DHL Impersonated in Shipping Return Scam
As the world is stuck inside, shipping items has increased and cybercriminals are taking notice. In a recent scam, attackers created an email to impersonate DHL and claimed that a package intended for the recipient was been returned to the sender. As a result, the recipient must pay €50 in order to deliver the package.
Summary of Attack Target
- Platform: Office 365
- Email Gateway: Proofpoint
- Victims: Employees
- Payload: Malicious Link
- Technique: Impersonation
Overview of the DHL Shipping Scam
In the email, attackers claim that the recipient must visit a website and pay €50 to obtain a PIN code, which they must then send to an email address (ostensibly DHL, but actually an email address for the attackers) in order for their package to be delivered.
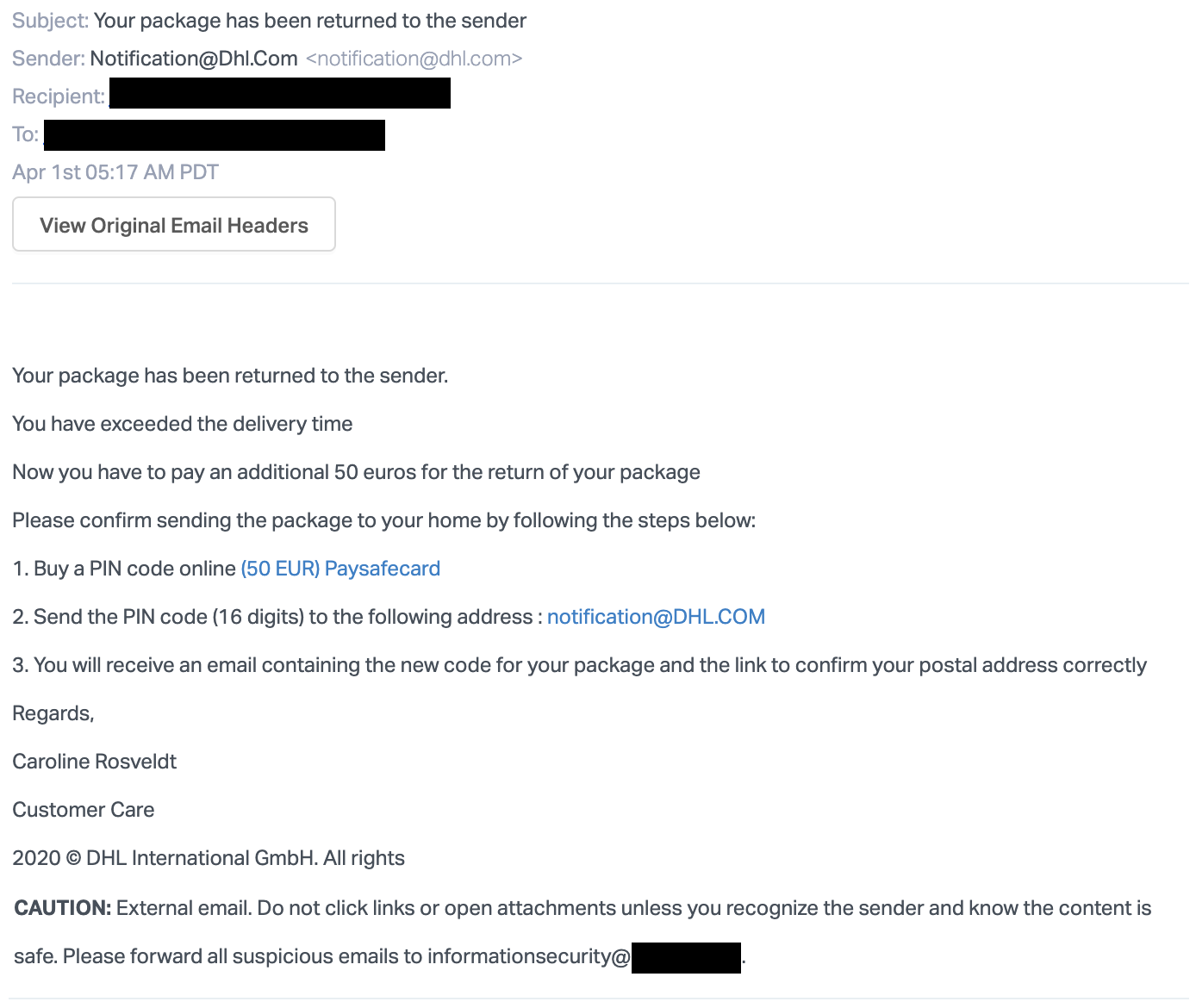
This attack itself uses no malicious links, as the link to obtain the PIN that attackers request is a legitimate service known as Paysafecard. However, it should be noted that DHL would never ask its customers to use this service to have a package delivered.
Additionally, the email that the attackers ask recipients to send the PIN to is different from the email displayed. The attackers write that the email to send the PIN to is notification@dhl.com, but the link actually directs victims to an email address controlled by the attackers.
Those who fall victim to this attack will lose the €50 that is paid to the attackers. While this isn't a large sum of money, it does showcase how attackers can make thousands from a single email sent to multiple people.
Why This DHL Shipping Scam is Effective
As with many attacks, this one leverages urgency to ensure that victims scrutinize the email less than they might otherwise. In this case, the email claims that "You have exceeded the delivery time," which puts pressure on the recipient to act quickly.
There is also the case of the hidden URL. Although the email that the attackers ask their victims to send the PIN to is written as notifications@dhl.com, the embedded link actually has victims sending the PIN to an email controlled by the attackers. If victims don't check the email before sending the PIN, they would have no idea that it's being sent somewhere other than where they expected. Furthermore, the attack leverages a legitimate service in Paysafecard that is used to pay for items.
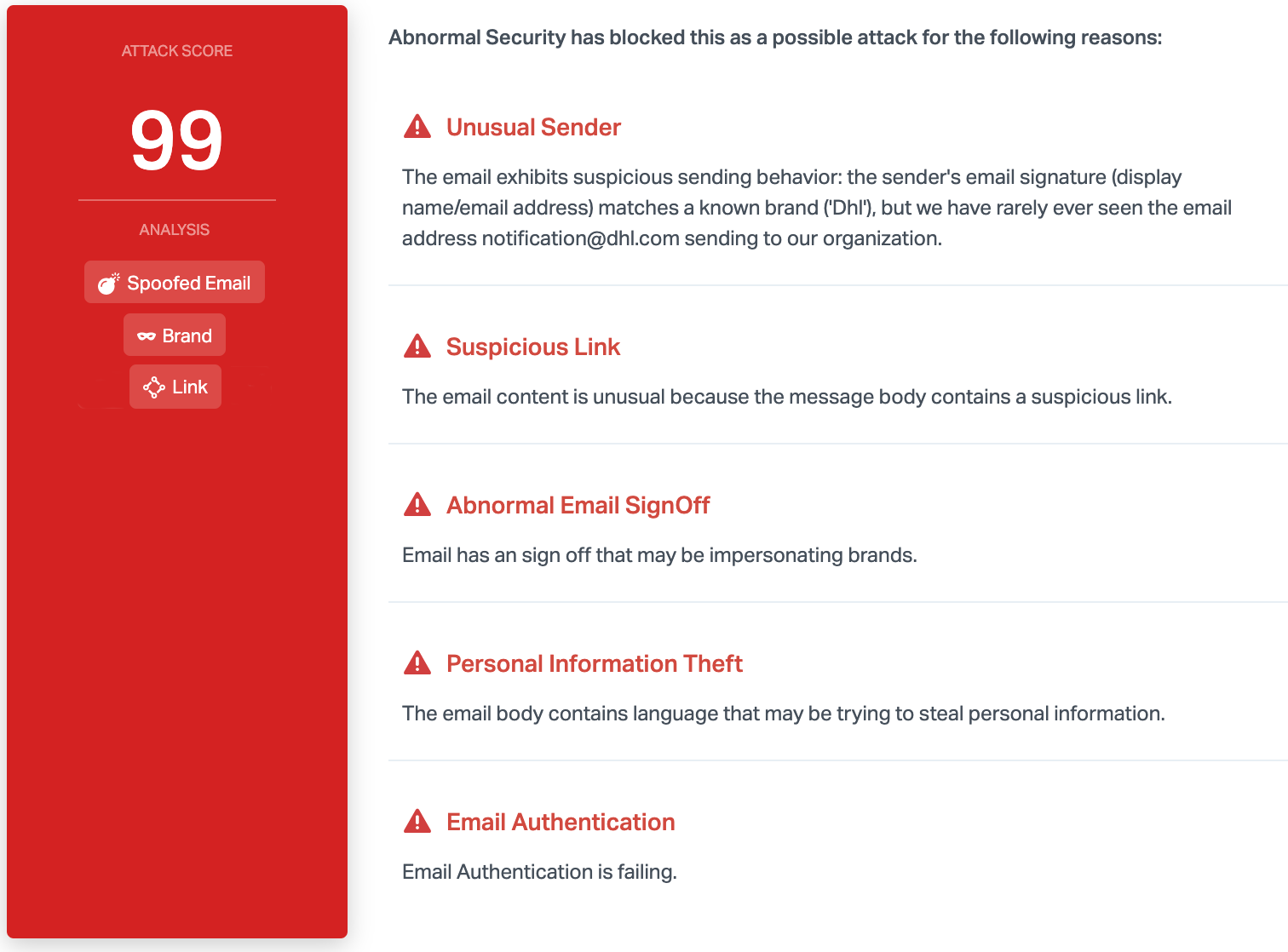
Abnormal is able to stop this attack due to a variety of reasons. Most notably, email authentication is failing and the sender's display name matches a known brand, but has an abnormal email signoff that indicates it may be suspicious. Combined with the suspicious link and the financial instructions, this provides the basis for discovering the malicious attack.
To learn more about how Abnormal can protect you from shipping scams and other advanced threats, see a demo of the platform today.
Get AI Protection for Your Human Interactions







