USPS Impersonated in Credit Card Phishing Scam
With holiday delivery deadlines quickly approaching and online orders continuing to pour in, courier services are facing increasing pressure from anxious consumers. This rise in shipping demand has made Amazon, USPS, UPS, and FedEx targets of increasing impersonation attacks aimed at their unsuspecting customers. In this attack, attackers impersonate a USPS package tracking page to steal credit card credentials.
Summary of Attack Target
Platform: Office 365
Bypassed Email Security: IronPoint
Victims: Employees
Payload: Malicious Link
Technique: Impersonation
Overview of the Credit Card Phishing Attack
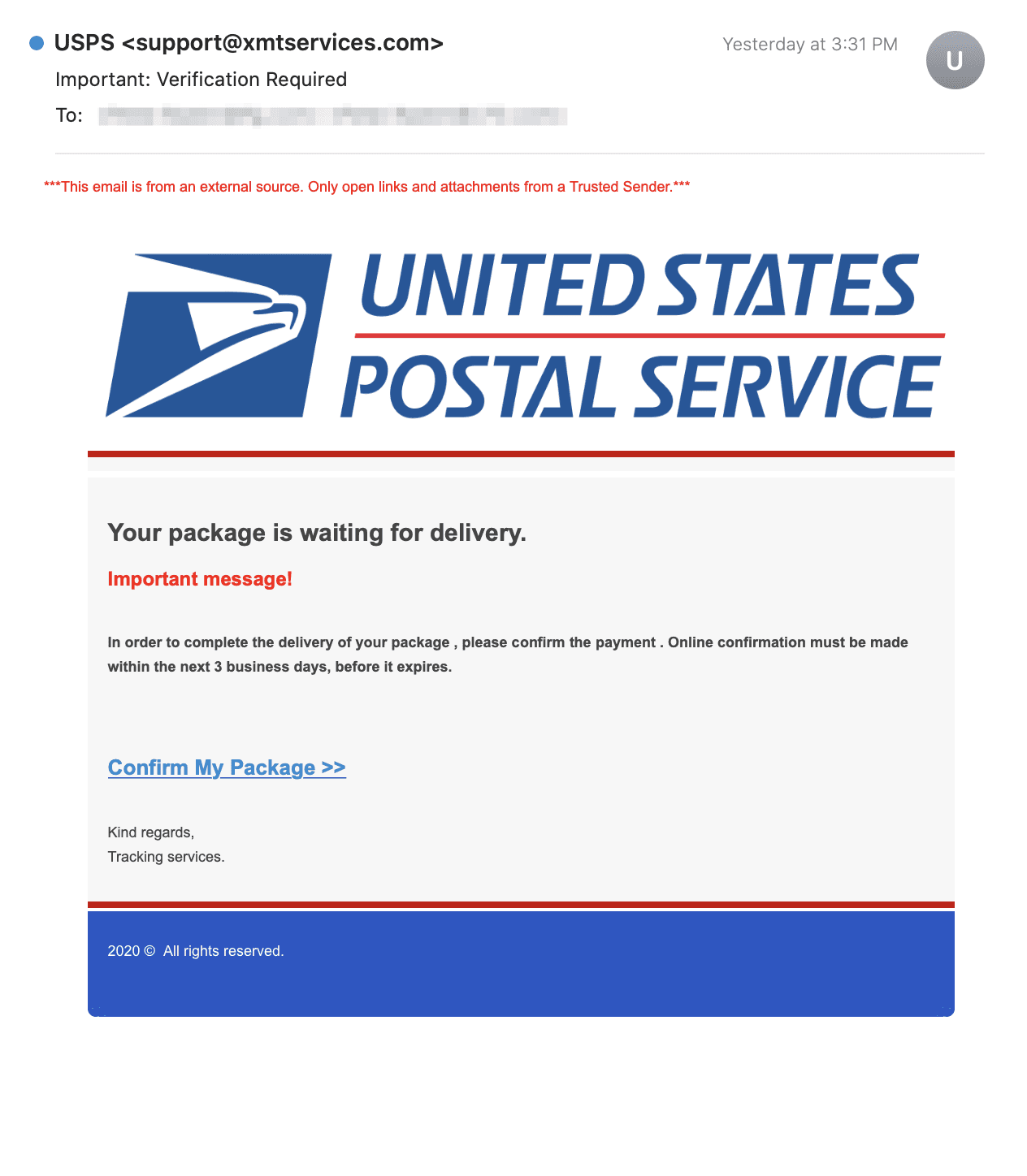
This attack mimics a delivery notification email from the U.S. Postal Service, notifying the recipient that their package cannot be delivered until their payment is confirmed. Although the email appears to originate from “USPS” and features the official USPS logo, the true sender is support@xmtservices.com.
The email prompts the recipient to confirm their package by clicking on a link, which leads the recipient to a fake USPS tracking site that claims that additional shipping fees must be paid to ensure package delivery. This page asks for payment details to fulfill this charge, setting a trap for the recipient to release sensitive credit card information to the scammers.
In an ironic twist, the email includes a banner that reads "***This email is from an external source. Only open links and attachments from a Trusted Sender.***," showcasing how far attackers will go to trick unsuspecting victims.
The malicious link hidden under the “Confirm My Package” hypertext redirects to https://www[.]kingstark[.]net/PackageBill/cvea1, a phishing site posing as a tracking page for USPS packages. The landing page contains a fake tracking number for the recipient's supposed package, and prompts them to enter their credit card information. If submitted, these payment credentials are sent directly to the attackers in a successful payment fraud scheme.
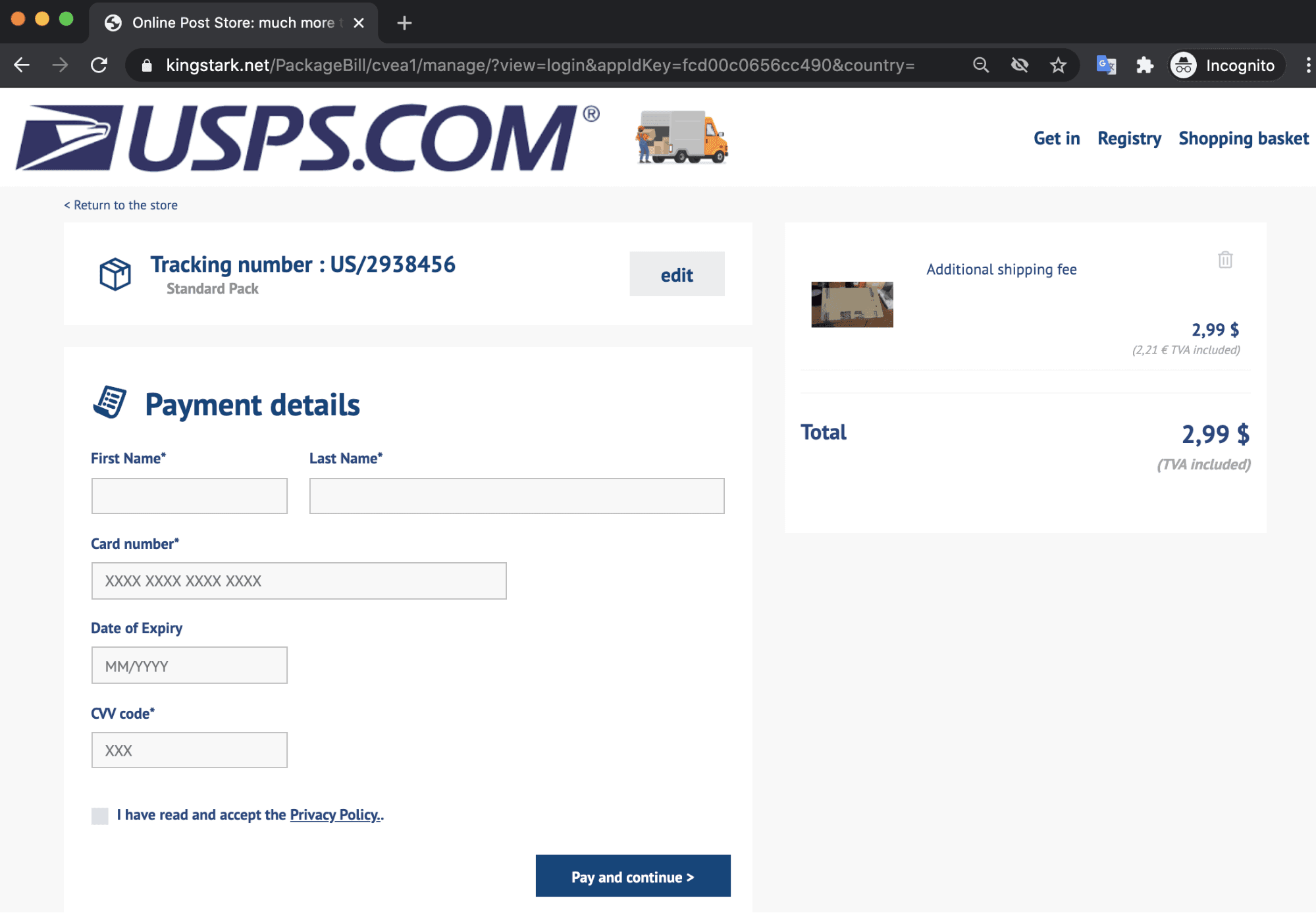
Should recipients fall for this attack, scammers can use their credit card information to make unauthorized transactions.
Why the Credit Card Phishing Attack is Effective
This attack creates legitimacy through the use of USPS logos in both the email and landing page. The landing page, in addition to a section for payment details, includes a fake tracking number, links that lead to actual USPS webpages, and even a checkbox for the recipient to indicate that they have accepted the USPS Privacy Policy. These details contribute to the authenticity of this scam, thus increasing the likelihood that a recipient will overlook the suspicious link and fall into the trap.
In addition, the email includes a sense of urgency and states that payment confirmation must be made within three days, or else it will expire and their package will not be delivered. Timed strategically before the holidays, the point is to motivate the recipient to act quickly so they receive their important packages in time. It also aligns to a time when consumers are expecting an increase in packages and are receiving delivery notification emails.
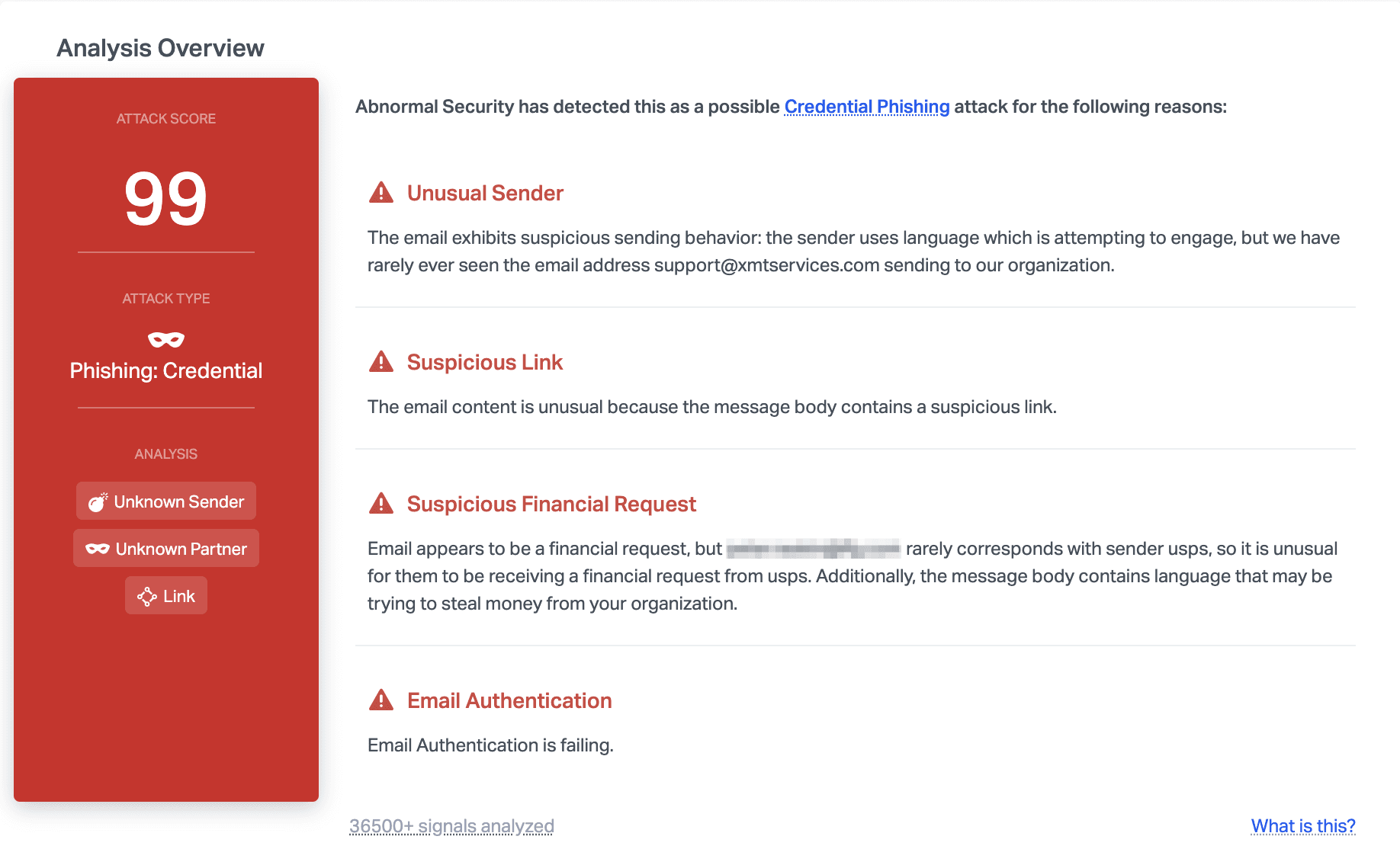
Abnormal stopped this email due to the unusual sender, suspicious link, and the fact that the email failed authentication—a clear indicator that the email is malicious. In addition, the fact that this email includes a financial request but USPS typically does not send financial requests indicates that this email may be fraudulent.
Shipping companies worldwide have reported an increase in email impersonation scams characterized by these fake delivery notifications. According to data from Check Point Software Technologies, November saw a 440% increase globally in shipping phishing emails compared to October. We expect this trend to continue to spike even more in December and throughout the duration of the holiday season.
Want to protect your employees from holiday-related phishing scams? Request a demo now to see how.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.

