Social Media Platforms Impersonated in New Scams
Abnormal Security has observed attackers impersonating major social media platforms like Instagram, Facebook, and Twitter to steal the login credentials of employees at enterprise organizations. In the past two months, we have seen a 60% increase for several organizations with key social media presences.
Overview of the Social Media Attacks
These attacks impersonate popular social media platforms to deliver phishing emails to influential users of each platform by impersonating Instagram, Facebook, and Twitter, in an attempt to extract login credentials.
Here are examples of the attacks we've observed on various platforms.
Instagram Impersonation Scams
Attackers are impersonating a notification from the company. This notification aims to create a sense of urgency for the recipient by claiming their account contains content that violates Instagram policy and copyright law, and the recipient's account will be deleted permanently within 48 hours. The email contains a link to an appeals form that recipients are instructed to fill out, ostensibly to prevent this account deletion.
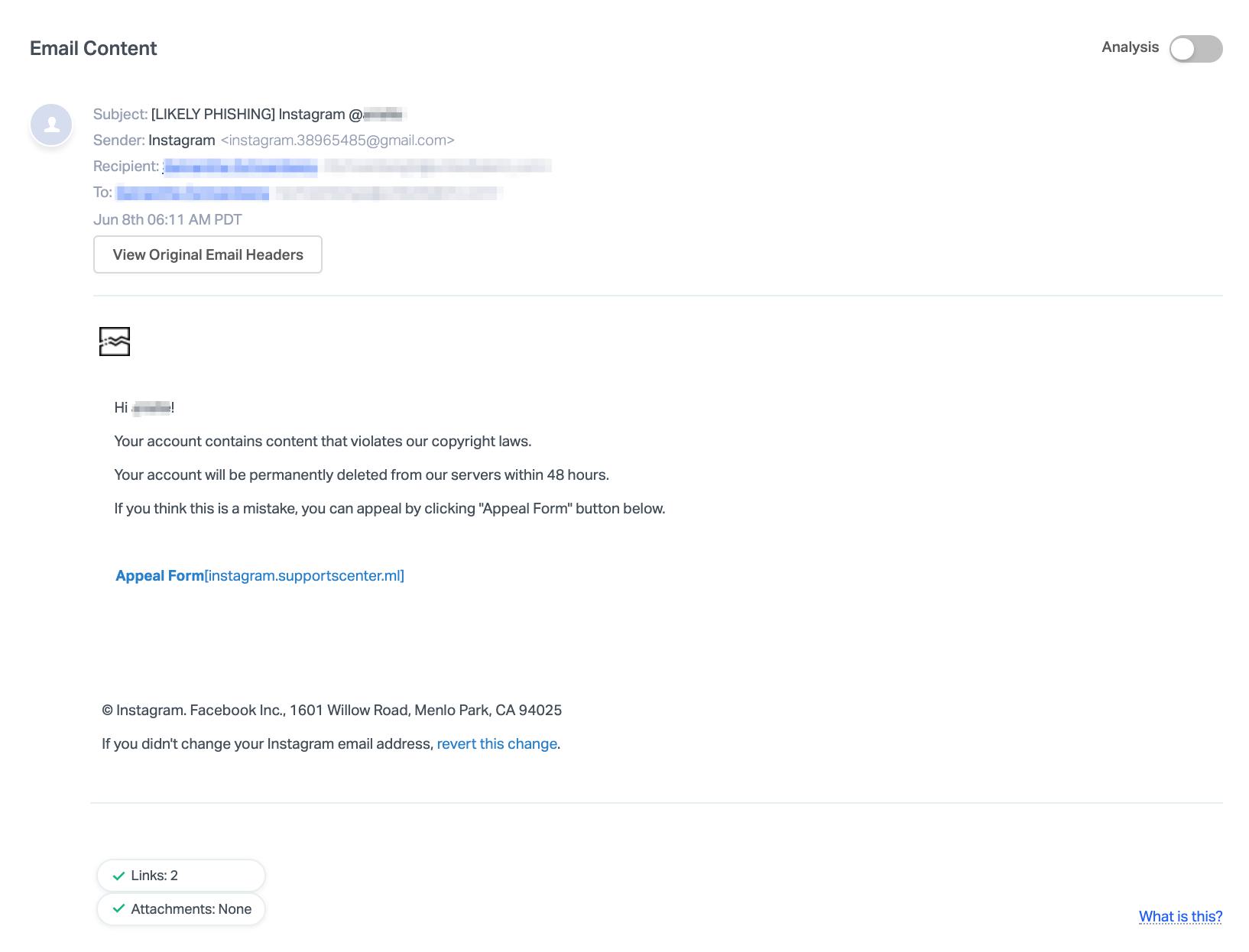
The email states that is this was an error, the recipient can appeal it by following the link included in the email. That link, of course, leads to a phishing page where the user inputs their credentials.
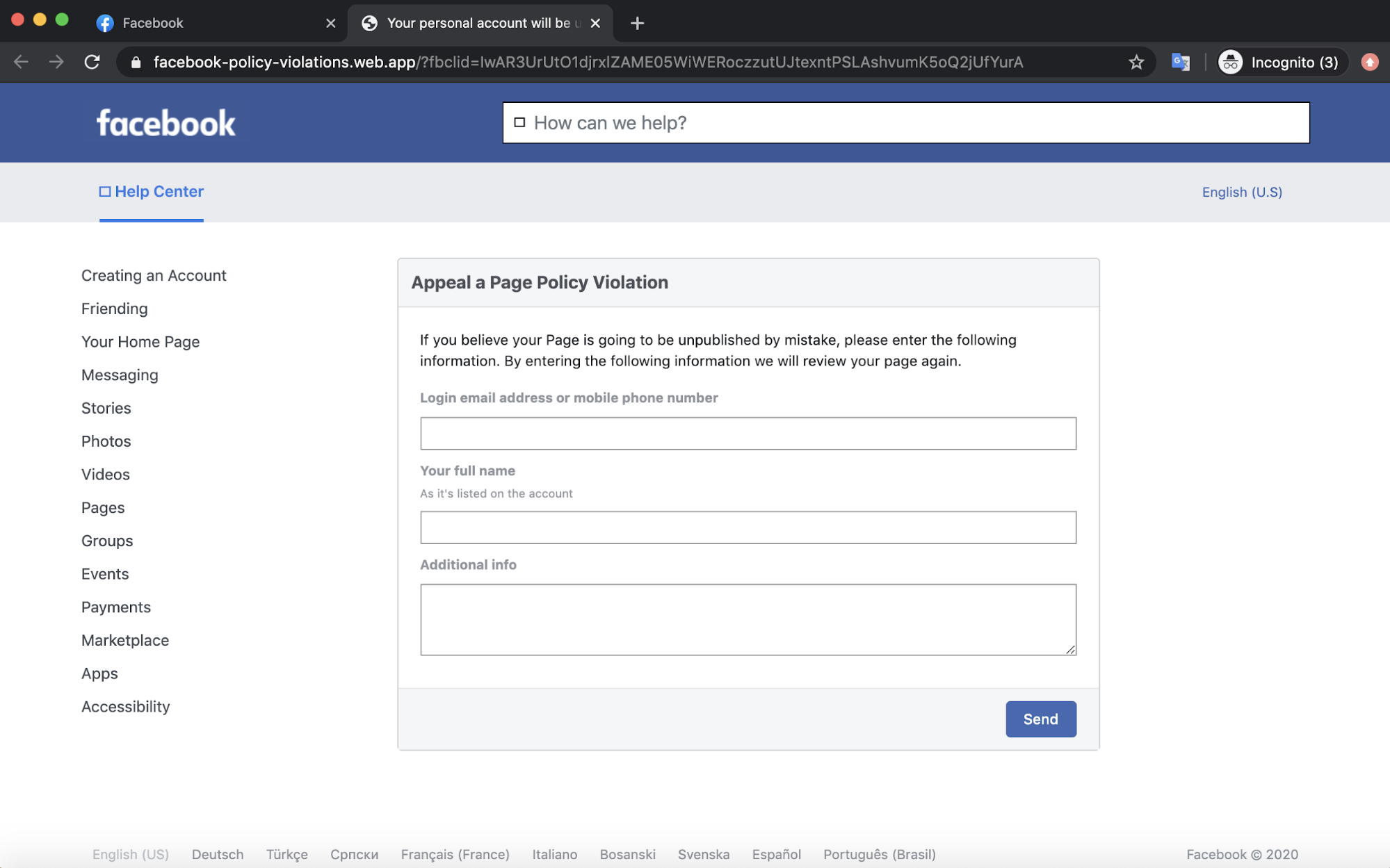
Facebook Impersonation Scams
Attackers here are also impersonating an automated message from Facebook with a similar template. This notification again intimidates the recipient by stating they have received a number of complaints and that Facebook has had to unpublish the user's page.
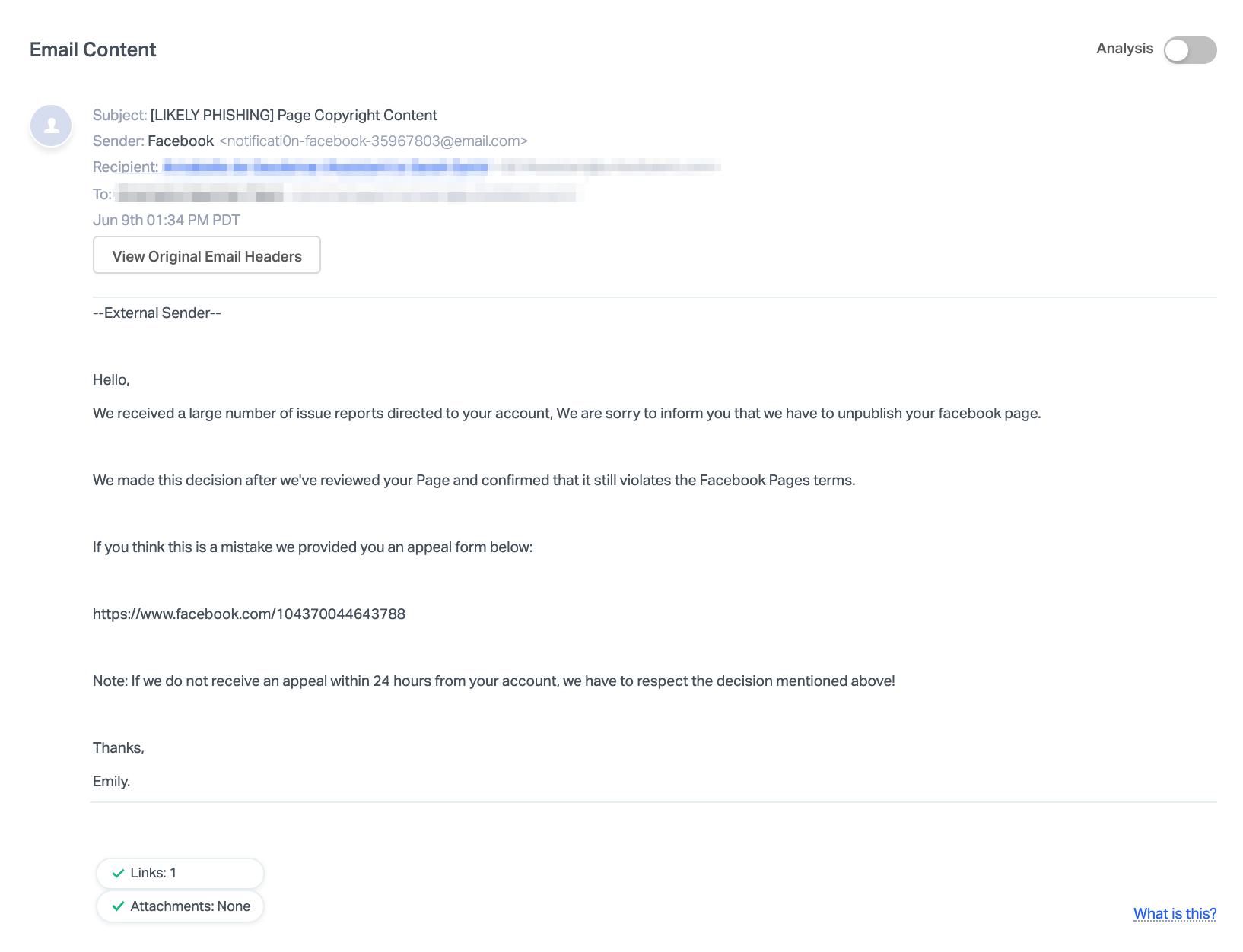
Again here, the attackers provide a landing page where the recipient can appeal the copyright infringement.
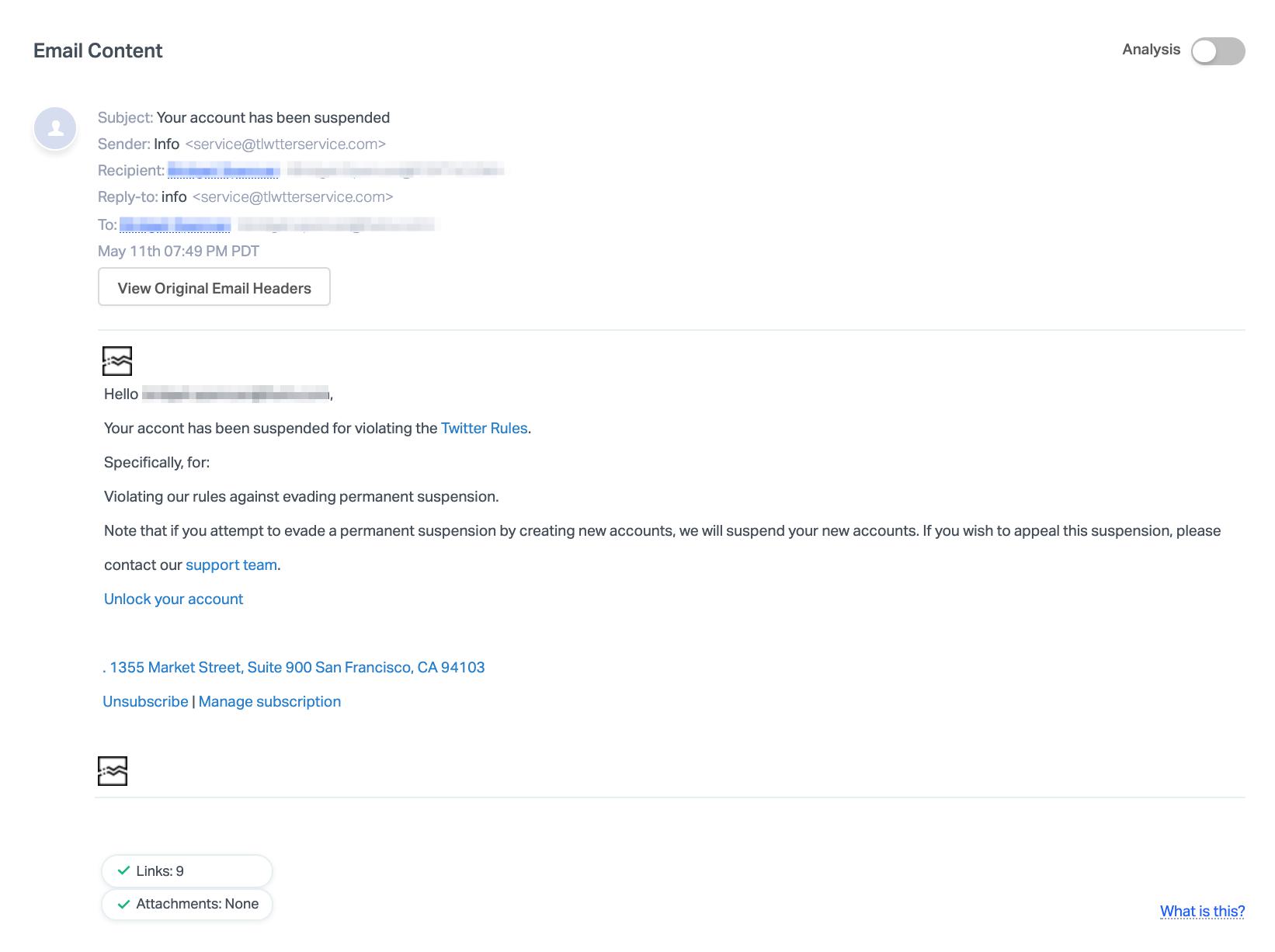
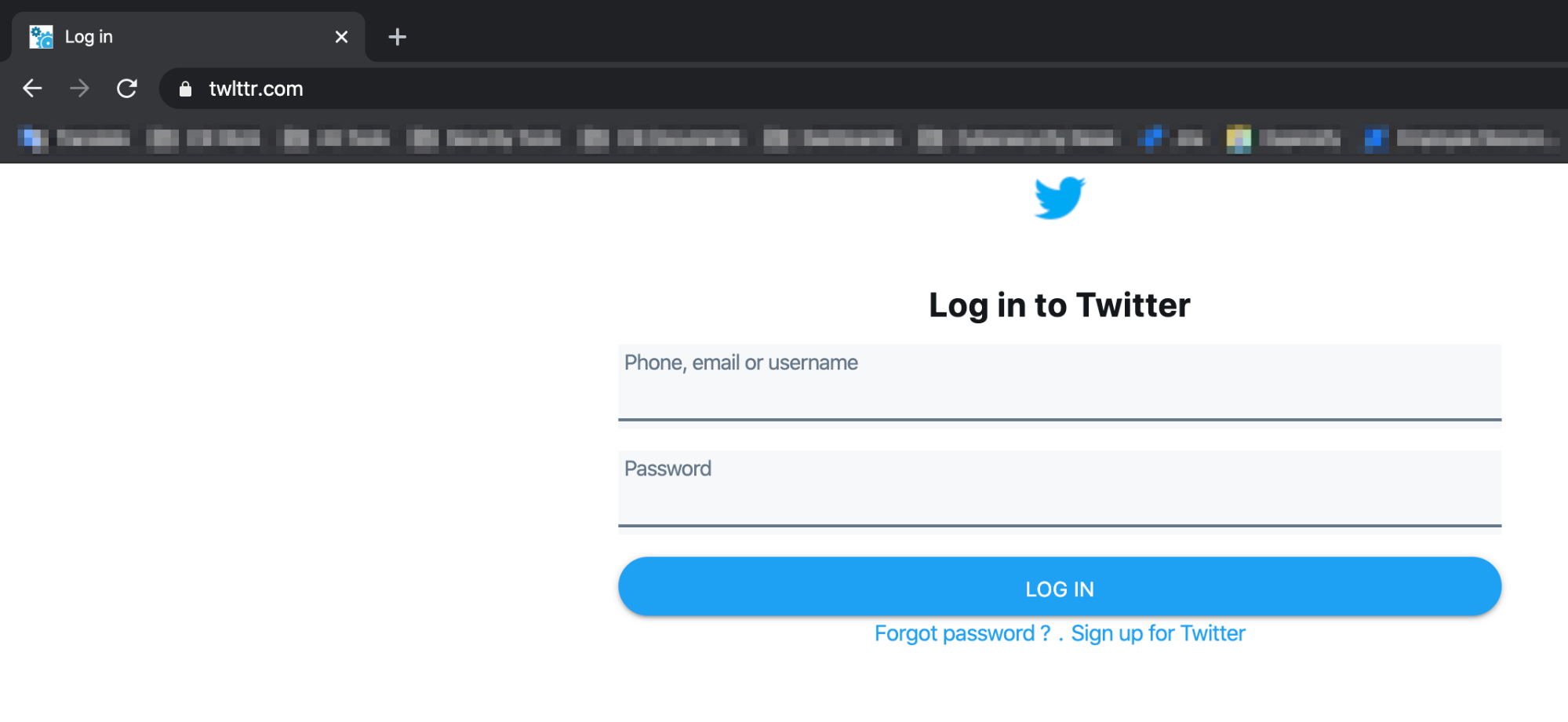
Twitter Impersonation Scams
In a recently uncovered Twitter scam, attackers are sending emails from a lookalike domain they've registered, where the "i" in Twitter is replaced with a lower-case "L". The body of the email contains a similar pattern to the Facebook and Instagram emails—the email claims the user's account has been suspended for violating Twitter rules, though they state the user is being suspended from creating new accounts. A form is also available to appeal the suspension.
In each of these emails, the social media platforms are impersonated and the body of the message contains urgent language, pressing the user to take action or their accounts will be deleted.
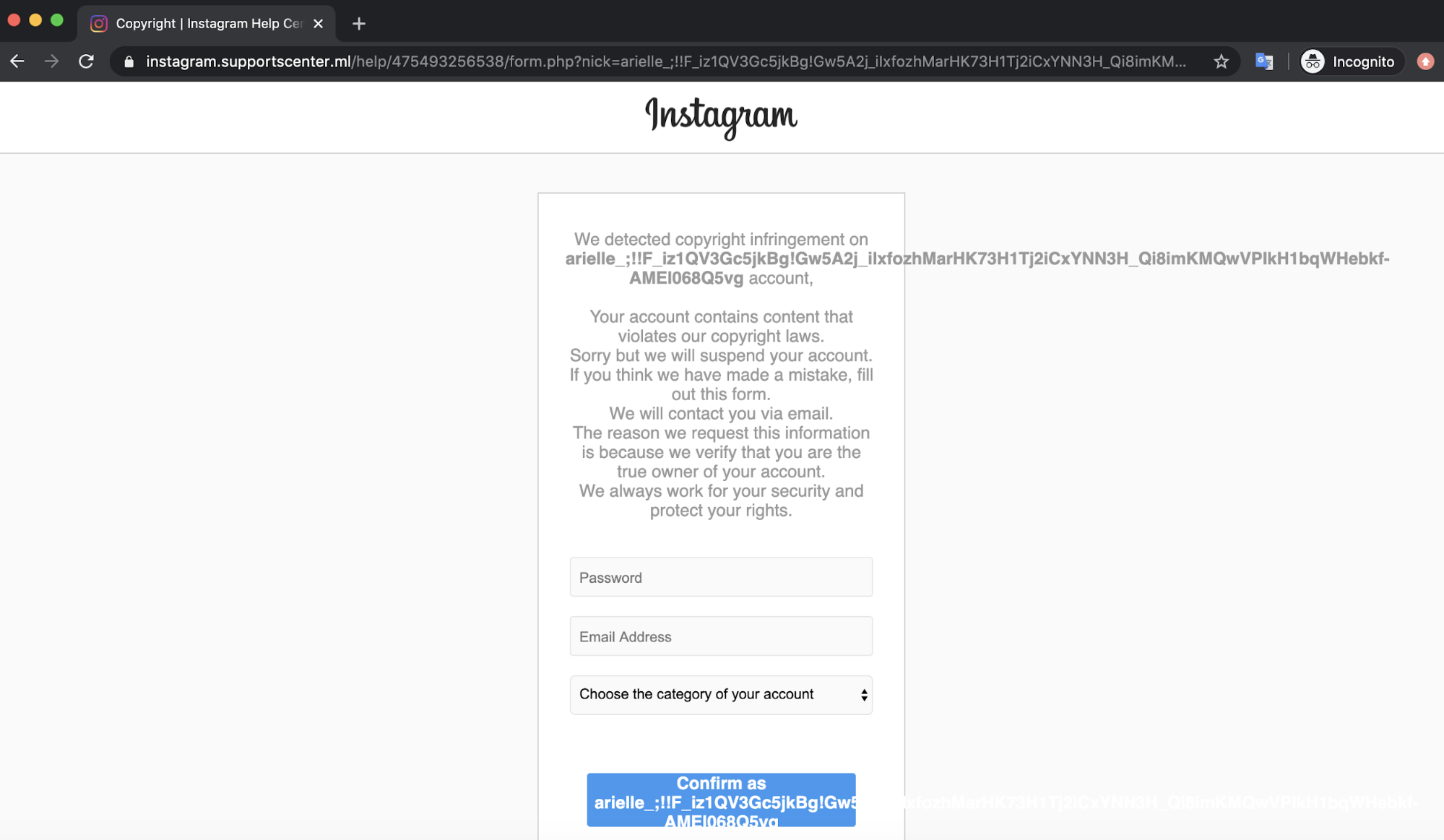
Social Media Impersonation Emails Lead to Phishing Sites
The appeal form within each email directs recipients to false login pages hosted on lookalike domains.
In the Instagram attack, the attackers created a fake Instagram login page where the username at the top and on the confirmation button appears to be different for each email recipient.
The attackers orchestrated their Facebook attack slightly differently. The user must be logged into their Facebook account since the link to the fake login form is located on a Facebook notes page, which can be created by any user. IT's interesting to note that this landing page is made to look like the Facebook Help Center to further trick recipients.
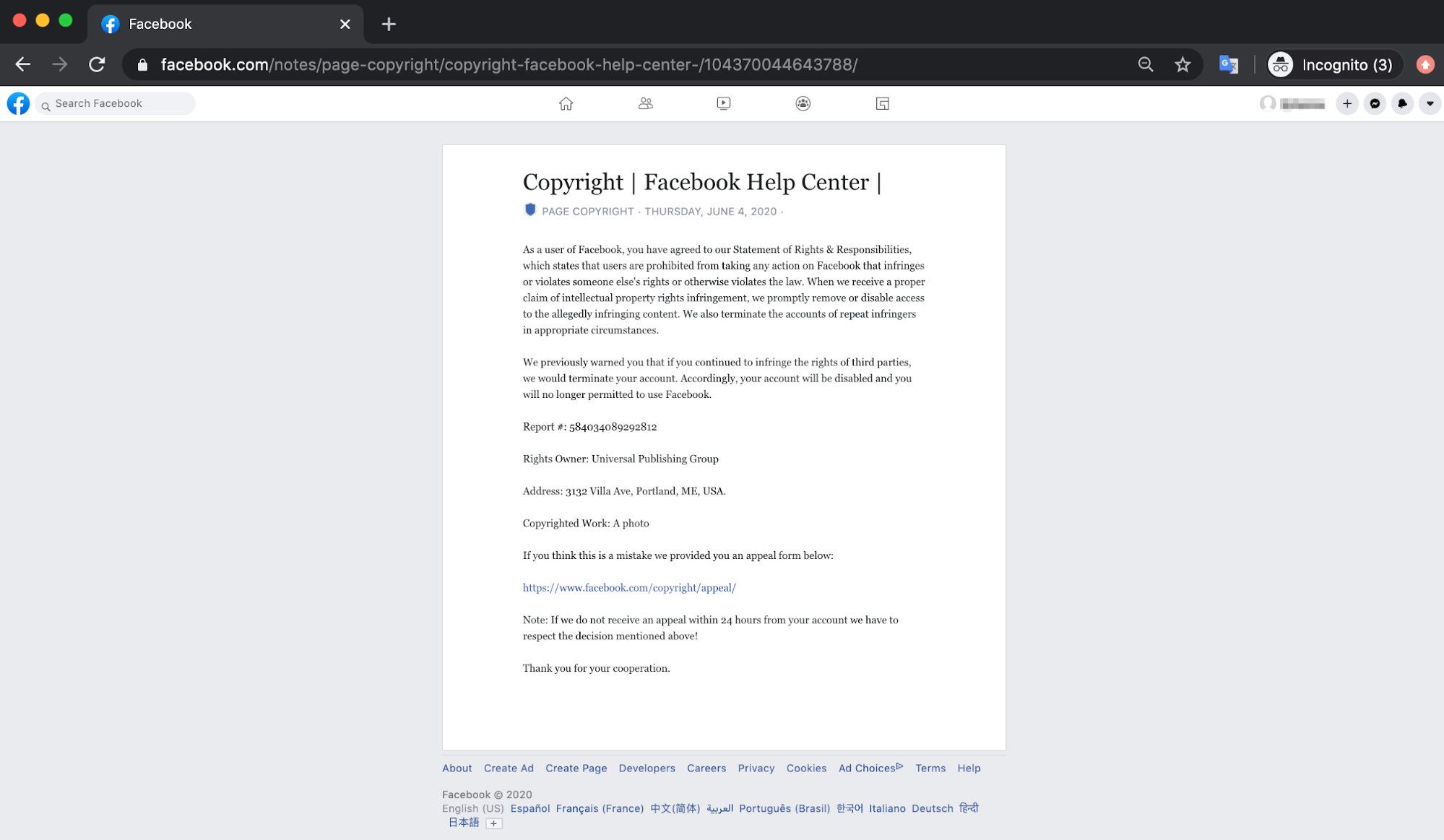
This note leads to the fake login page, where the user inputs their credentials. This attack is particularly malicious for enterprises, given that personal Facebook accounts are linked to business profiles.
And the Twitter login page is hosted on the lookalike domain; at a casual glance, users would be hard-pressed to see that this is not the real login page and after entering their credentials, it would be too late.
Why Social Media Impersonation Attacks are Effective
Since the beginning of the year, social media impersonation attacks like these have affected a substantial number of Abnormal customers. Roughly 60% of all attacks observed this year occurred in the past two months. Affected industries include media conglomerates, talent agencies, print and digital services, and the hospitality sector. We believe that this uptick since COVID-19 began could be because attackers are taking advantage of their targets being more active on social media. These trends are expected to grow with other major co-occurring events.
A key reason these attacks are effective is the language used in the email body. In each case, the email claims the recipient has violated the terms of service for the platform and thus the platform has decided to suspend the recipient's account. The emails also provide an opportunity for the recipient to reinstate their account if they act within a certain period of time. Because of the urgency this creates, attackers are hoping the recipients will overlook suspicious signals and provide login credentials to the account. Once accessed, the attacker can make posts on behalf of the individual or organization, send messages, or use it to attack other accounts. In some cases, they can also hold account access for ransom, hoping that the organization will pay to reinstate the account.
To learn more about how Abnormal can protect your employees from these impersonation scams, request a demo today.






