COVID-19 Messages Part of Credential Phishing Attack
With many employees forced to work from home because of COVID-19, cybercriminals can take advantage of the fear and uncertainty caused by the pandemic. This attack features a new phishing scheme around returning to the office.
Despite (or perhaps because of) the rise in COVID-19 cases, companies are now providing status updates on when offices are expected to reopen and when employees can return to working there. In this attack, scammers impersonate an internal company memo about when the company will return to the office to steal employees' credentials.
Summary of Attack Target
- Email Security Bypassed: G Suite
- Victims: Employees
- Payload: Attachment
- Technique: Impersonation
Overview of the Back-to-Work Phishing Attack
The email is disguised as an automated internal notification from the company, as indicated by the sender display name. The sender's actual address is 'news@newsletterverwaltung.de’, an otherwise unknown party and the IP originates from a blacklisted VPN service that is not consistent with the corporate IP. This indicates the sender is impersonating the automated internal system.
The email is sent to a specific employee, requesting a call back with an attachment and text that make it seem like the recipient has received a voicemail.

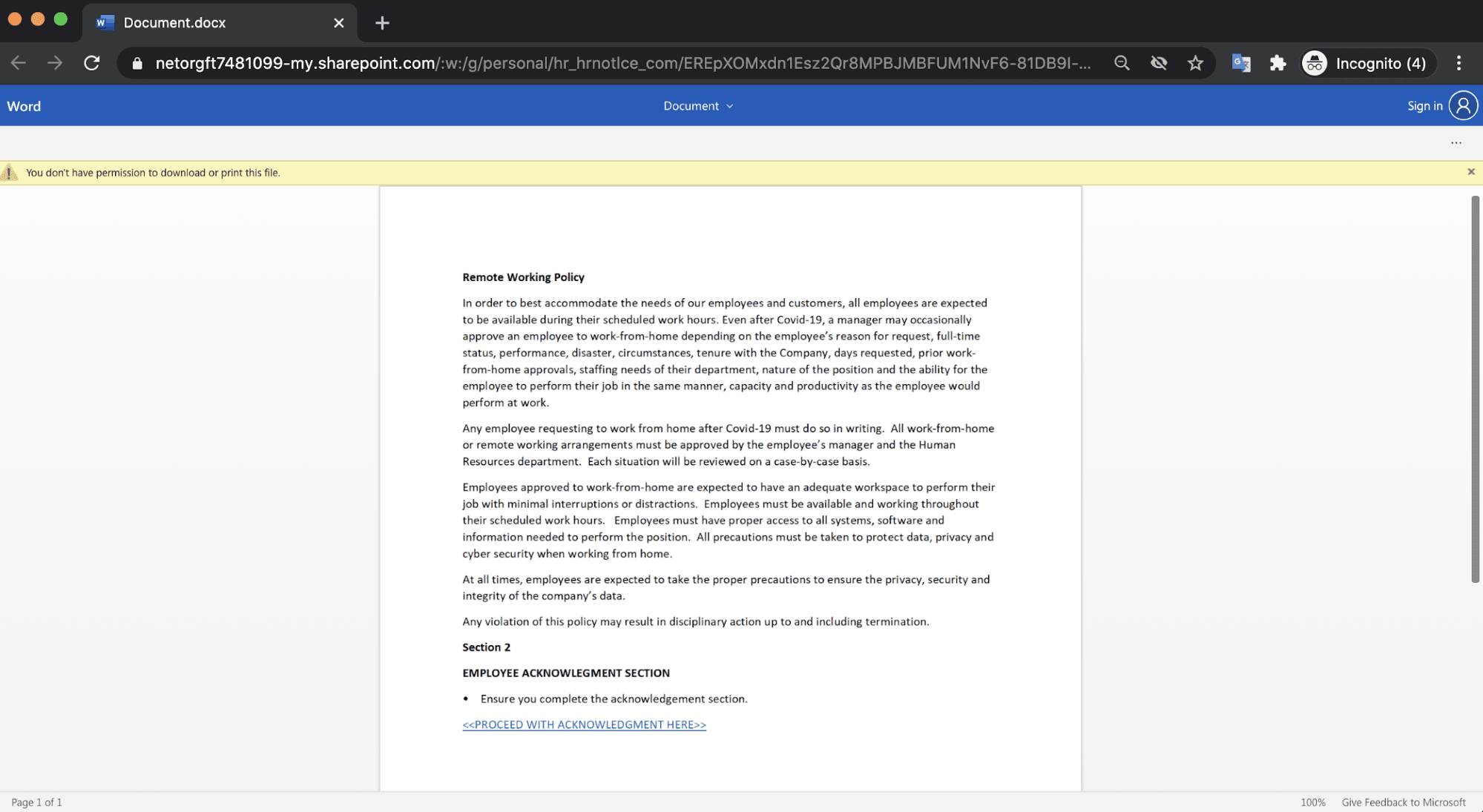
The email contains an HTML attachment containing the recipient’s name, which encourages the recipient to open it. By clicking on the attachment, the user is redirected to a SharePoint document with new instructions on the company’s remote working policy. Underneath the new policy, there is text that states “PROCEED WITH ACKNOWLEDGEMENT HERE”.
Clicking on this link redirects the user to the attack landing page which is a form to enter the employee’s email credentials.
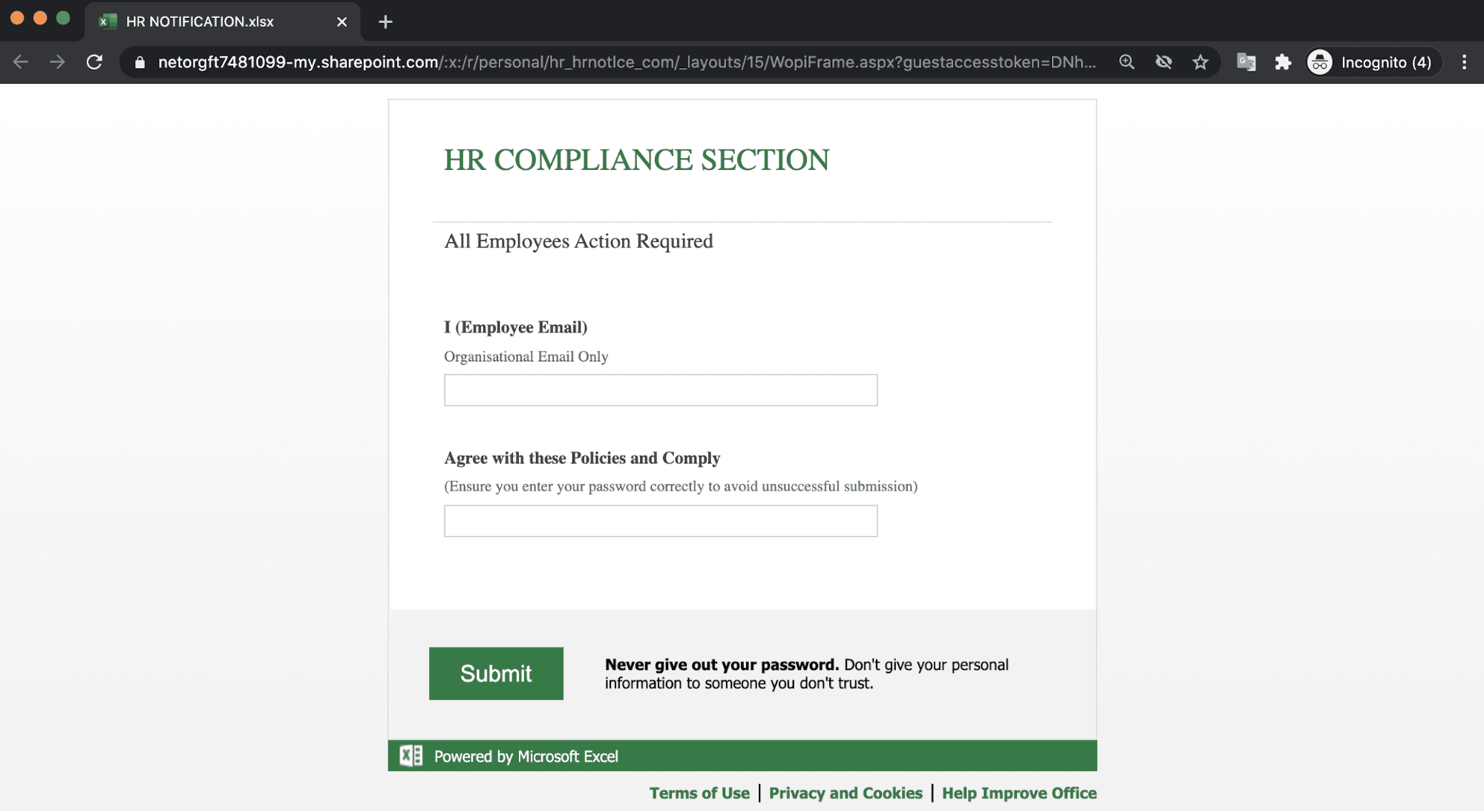
If the recipients fall victim to this attack, the login credentials for their email account will be compromised, and the attackers will gain access to sensitive corporate and personal information. Although there is an explicit message telling those who fall on this landing page that they should never give out their passwords, there may be some number of recipients who still input their credentials.
Why the Back-to-Work Phishing Email is Successful
This attack utilizes growing concerns regarding company safety protocols during the COVID-19 pandemic. This email sets a short deadline for when employees must acknowledge that they have received this message and complete the form.
And because employees are more likely to provide credential information to others within their organization, the attacker attempts to impersonate the company’s internal messaging system and HR department.
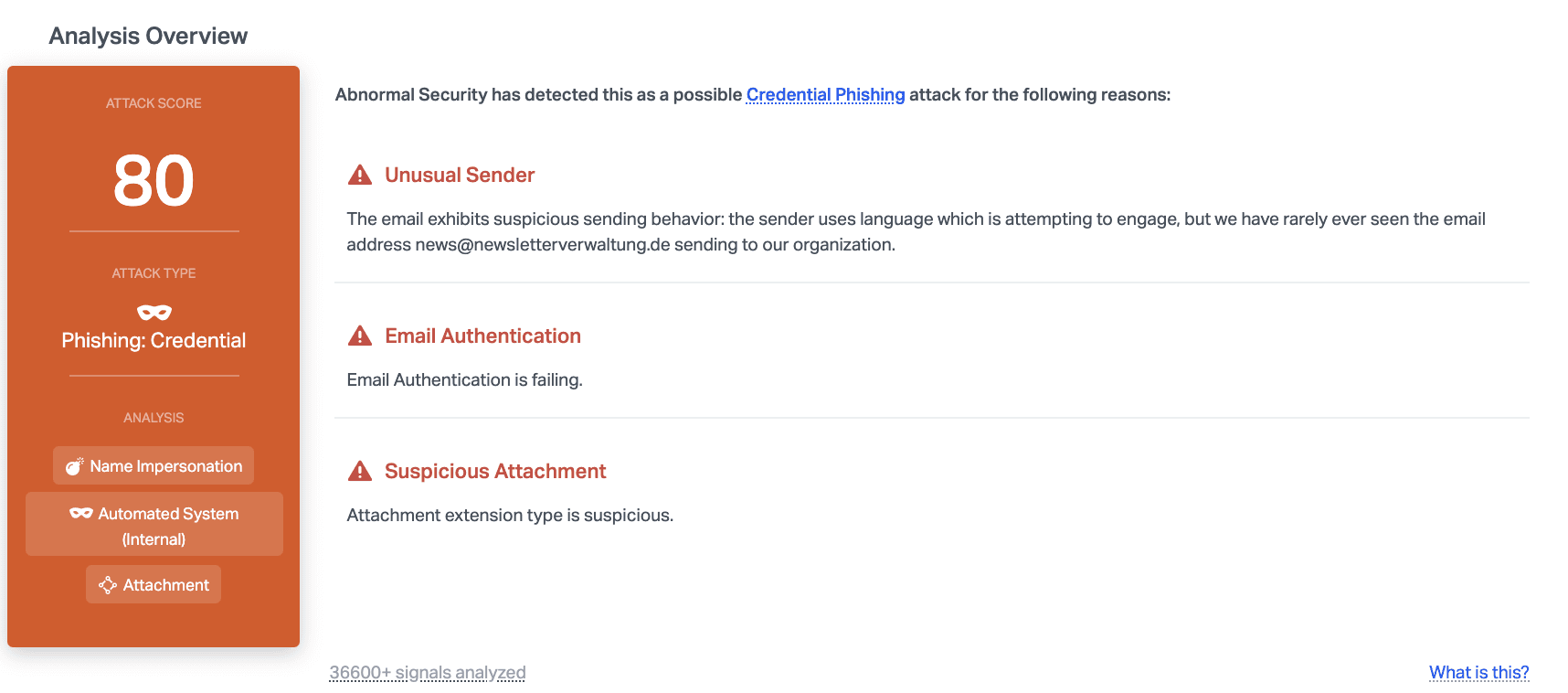
Abnormal detected this malicious email due to the unusual sender, the failed email authentication, and the suspicious attachment. These three things combined provide enough insight to make this email dangerous and stop it before it hits inboxes.
Learn how to protect your company against brand impersonation and other types of credential phishing attacks by requesting a demo of the Abnormal platform.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.

