Facebook Impersonated in Credential Phishing Scam
Facebook phishing attacks are popular because users tend to use the same email address and password for other sites. In this attack, the cybercriminal impersonates Facebook to send out a phishing attack using a legitimate Facebook link.
Summary of Attack Target
- Platform: Office 365
- Email Security Bypassed: IronPort
- Victims: Employees
- Payload: Malicious Link
- Technique: Impersonation
Overview of Facebook Credential Phishing Attack
At first glance, this email looks to be coming from Facebook Mail. The email informs the recipient that there have been reports of the recipient’s page violating Facebook policies. Through a legitimate Facebook link, the attacker provides a way for the recipient to appeal the supposed “violations,” stating that appeals will only be accepted within 48 hours.
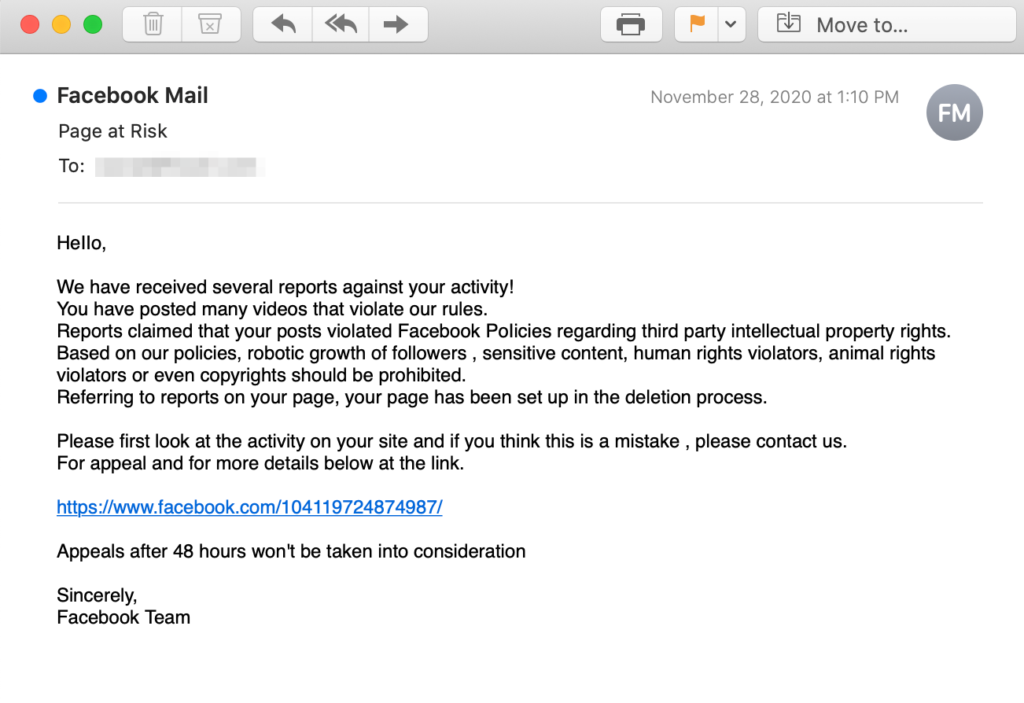
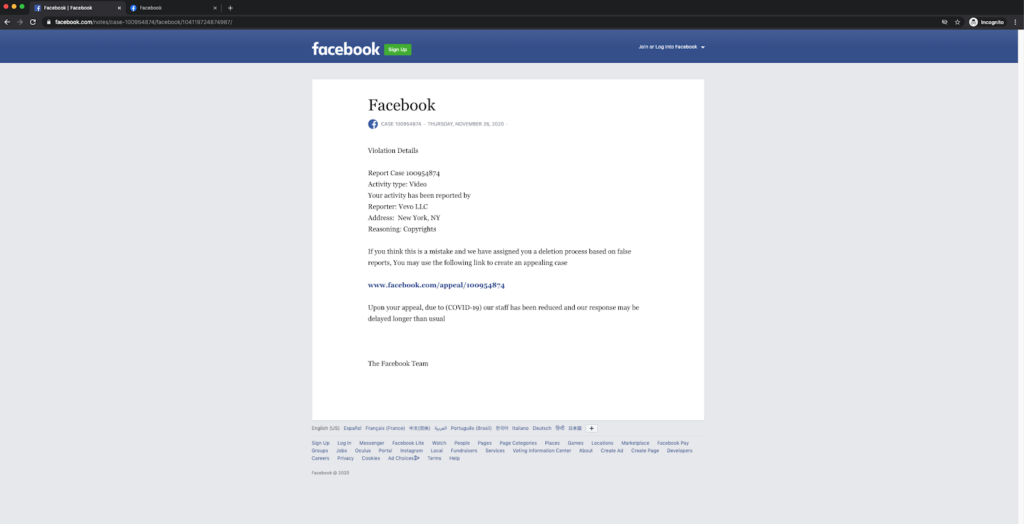
With additional research, there are a few indicators that this is in fact the start of a phishing attack. Although the email is actually coming from a random Gmail account, the attacker changes the display name to “Facebook Mail” to deceive the recipient. The attacker also uses a real Facebook link leading to a real Facebook page. It is only after following the link on this page that the recipient will be redirected from the actual Facebook website.
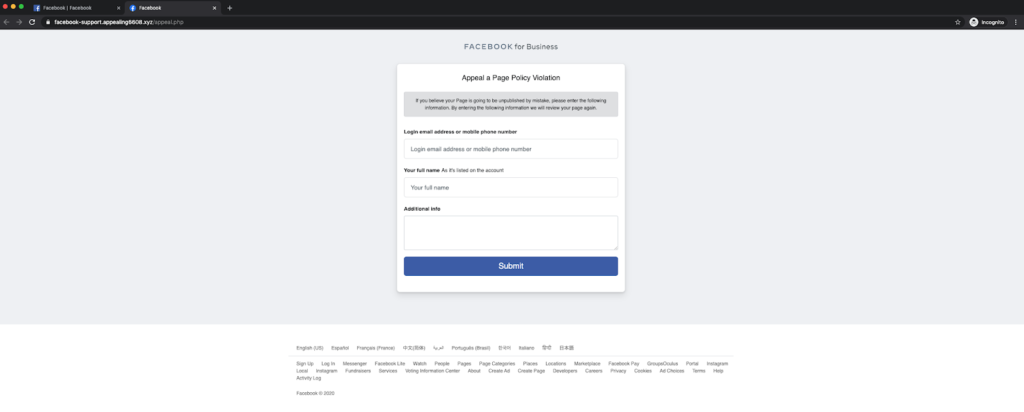
Although the original link the attacker provides in the email leads to Facebook’s website, the link is concealed, and redirects to a phishing page with the URL ‘https://facebook-support[.]appealing6608[.]xyz/’. The attacker attempts to fool the recipient by putting “facebook-support” in the URL, but the domain of this site, “appealing6608[.]xyz,” has no relation to Facebook.
This impersonated Facebook site then asks the recipient for their email or phone number, full name, and any additional information.
When the recipient fills this out and clicks submit, they are led to the last step of the attack. The final landing page looks like a legitimate Facebook login page, stating “you must log in to continue,” but the domain remains “appealing6608[.]xyz,” instead of “facebook.com.” It is here that, if the login is filled out, the attacker gains the recipient’s Facebook credentials.
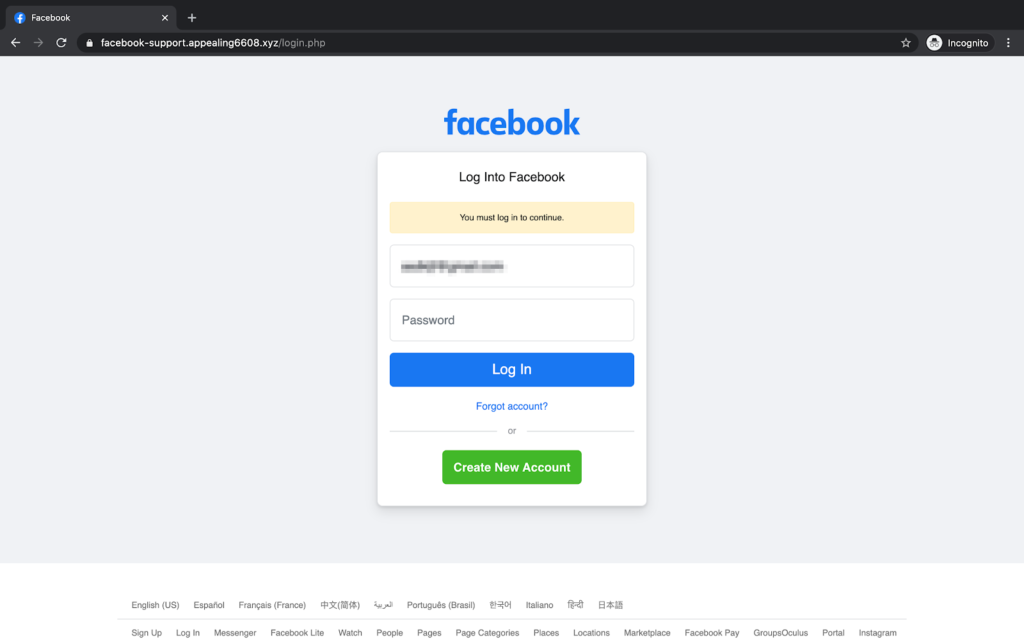
If the recipient does fall subject to this attack and inputs their credentials, the attacker will gain access to the account any sensitive, personal information included within it. The attacker can find out where the recipient lives, attends school, and other sensitive details about them through their Facebook profile. This also gives the attacker the opportunity to take advantage of this compromised account and attempt to compromise the recipient’s Facebook friends as well.
Why the Facebook Phishing Attack is Effective
To make this attack effective, the attacker uses a real Facebook link in their email, possibly causing the recipient to believe this was a real email from Facebook and a safe link to follow. Further, the attack conceals the link provided on the original landing page. The link appears as though it will lead to another Facebook website, but instead leads to a phishing site. It is only after the recipient follows the link in the original landing page that they may realize that this is not a legitimate email, as they are redirected from the Facebook website. The final landing page that the recipient is faced with, where they are asked to input their credentials, looks nearly identical to the real Facebook login page.
And for those who use Facebook regularly, the attackers use fear and claim that appeals will only be accepted for 48 hours after the receipt of this email. This creates a sense of urgency for the recipient that will make it more likely for them to overlook red flags in their haste to complete the actions this email says are required of them.
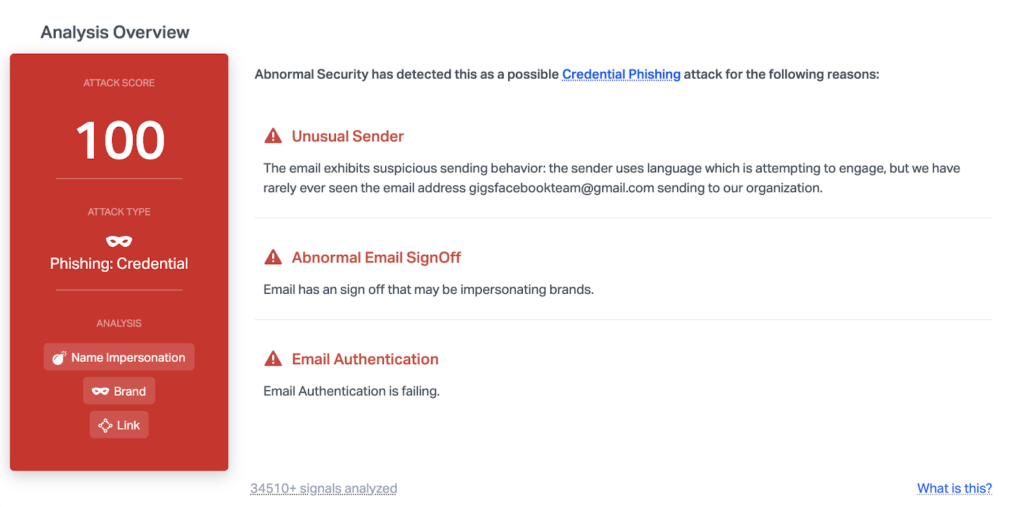
Abnormal is able to catch this attack due to a multitude of factors. The key indicator here is that DMARC email authentication fails for the sender address, and the brand name impersonation indicates that it is a malicious email. The content of the message and the multiple redirects are also key indicators that this email should not be trusted.
To learn more about how Abnormal prevents credential phishing, request a demo today.






