Abnormal
for Box
Analyze human behavior to unpack who is accessing Box.
See a Demo

PROBLEM
Threats to Box Are Hard to Contain
Subheading text goes here
Attackers Want to Break Open Box
Despite the efficacy of Box Shield, attackers continue to gain access to the sensitive data housed by Box’s 97,000+ customers.
Security Teams Have Limited Visibility
Security Teams Have Limited Visibility
With a countless number of users, Box environments are highly complex and often not owned by security teams.
Traditional Solutions
Fall Short
Traditional Solutions
Fall Short
86% of security teams feel they are not sufficiently equipped to stop threats like account compromise in the cloud, potentially leaving Box wide open.
How Abnormal Secures Box
Gain Visibility into Box Activity
In order to protect the thousands of files your organization stores in Box, you need visibility. With an API integration with Box, Abnormal ingests and normalizes sign-in event data—analyzing rich telemetry related to Box access patterns and building a behavioral baseline of what “normal” Box sign-in behavior looks like.

Contextualize and Investigate Threats to Box
When Abnormal detects suspicious deviations in how humans are accessing Box, behavioral AI automatically triggers and builds a Case with a contextual timeline of Box activity correlating against cross-platform email, SaaS, and cloud activity for each suspicious user for each suspicious user. It then alerts the SOC to threats that may have otherwise gone unnoticed.

Simple, Effective Security for Box
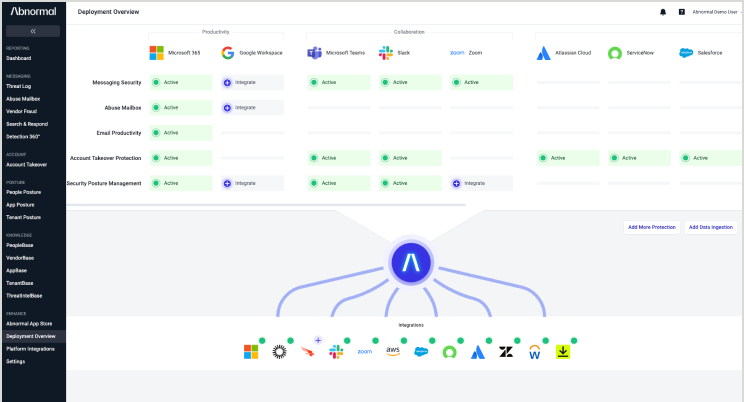
Data Integration Platform
Easily integrate and ingest behavioral signals from multiple cloud applications and services, including Box, with cloud-native API architecture.
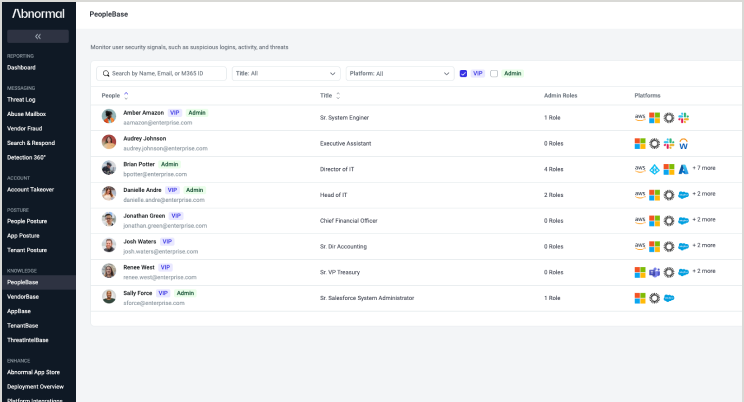
PeopleBase
Explore sign-in activity, permissions, and admin roles in Box for every person in your cloud environment through comprehensive behavioral profiles.
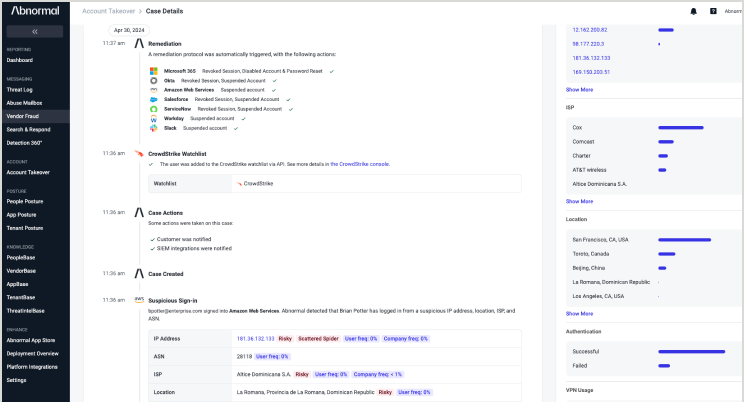
Complete Account
Takeover Protection
Extend uniform protection from account takeovers across dozens of cloud applications and services, including Box.
Abnormal is just what we needed—a full-service tool that automatically does what we were doing manually before.”
— Mark Baldus, IT Infrastructure and Operations Manager, Dudek
Related Resources
Understand Human Behavior in Your Cloud Environment
Gain dynamic visibility into how humans in your organization are accessing your most important cloud applications and services.
Request a Demo
Request a Demo





