Inbound Email Security
Stop the full spectrum of email attacks with behavioral AI.
Watch Demo
See Product Tour

Email Attacks Have Increased in Sophistication and Severity
Costly
The average business email compromise attack costs organizations $125,000.
Frequent
89% of companies see a supply chain compromise attack each week.
Difficult to Detect
It takes an average of 308 days to identify and contain a breach.
How Abnormal Stops the Full Spectrum of Email Attacks
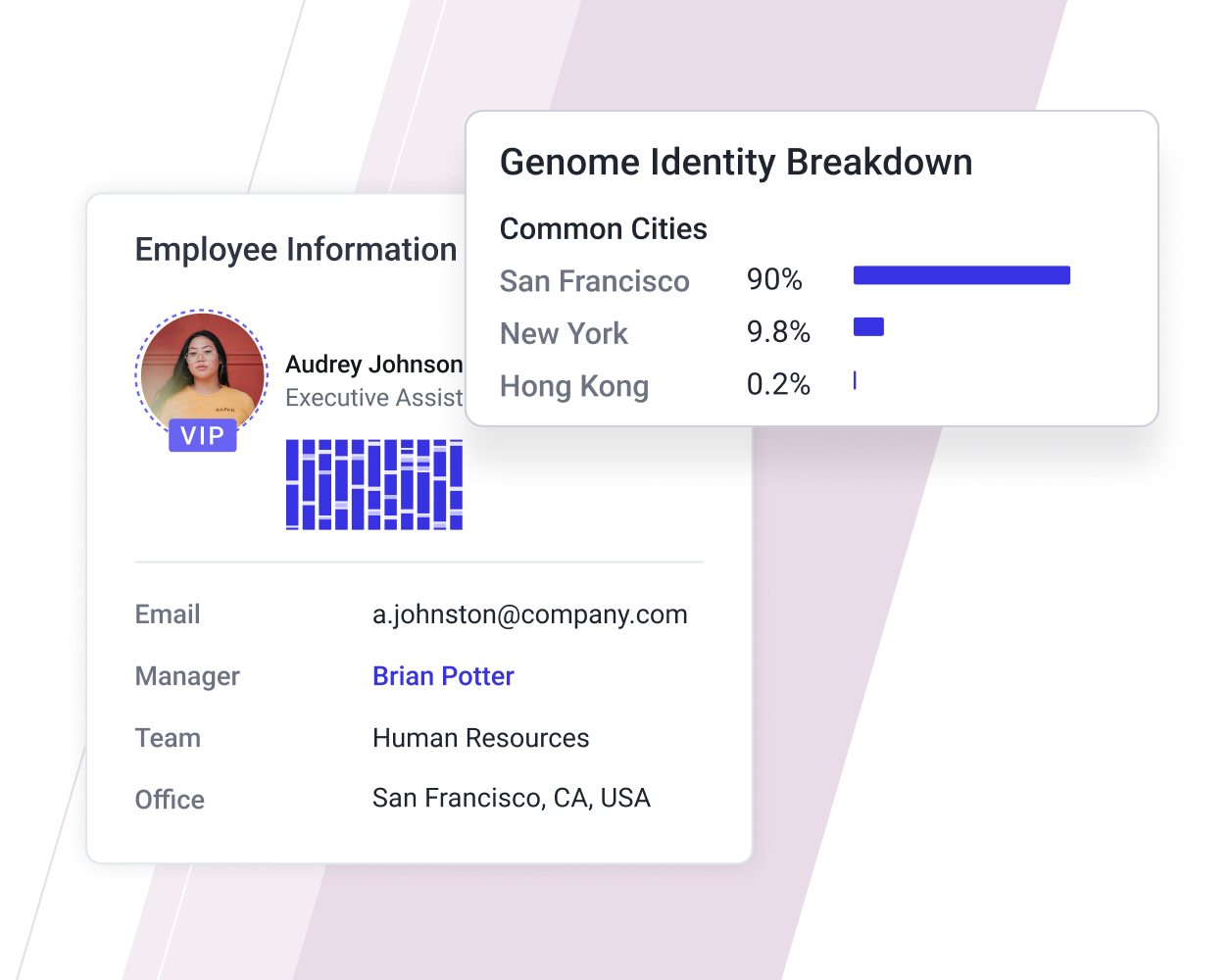
Detects Anomalous Behavior
Abnormal detects never before seen attacks with no traditional indicators of compromise by analyzing tens of thousands of unique signals to detect anomalies in email messages.
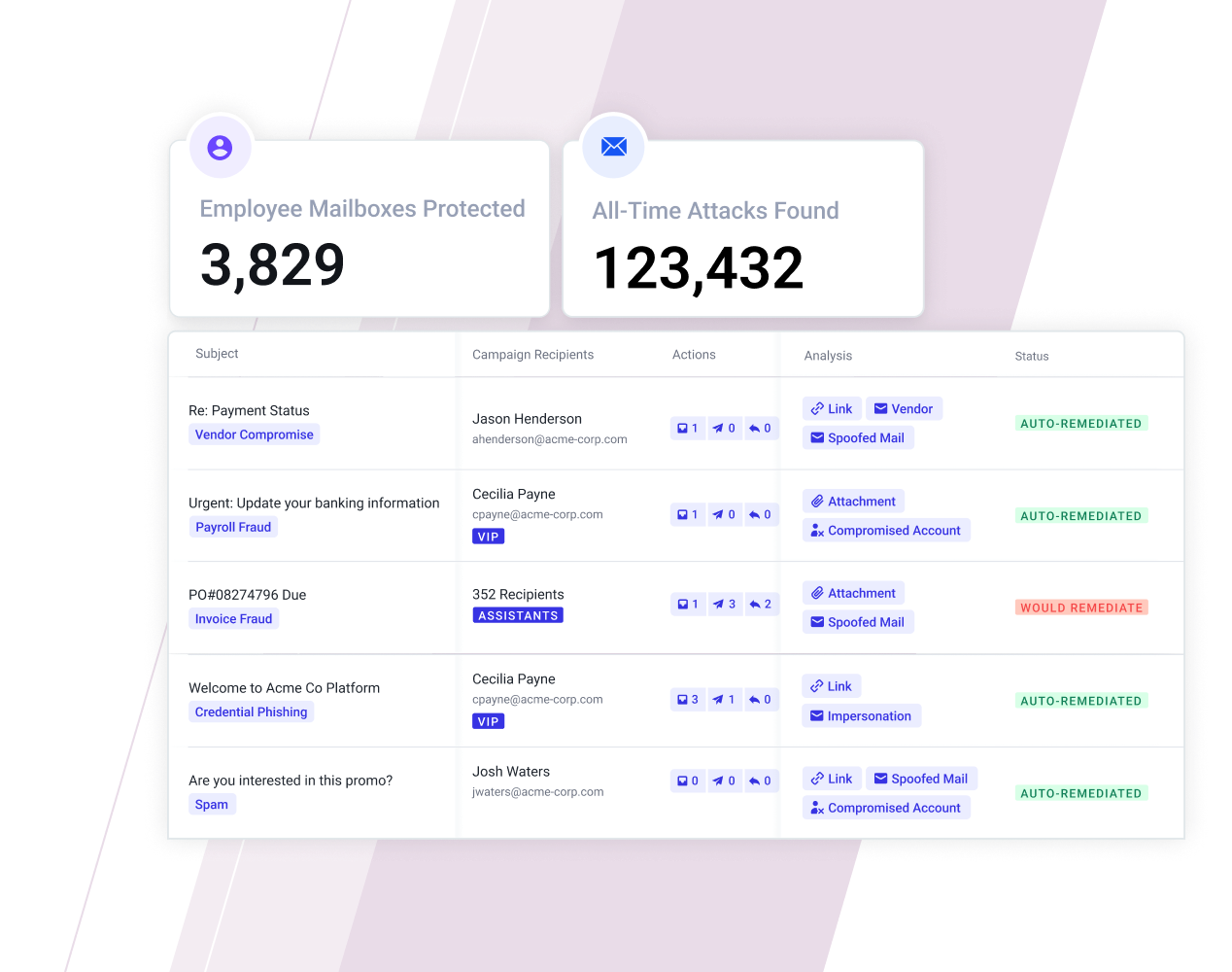
Remediates Malicious Emails to Prevent End-User Engagement
Abnormal automatically remediates malicious messages, removing the possibility of end-user engagement.

Explains Complex Attacks in Simple Language
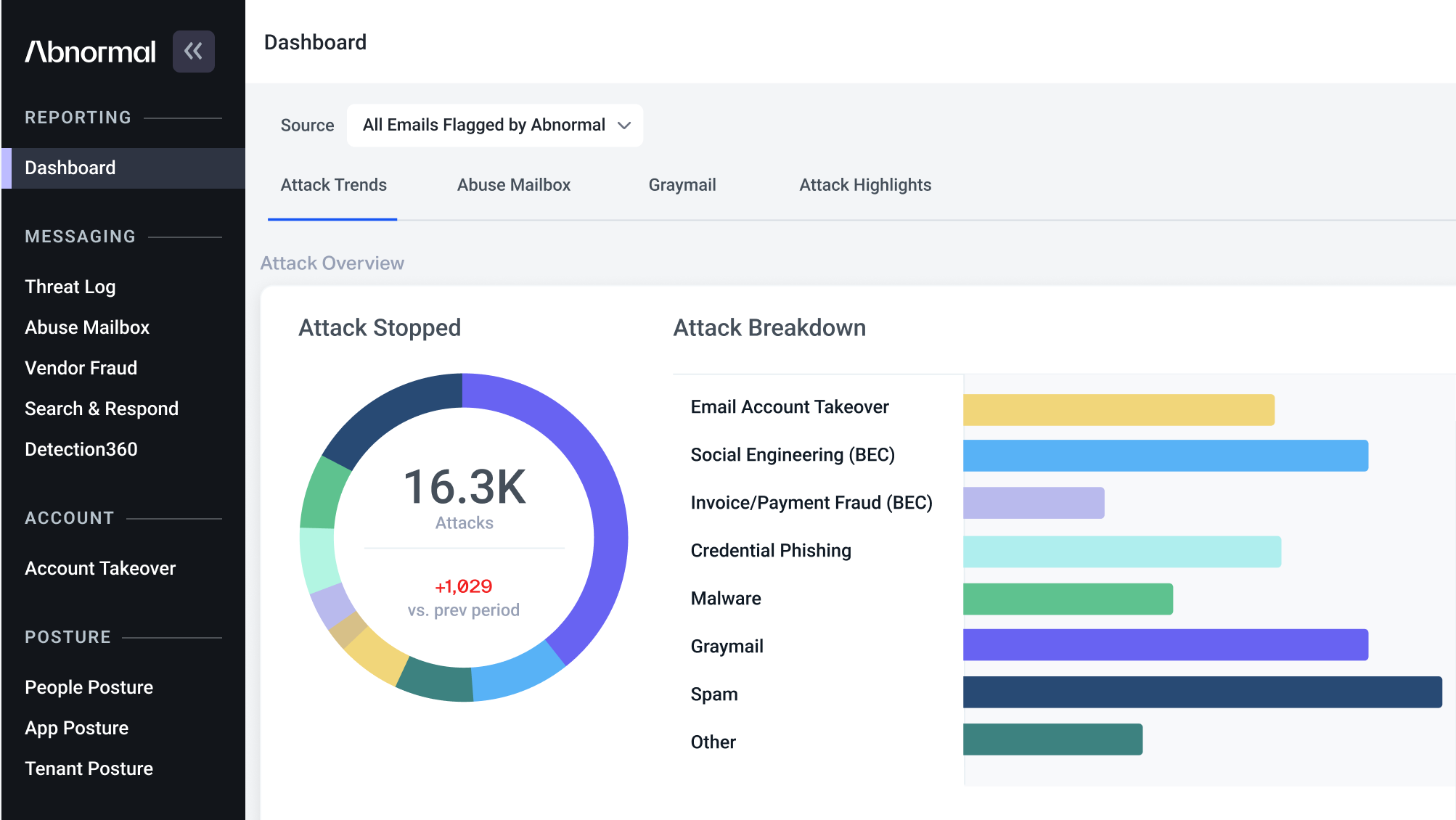
Abnormal provides searchable logs of every email message it categorizes with an in-depth Threat Log. Administrators can review trends, deep dive into attacks, or use search and respond capabilities to remediate misdirected messages.
See How Inbound Email Security Works
BEC Detection
Stops business email compromise attacks with behavioral models built on your organization’s relationship and communication patterns.
Behavioral AI
Baselines known-good behavior across every employee and every vendor to understand normal behavior.
VEC Detection
Monitors each vendor for risk indicators and automatically adapts protection to block attacks from compromised partners.
The realization of value was almost immediate—real-time visibility into attacks going on in the environment that are bypassing the traditional defenses. That context allowed ADT to start identifying threat trends while blocking them from employee inboxes.”
— Ryan Fritts, CISO, ADT
Stop Inbound Email Threats from Reaching Your Employees
Protect your organization from the full spectrum of inbound email attacks with Abnormal. See a Demo