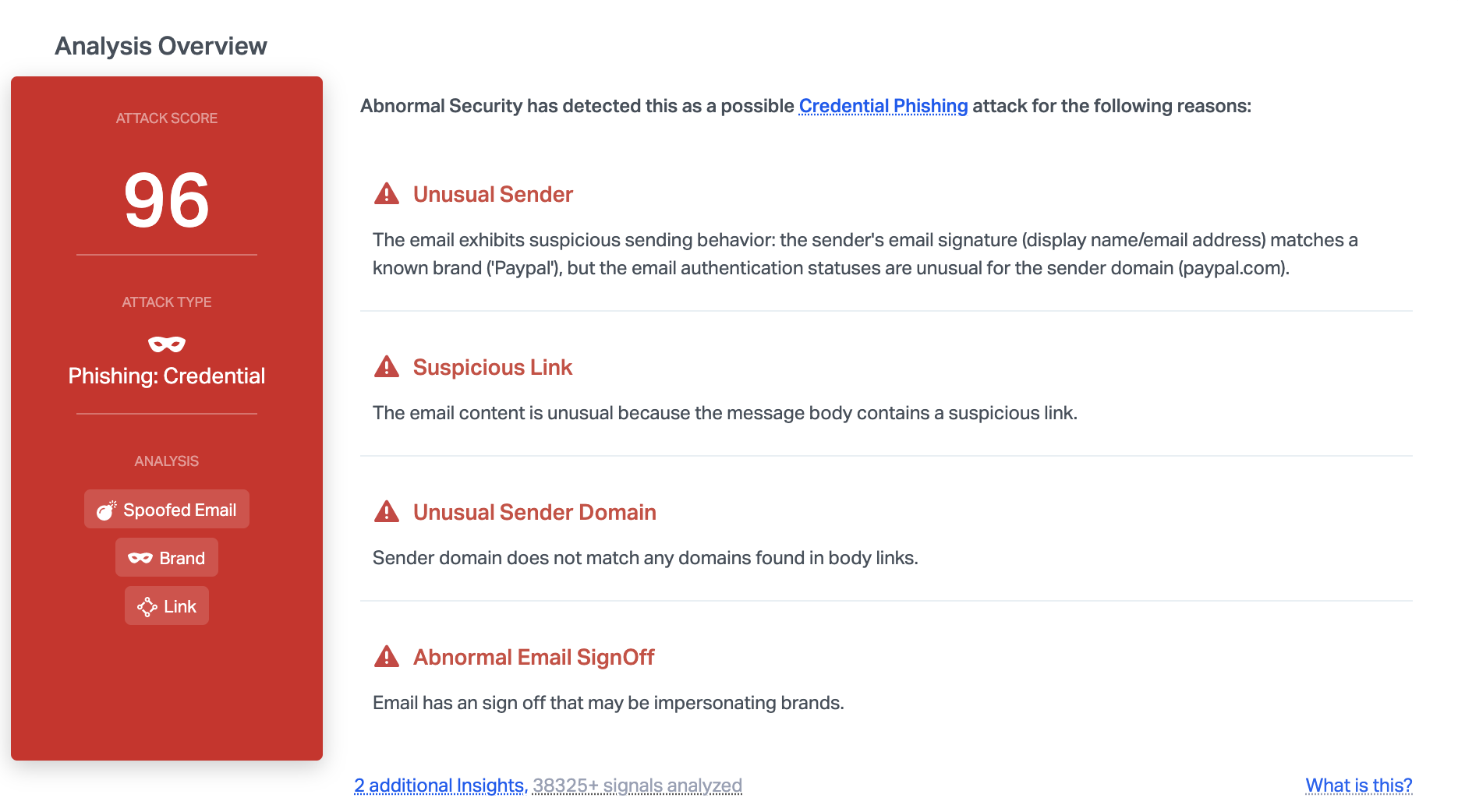
Abnormal was able to detect this malicious email due to a variety of factors, including the unusual sender domain and the suspicious link. In addition, the unusual authentication statuses and email sign off indicate that it may be malicious—causing Abnormal to block it before it reached end users.
To learn how Abnormal can block malicious emails for your organization, request a demo today.






