Skype Impersonated in Microsoft 365 Attack
Skype is used prolifically in both casual and business settings. As a result of its affiliation with Microsoft, it is a popular choice for attackers to impersonate in order to trick victims into handing over their Microsoft credentials.
Summary of Attack Target
Platform: Office 365
Email Security: IronPort
Payload: Malicious Link
Technique: Impersonation
Overview of the Skype Impersonation Attack
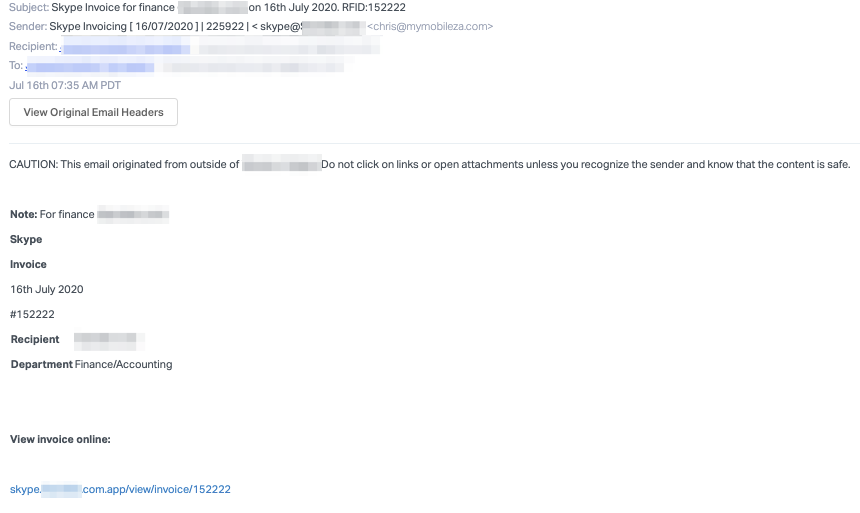
In these attacks, the sender impersonates an automated Skype invoice notification and uses brief language. The message notes it is for the finance department and contains a link to the supposed invoice.
If a recipient clicks on the link provided, they are brought to a replica of the Microsoft sign-in page which mimics a legitimate Microsoft login page and includes the Skype logo above the sign-in location. It should be noticed though that the URL leads to 'skype-online51877.web.app' which is not associated with either Skype or Microsoft.
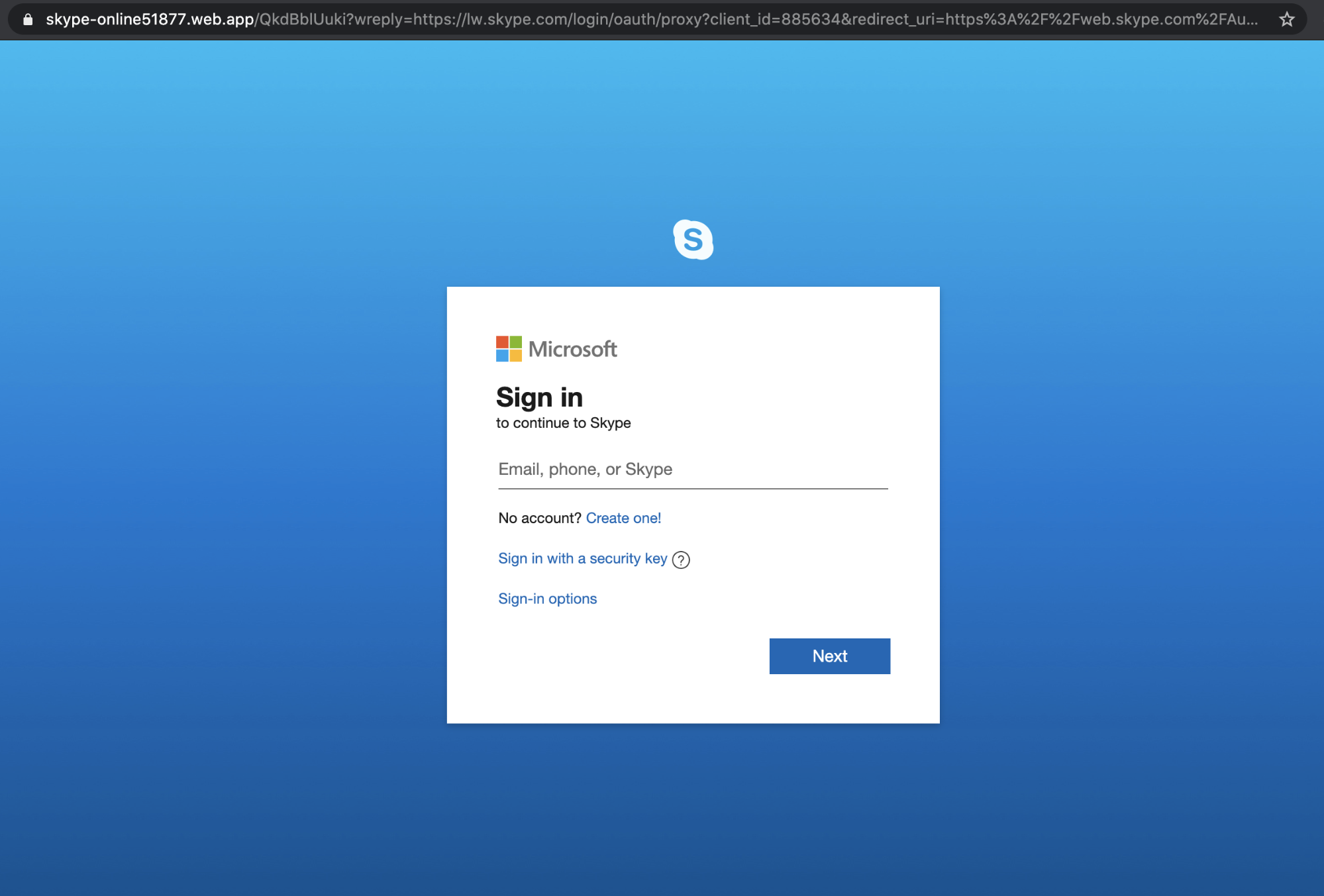
Nonetheless, the landing page looks extremely convincing and if a recipient were to enter their credentials, they risk exposing sensitive information found within their Microsoft account. This is particularly nefarious given that these credentials also give access to Office 365 where the attacker can access existing email conversations or use the account to send attacks on coworkers, partners, and customers.
Why the Skype Impersonation Attack is Effective
Within the email, the attacker includes references to the recipient’s organization and a note that the message is for the finance department. Here, the attacker is hoping that even if the recipient is not from the finance department, they will still follow the link or send it to the “appropriate” individuals. By mimicking an official application, attackers hope that the recipient will be less likely to scrutinize the content of the message and be more susceptible to the attack.
In addition, the payload link is concealed in the text. However, when clicked, it reveals the link used is hosted on Branch.io, which is a service that conceals the real link and tracks link usage. This attack is sophisticated in the use of link tracking, as the attacker is able to change the destination of the redirect link based on the collected link usage. In this attack, the first few clicks on the link directed to the Skype phishing page. However, on subsequent clicks on this link, it directs to the real Microsoft website. The attacker does this in order to bypass security measures that crawl links.
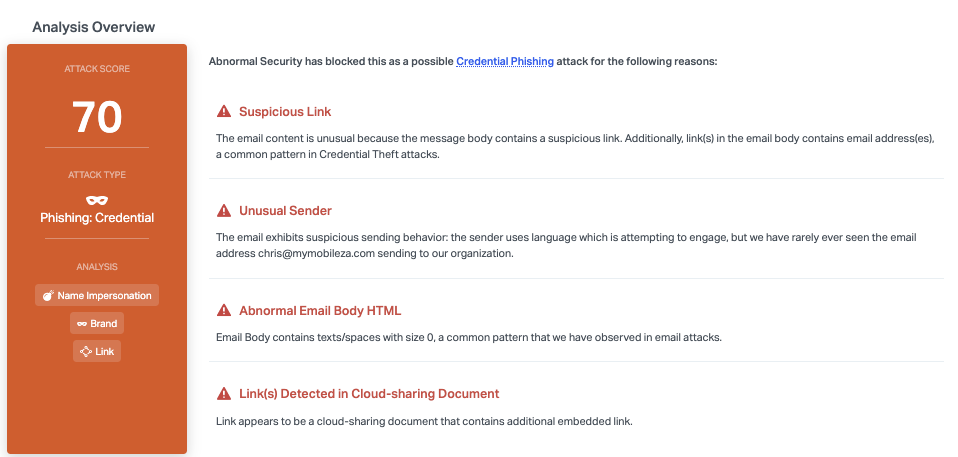
Abnormal Security blocks this by detecting specific aspects of the email, including the suspicious links, particularly the additional embedded links, and the unusual sender. We're also able to detect that the body text contains spaces with a size zero font, which is a common pattern within email attacks.
To learn how Abnormal can protect you from Skype and Office 365 attacks, see a demo today.






