The #1 AI-Native Platform
for Human Behavior Security
The #1 AI-Native Platform
for Human Behavior SecurityTrusted By More Than 15% of the Fortune 500
Abnormal Approach to Human Behavior Security
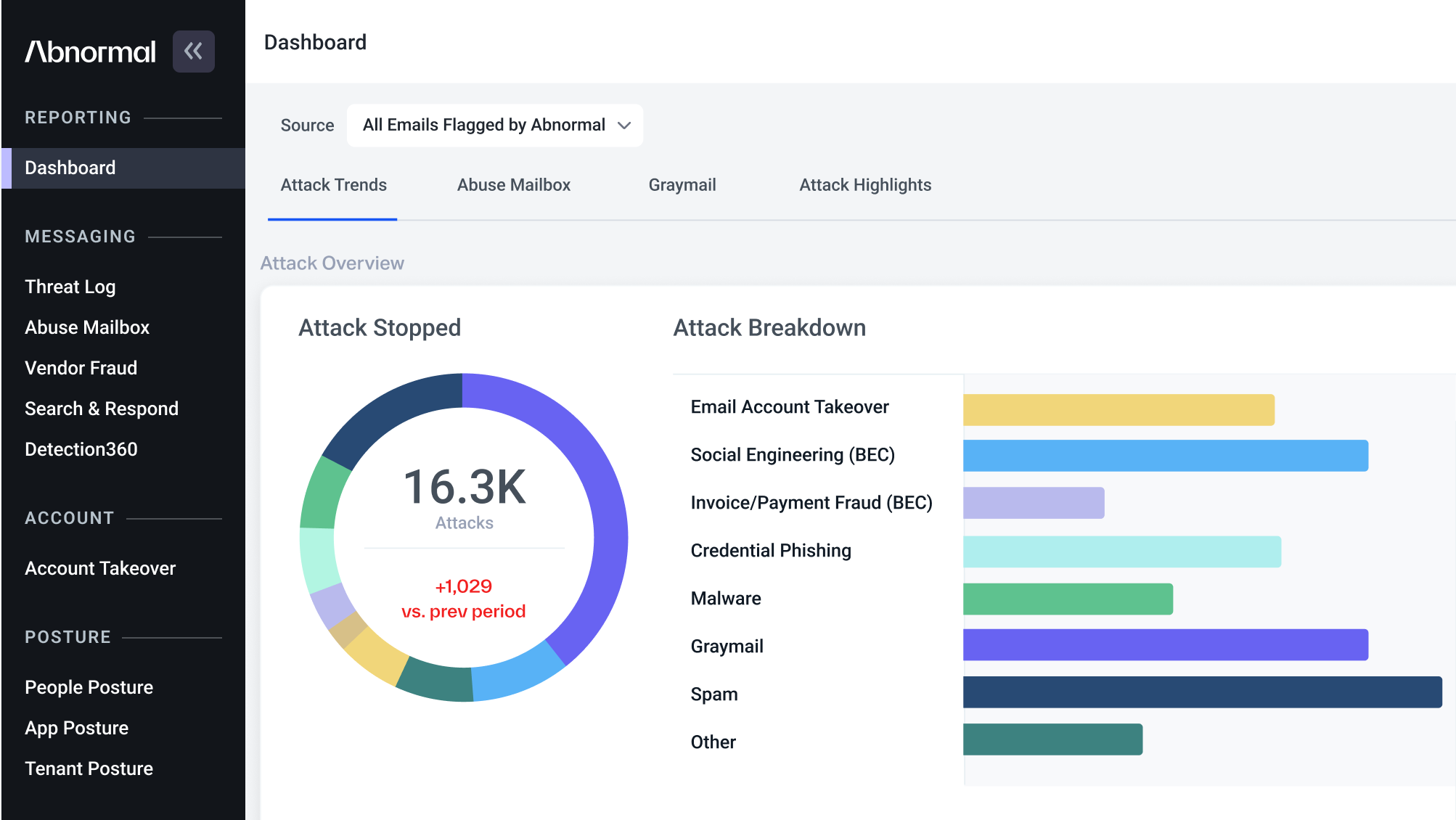
Today's email and cloud account breaches are rooted in tactics that exploit human behavior. Our mission is to protect humans with AI.
How do we do it? Abnormal deeply understands human behavior to provide unprecedented protection against tactics that exploit it, such as phishing attacks, socially-engineered threats, and cloud account takeovers.
See What Our Customers Say
Work Values that Actually Work
Abnormal’s values serve as the operating principles for every team member. From our CEO to our interns, we are all driven by the Abnormal VOICE Framework.
At Abnormal, we are committed to finding new ways to solve old problems, disrupting the traditional paradigm of security and providing fresh ways to tackle hard problems. Our VOICE values are how we achieve this, together.
Learn More

Abnormal Leadership Team
The Abnormal leadership team is composed of visionaries with decades of AI and ML experience, dedicated to delivering an exceptional customer experience. Their careers span influential roles at companies like Google, Twitter, Amazon, Proofpoint, Okta, Salesforce, and Slack.
Meet the Team
Abnormal Awards
An Abnormal Conversation with Greylock Partners
Abnormal Beginnings
Commitment, Chemistry, Experience
Abnormal Customer Love
Obsessing Over the Needs of Customers
The Abnormal Future
Using AI + ML to Enable Intelligent Trust
Abnormal Partnerships with Market Leaders
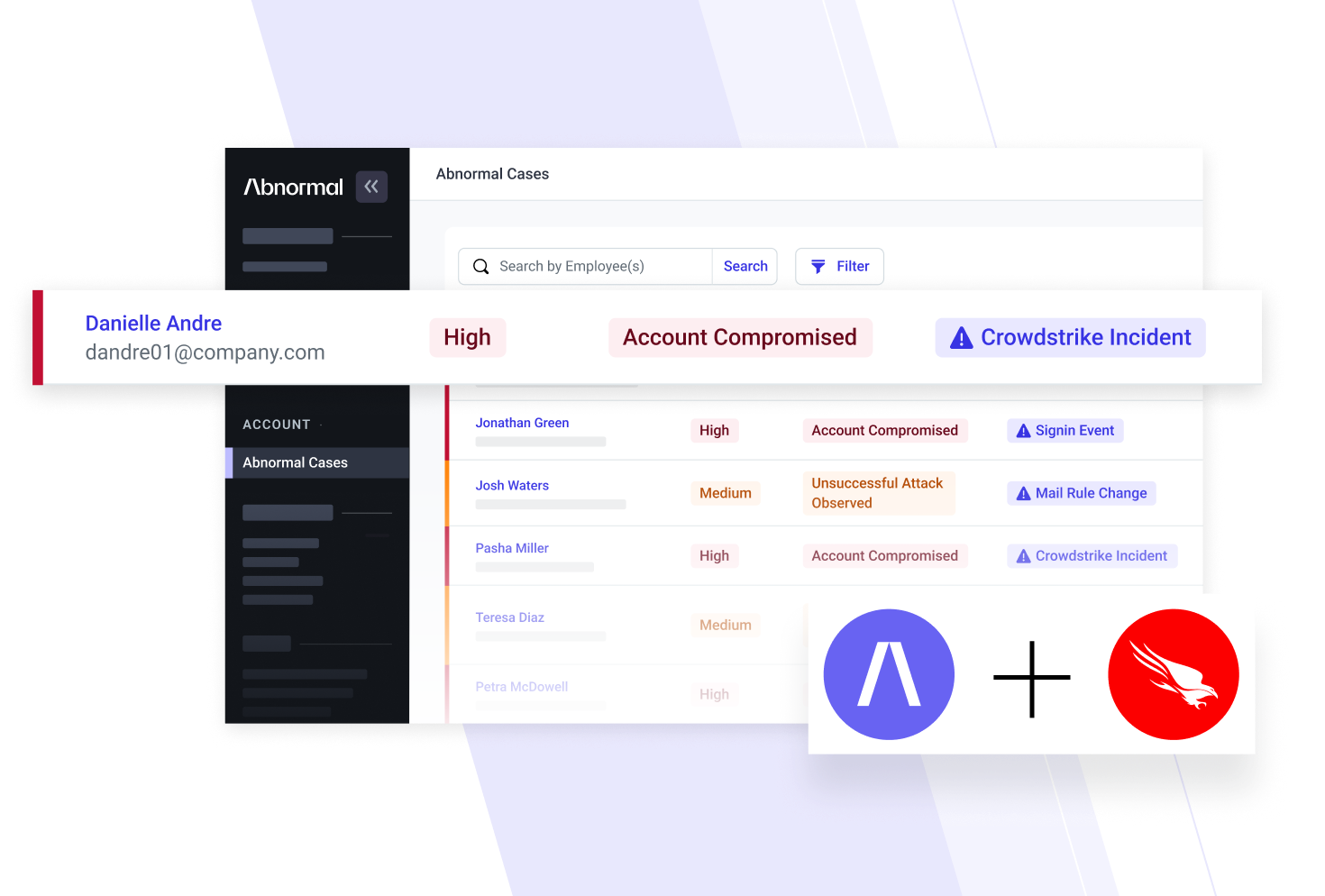
Abnormal partners with the best companies in cybersecurity, including Microsoft and CrowdStrike. With technology integrations and joint marketing strategies, Abnormal enables security teams to do more with their current tools.
See Abnormal + CrowdStrike
See Abnormal + Microsoft
Abnormal Intelligence
Abnormal Intelligence provides threat research that enables security teams to understand new trends in the email landscape. By uncovering the threat actors behind these attacks and the tactics they use, we can better predict shifts in their strategy.
Visit Abnormal Intelligence
Abnormal Experience
Nothing exceptional was ever normal. The DNA of our company is built on challenging existing constraints to continuously innovate.
None of our work would be possible without the people who make up our team. We are dedicated to providing opportunities for impact and learning, and we'd love to have you join us!
View Open Roles

Curious About Abnormal?
Want to discover how to get better email protection while lowering your email security spend? Have questions about how we protect our customers? Need to contact a real person? We’re here to help.
Contact Us
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email and collaboration application attacks with Abnormal. See a Demo