Department of Labor Impersonated in Identity Theft Attack
We're nearly a year into the pandemic and scammers are still taking advantage of the financial hardship caused by COVID-19. In a recent attack, they impersonated a government entity and offered supposed relief funds to gain access to sensitive and identifying information.
Summary of Attack Target
- Platform: Office 365
- Bypassed Email Security: Proofpoint
- Victims: Employees
- Payload: Link
- Technique: Impersonation
Overview of the Department of Labor Impersonation Attack
The attacker impersonates the New York Department of Labor by disguising their identity with the display name “noreply@labor.ny.gov” and displaying the New York State logo at the top of the email. However, a closer look reveals the true sender is “naij30@naija9icevibes.com”, a Panamanian-registered domain with no association to the New York state government.
The attacker claims that the government will administer a $600 relief fund to citizens who fill out the indicated form. The “click here” hypertext redirects the recipient to a webpage controlled by the attackers and mimics a New York state government page that asks for sensitive information such as name, address, date of birth, social security number, and driver’s license number.
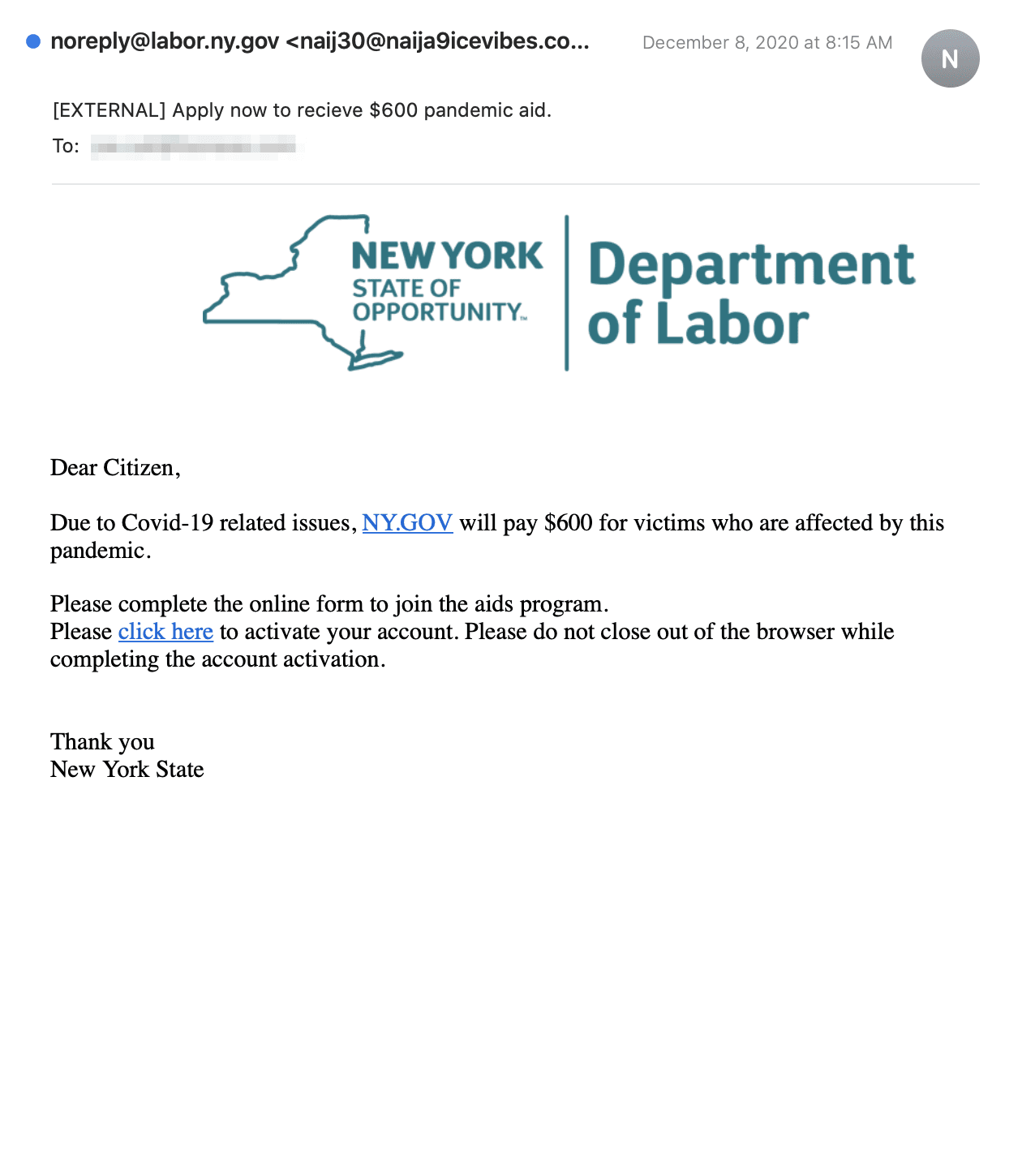
The email contains an embedded link that should supposedly lead to a NY.GOV site, but actually points to "https://thesender[.]org/fjc4". After clicking on the hypertext, the link redirects to “bo2.cloudns.cl/NYU/cnf[.]php”, a phishing page posing as a legitimate government website. Although this landing page displays the official New York state government logo, the URL is not associated with the New York Department of Labor. Instead, it is a trap for users to release valuable information in the pursuit of their promised COVID-19 relief fund.
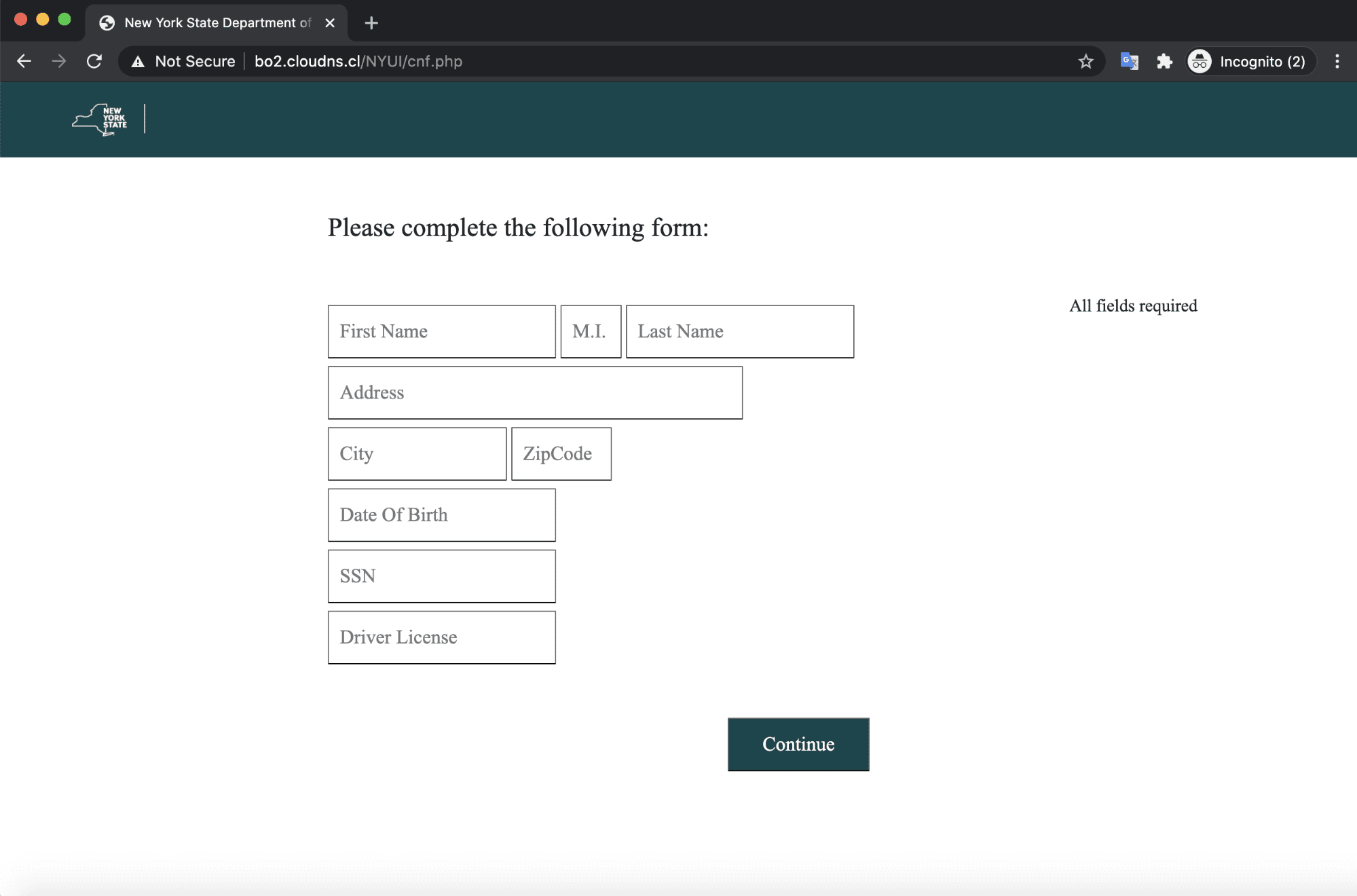
The landing page itself asks for not only basic information like name and address but also social security number and driver's license number—both of which could be used for nefarious purposes. If the recipients fall victim to this attack, they would release extremely personal information to the scammers, which could ultimately lead to identity theft and other fraud.
Why This Identity Theft Attack was Effective
Because this email is offering $600 in relief funds to those who might be suffering from financial hardship, the recipient is incentivized to act quickly in order to claim this offer. Additionally, by impersonating an official government entity, the email creates an air of authority and may seem more legitimate to the recipient, motivating the recipient to engage without delay. Americans have already received pandemic stimulus checks from the government, so a recipient of this email may truly believe that the government is offering additional relief as the pandemic continues.
In an additional effort to appear legitimate, the attacker employs the official logos of the New York state government in both the email and the fake form, creating a credible impression of a legitimate government entity.
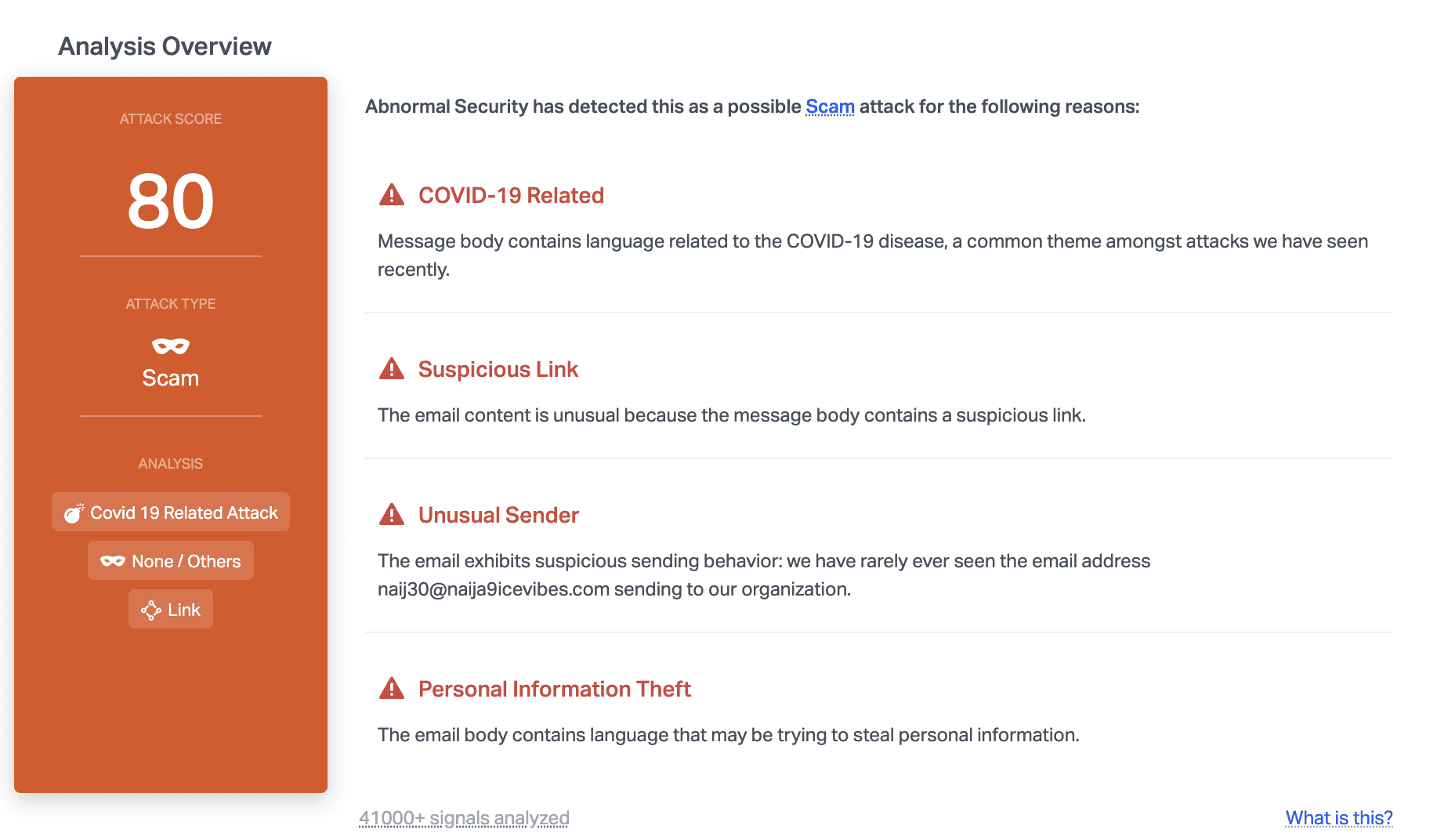
Abnormal stopped this email due to a variety of factors, including the unusual sender, suspicious link, and the language that indicates that the attacker may be attempting to steal personal information. We've also seen a large uptick in the number of attacks revolving around the COVID-19 pandemic, making this more likely to be an attack. Combined together, these factors help determine that the attack is malicious and is thus stopped before reaching inboxes.
If you're interested in stopping identity theft and credential phishing for your organization, see a demo of the Abnormal Security platform today.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.

