New Recruitment Scam Leads to Vishing
With unemployment on the rise, attackers are exploiting individuals in search of new positions. This method makes use of targeted social engineering techniques, combining email and mobile platforms, to reap information from recipients. In this attack, malicious actors pose as job recruiters to lure victims into an over-the-phone scam.
Summary of Attack
- Platform: Office 365
- Email Security Bypassed: Office 365
- Payload: Text/Vishing
- Technique: Impersonation
Overview of the Job Recruiting Vishing Scam
The attack impersonates an email from a recruiter at a non-specified career website. It appears to be directed to the recipient specifically. It is well written and contains pleasantries, a brief description of the job requirements, the payment amount, pay schedule, conditions, and the HR contact—all the major details with the exception of the company name. At the conclusion of the email, the recipient is directed to reply to the email with their phone number for further consideration.
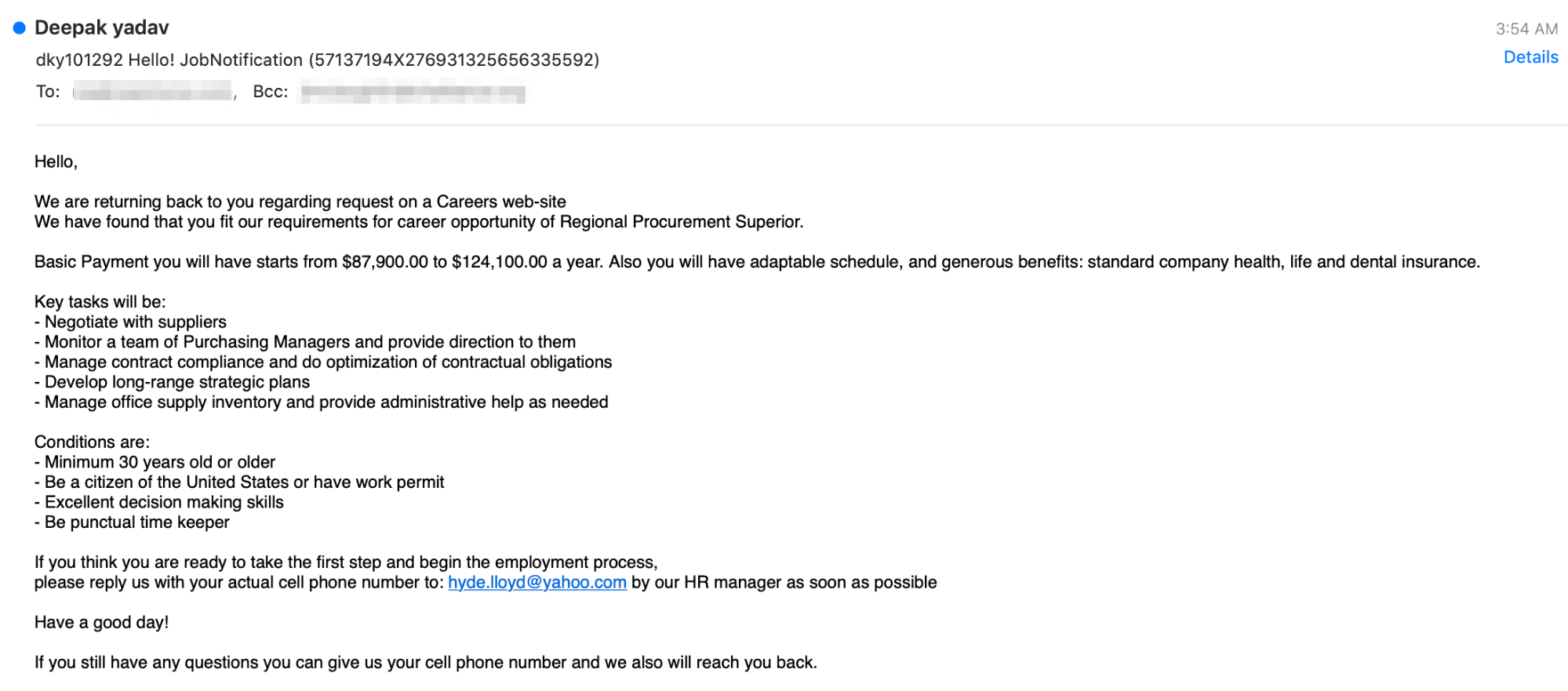
The practice of luring victims into a scam performed over the telephone is known as vishing, a combination of voice and phishing. If the recipient responds to the email with their personal contact information, attackers can use it for another step in an attack on this recipient, for the purposes of a scam, or potentially to launch an attack on other individuals with whatever information is divulged. We don't know exactly what direction this attack would take, but recipients will want to avoid passing along any information.
Why the Job Recruiting Vishing Scam is Effective
The job landscape is rapidly shifting during the pandemic and employees are uncertain whether they will remain employed. Along with this shift, employees are seeking other positions in more favorable locations. When presented with this opportunity, it is easy to miss details that point out red flags, such as the company name being omitted, in a rush to contact the job poster.
Despite the vague origin, the email is crafted convincingly. The format, grammar, and context are written in such a way that makes the recipient believe the email request is sound, and the request for a phone number isn't extremely unusual for job seekers.
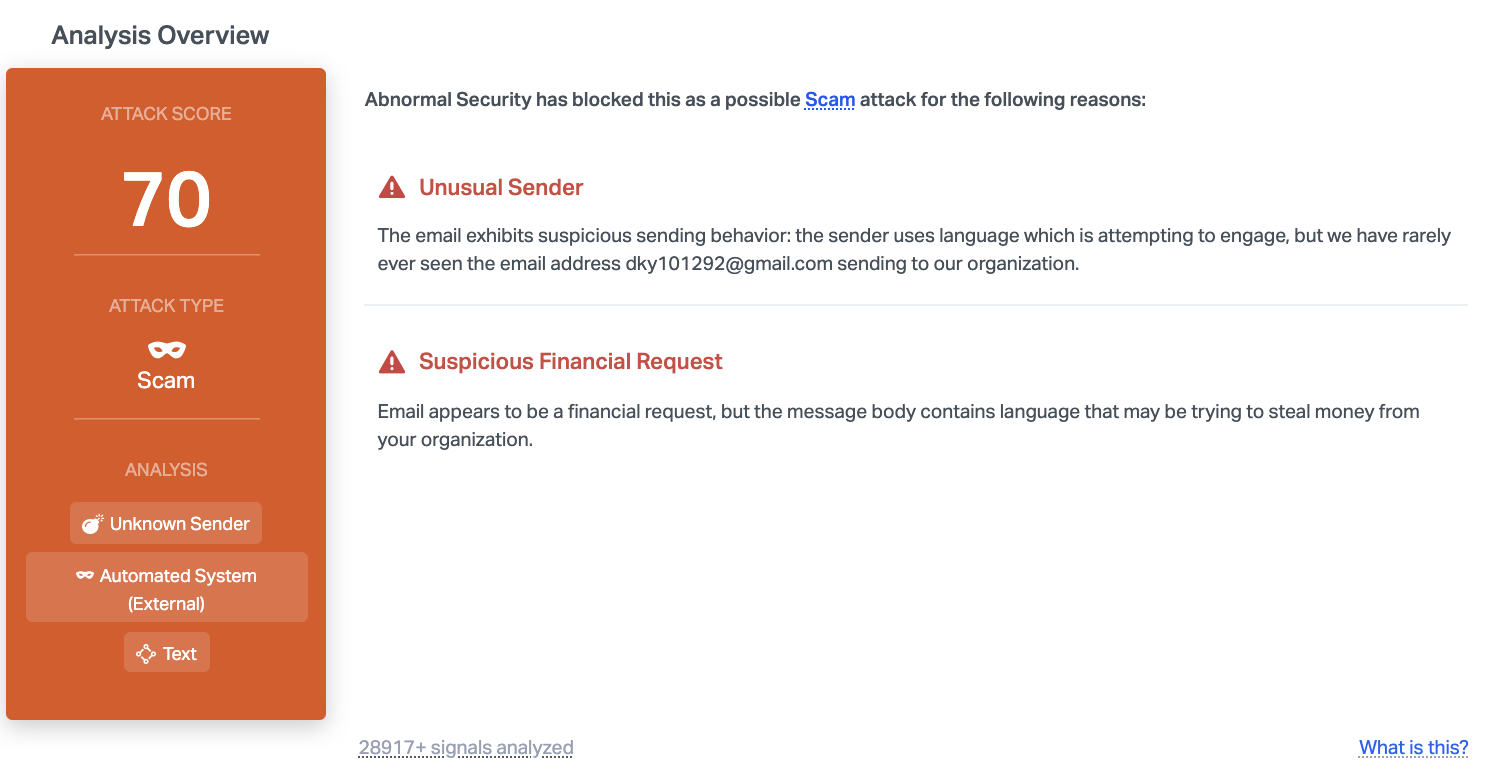
Abnormal can detect this attack because of the unknown, unusual sender. Despite using a Gmail address, which inherently has a good reputation, the specific email had never been used in communication with the organization, and it appears to be automating an external system. When combined with the text of the email, it appears malicious enough that Abnormal can block it before it reaches employees.
To learn more about how Abnormal can protect you from email attacks that lead to vishing, request a demo today.
Get AI Protection for Your Human Interactions







