LogMeIn Impersonated in Credential Phishing Attack
We’ve seen an incredible uptick in collaboration software impersonations in the past month as the COVID-19 pandemic has forced people to work at home. Most of these attacks are associated with platforms like Google Workspace and Office 365, which can be leveraged by attackers to gain access to or assault other accounts. However, we've also seen a rise in attacks on Zoom, Microsoft Teams, and other collaboration tools.
In May, we began to observe new email attack campaigns impersonating LogMeIn, after previously seeing none. This is likely due to various news stories about the troubled infrastructure and security of video conferencing platforms, as cybercriminals can engage with victims and steal credentials while avoiding scrutiny.
Summary of Attack Taret
- Platform: Office 365
- Victims: Employees
- Payload: Malicious Link
- Technique: Impersonation
Overview of the LogMeIn Credential Phishing Attack
The email claims to be from LogMeIn, informing the recipient of a patch to a zero-day vulnerability in some of the company’s offerings. The user must update by following the link given, which impersonates an actual LogMeIn URL.
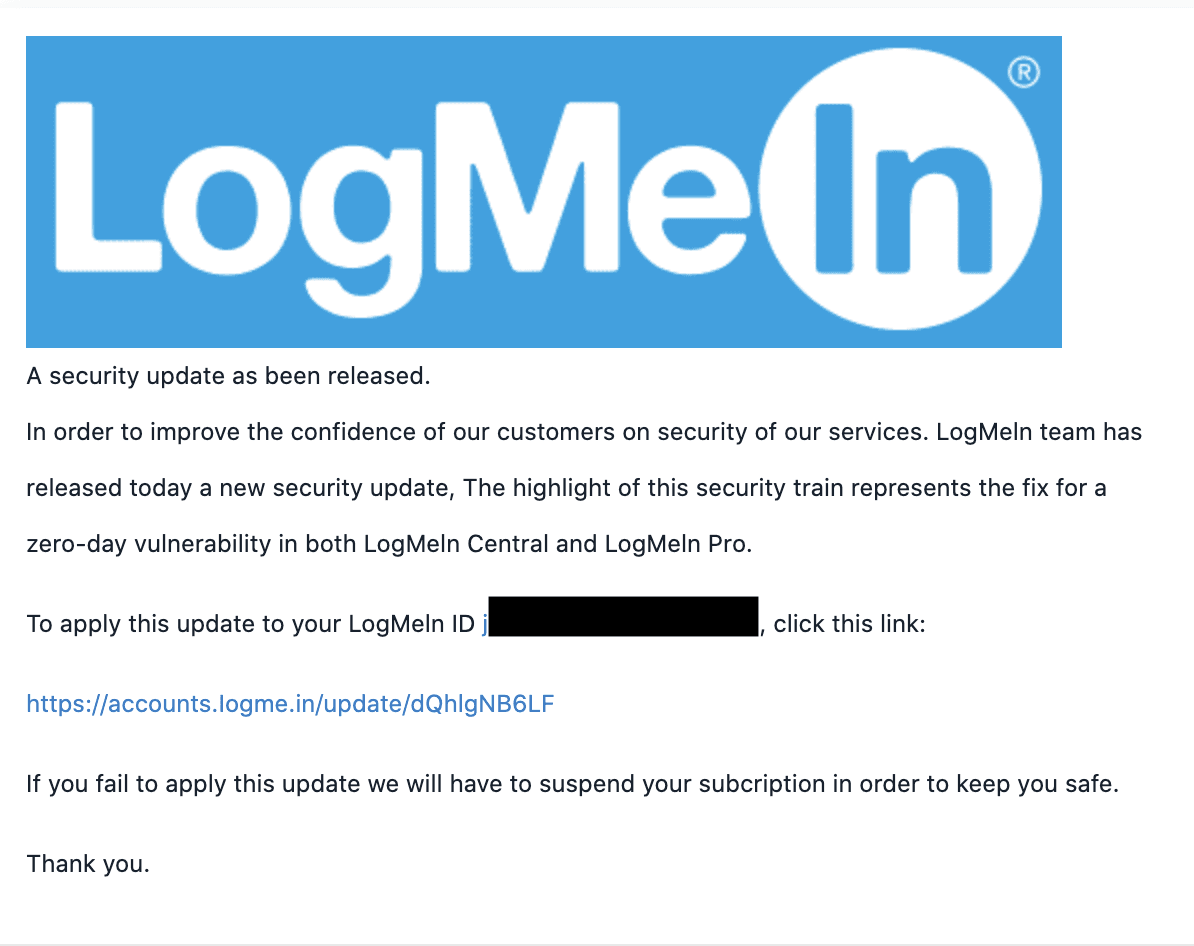
Users may be tricked by the fake URL, as it looks like what they would expect from the system. However, it redirects to a phishing page owned by the threat actor.
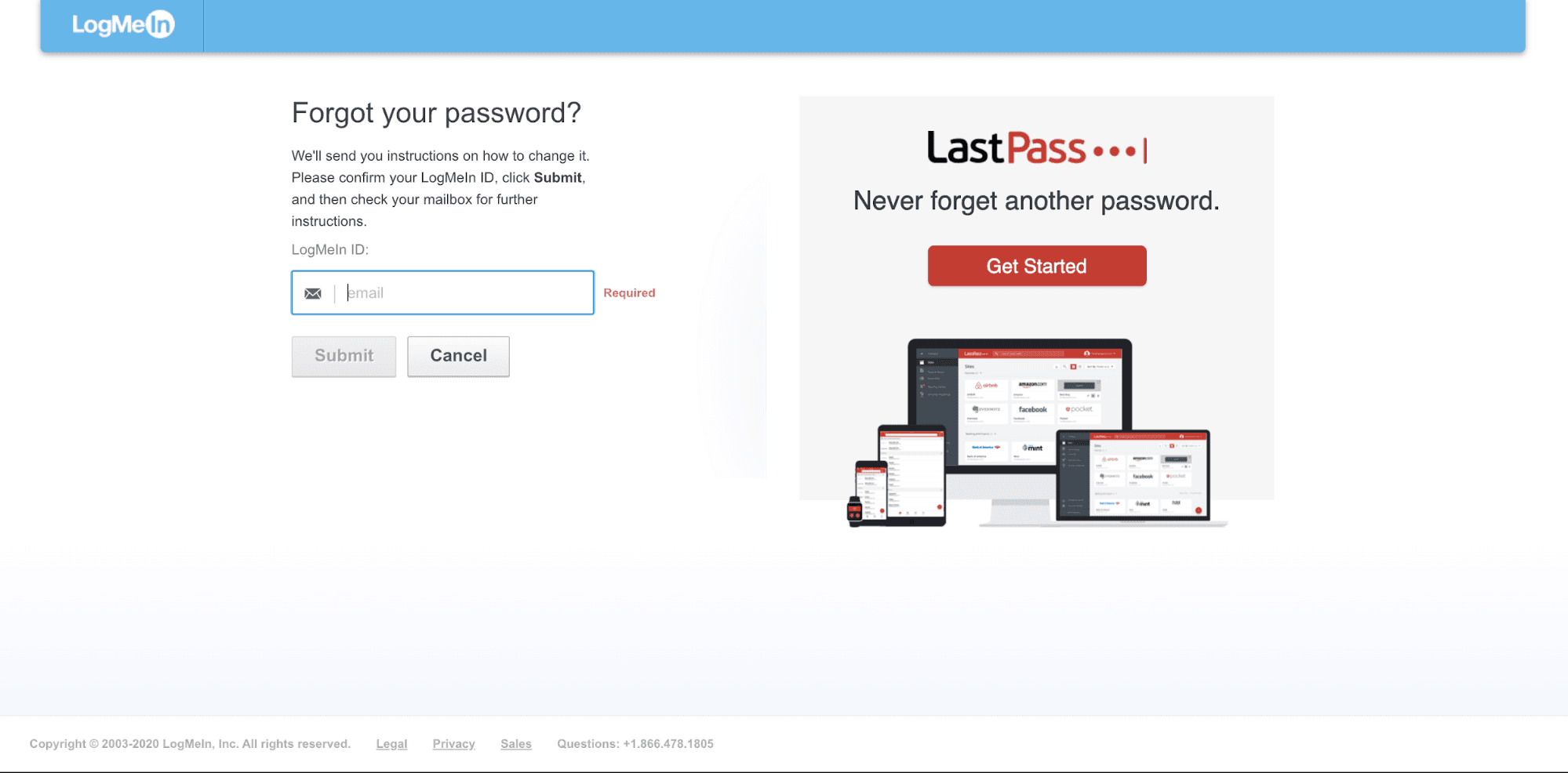
From here, the phishing page asks for email address and password. Should recipients fall victim to this attack, their login credentials to their LogMeIn account would be compromised. Additionally, since LogMeIn has SSO with LastPass as the parent company, it is possible the attacker may be attempting to obtain access to this user’s password manager.
Why the LogMeIn Credential Phishing Attack is Effective
Other collaboration platforms have been under scrutiny for their security, as many have become dependent on them to continue their work given the current pandemic. Because of this, frequent updates have become common as many platforms are attempting to remedy the situation. The cybercriminal is taking advantage of the situation, knowing that a recipient may be more inclined to update right now.
In addition, the link attack vector was hidden using an anchor text impersonation to make it appear to actually be directing to the LogMeIn domain. Furthermore, throughout this attack, imagery found in legitimate LogMeIn pages is found in both the email and the phishing page. Additionally, the LastPass image shows an in-depth knowledge of the impersonated company and its offerings.
Abnormal can stop this due to a variety of factors, including the suspicious sender and the malicious link. Even though the text of the link has been obscured, Abnormal can follow the actual URL to determine the malicious nature of both the email and the landing page. Combined with the body text, which showcases an attempt to gather information, it becomes obvious that this email is dangerous and it is blocked before entering inboxes.
Learn more about how Abnormal protects employees from credential phishing by requesting a free demo today.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.

