VPN Notifications Used for Credential Phishing
Due to the transition to remote work during the COVID-19 pandemic, corporations have become more concerned about online security and privacy. Companies rely on VPNs to connect remote employees to vital company servers, as well as to provide secure data sharing.
Attackers are taking advantage of the situation and in this attack, they impersonate a notification from the user's organization regarding VPN configuration in an attempt to steal credentials.
Summary of Attack Target
- Platform: Office 365
- Victims: Employees
- Payload: Malicious Link
- Technique: Spoofed Email
Overview of the VPN Attack
This attack impersonates a notification email from IT support at the recipients’ company. The sender email address is spoofed to impersonate the domain of each target's organization and the link provided in the email allegedly directs to a new VPN configuration for home access. Though the link appears to be related to the target's company, the hyperlink actually directs to an Office 365 credential phishing website.
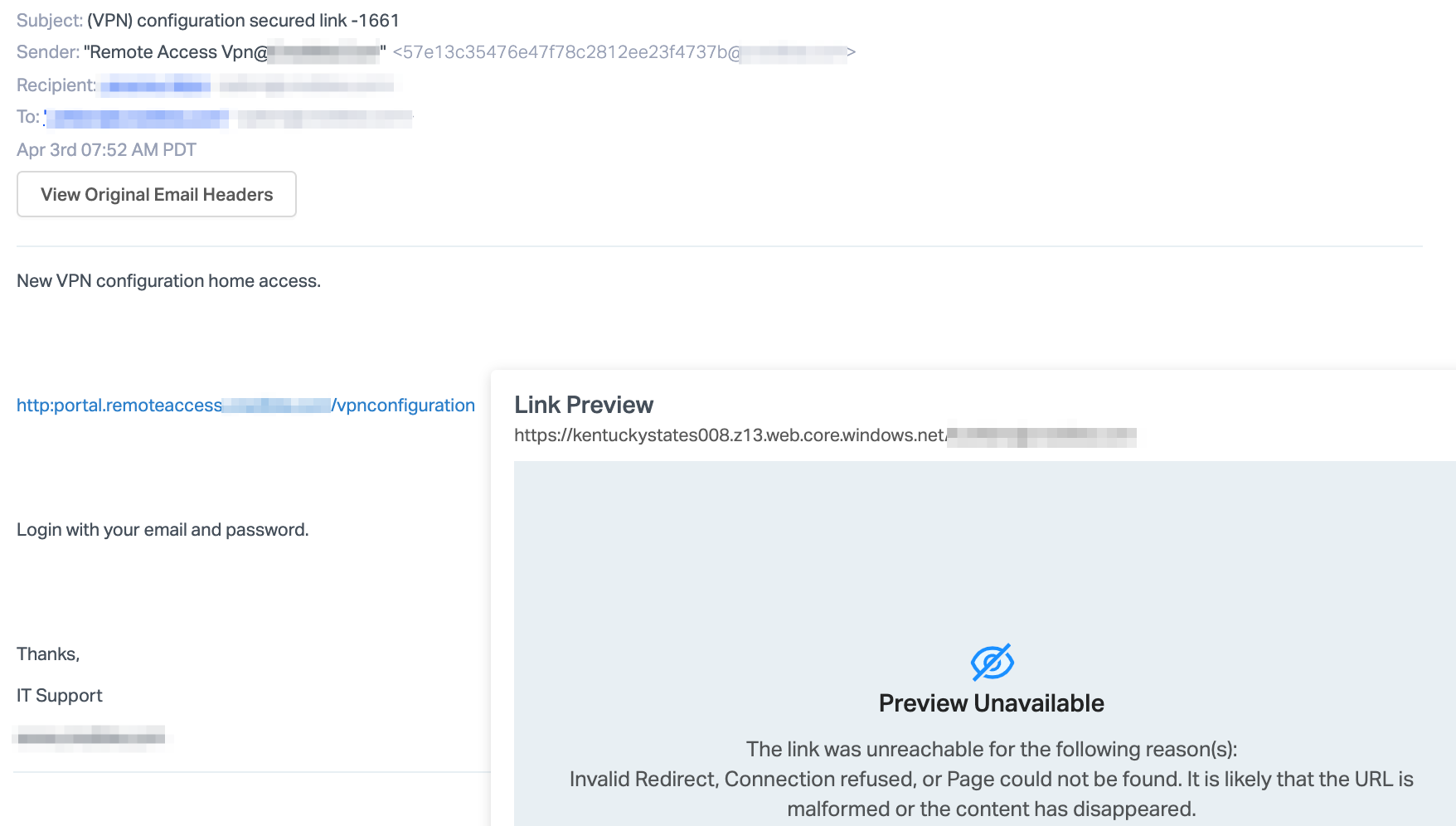
Multiple versions of this attack have been seen across different clients, from different sender emails and originating from different IP addresses. However, the same payload link was employed by all of these attacks, implying that these were sent by a single attacker that controls the phishing website.
Should the recipient fall victim to this attack, the user’s credentials would be compromised. In addition, the information available with the user’s Microsoft credentials via single-sign-on is also at risk—allowing threat actors access to confidential information across the company.
Why the VPN Attack is Effective
Because most employees are working from home, a VPN has become a necessity for some work-related tasks. Employees will likely be attuned to any alleged updates to their VPN configuration in order to avoid any issues completing work that requires VPN access.
This email attack impersonated the recipients’ company domain and the original landing page looks identical to the Office 365 login website. Since the phishing website is hosted on a Microsoft-owned platform, the webpage certificate is a valid Microsoft certificate. However, the URL of this site should not be trusted, and instead, users should only log in from their main company-affiliated webpage.
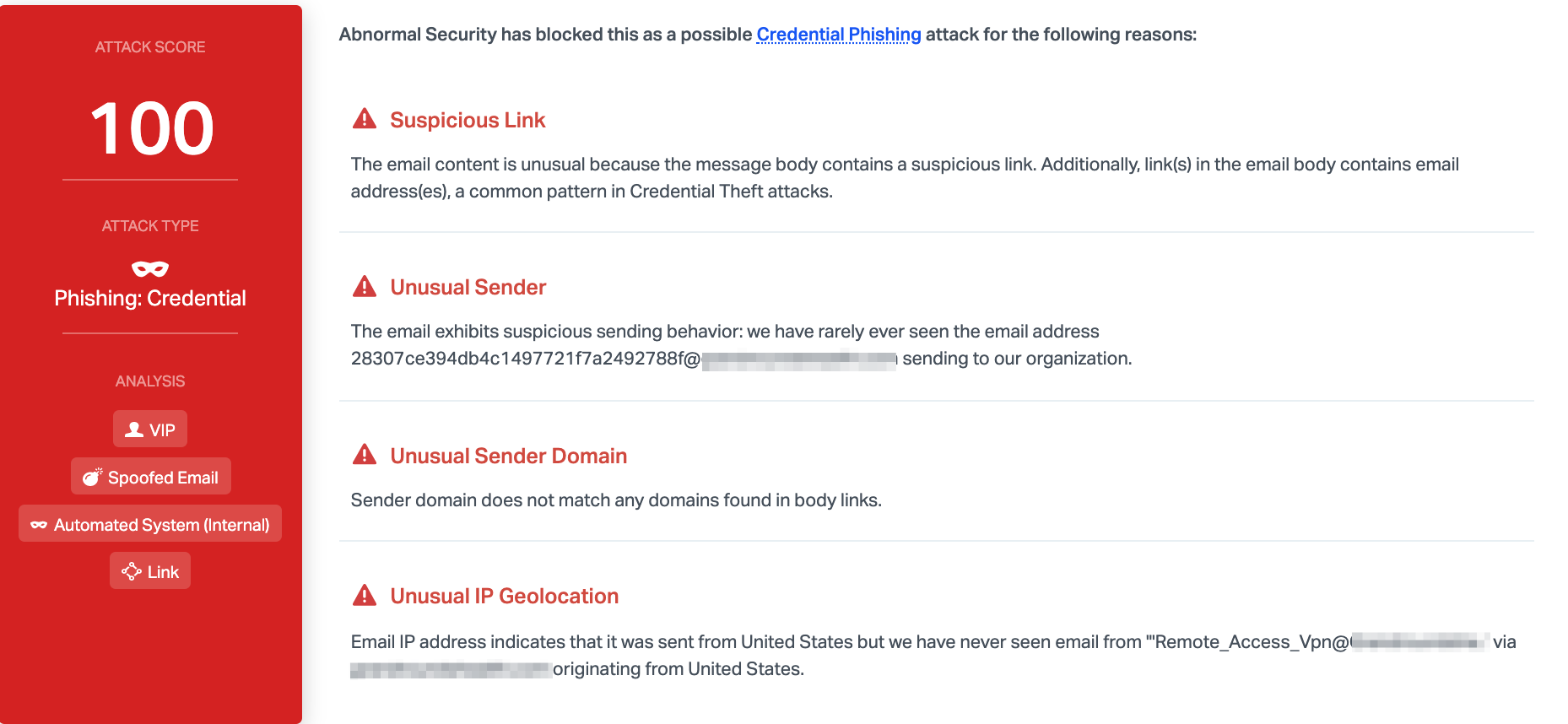
Abnormal detected this attack due to the unusual sender, who has never sent to this organization before, and the fact that the sender domain does not match any domains found within the body links. Combined with the unusual sender IP geolocation and the suspicious link, we can determine that this email is malicious and block it before reaching inboxes.
To discover how Abnormal can block malicious credential phishing messages for your organization, see a demo today.






