Executive Impersonated in Vendor Invoice Fraud Scheme
Executive impersonation is one of the most prevalent forms of business email compromise because it is typically easy to do. The attacker only needs to know the name and job type of a high-profile executive, and then they can use that name to prompt unsuspecting employees to send wire transfers, buy gift cards, or provide access to sensitive data. In this case, an executive was impersonated to commit vendor invoice fraud.
Summary of Attack
- Platform: Office 365
- Email Gateway Bypassed: IronPort
- Victims: Accounting Employee
- Payload: Invoice Attachment
- Technique: Executive Impersonation
About the Executive Impersonation Attack
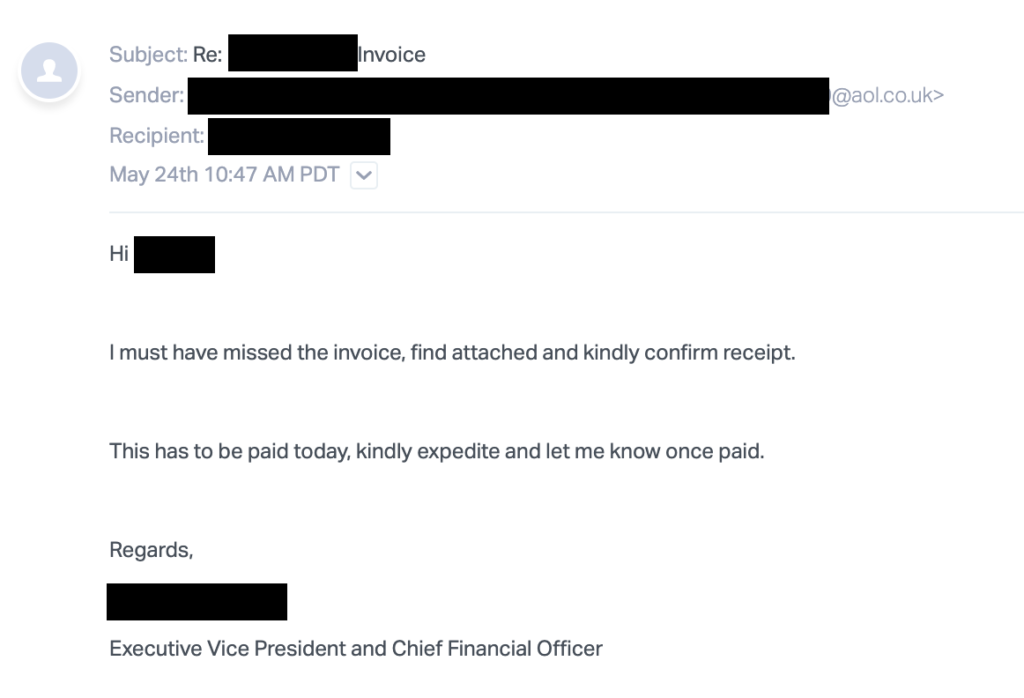
In this attack, the threat actor posed as an executive at the organization and asked an employee in accounting to pay an invoice, but failed to attach the invoice to the initial email. This may have been intentional in an effort to fool traditional email security systems and start the conversation. Once the employee in accounting responded to the initial email, they received the second email shown here.
The attached invoice looked legitimate but contained banking information that would've routed the wire transfer to an account that the cybercriminal owned.
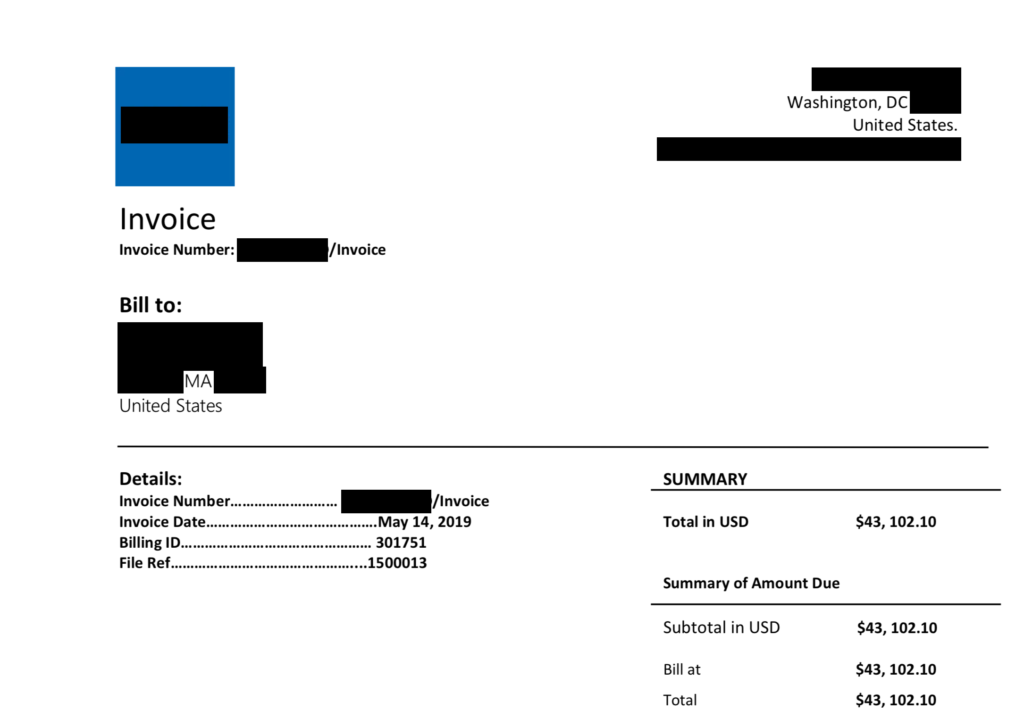
While Abnormal caught the attack, had it been successful, the attacker would have stolen nearly $43,000 from the targeted organization.
Why the Invoice Fraud Attack Bypassed Existing Security
As part of the attack, the attacker posed as an executive communicating with a low-level employee. This is purposeful, as the low-level employee would have recognized the name and thus would have been more likely to engage with the attacker. In addition, the attacker asked his victim to pay the invoice immediately, and this urgency often causes employees to forego the scrutiny they should be giving these types of email requests.
The attacker was able to bypass Microsoft Exchange Online Protection and Defender for Office 365 by using new or existing domains that did not have a negative reputation. However, Abnormal was able to catch this email due to the mismatch between the display name and the email address, as well as an abnormal email response.
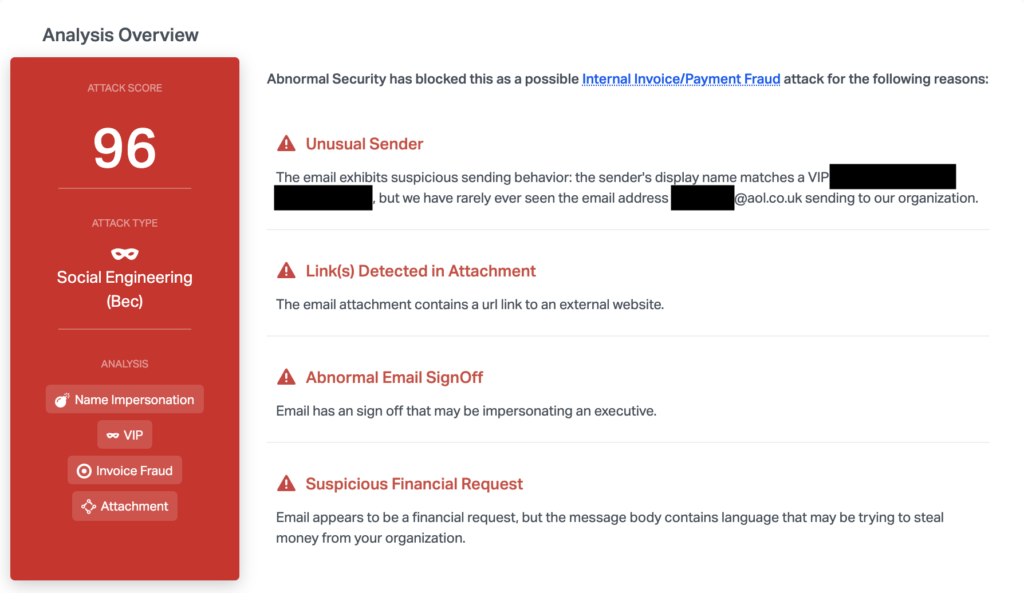
These factors, combined with the suspicious financial request, made it possible to understand that this attack was malicious.
Want to see how Abnormal can catch executive impersonation attacks at your organization? Request a demo to get started.
Get AI Protection for Your Human Interactions







