SharePoint Impersonated in O365 Credential Phishing Attempt
SharePoint is an increasingly popular tool for Microsoft users, especially in a time when millions of employees are working remotely. In this attack, malicious actors make use of an automated message from Sharepoint to send phishing emails.
Summary of Attack Target
- Platform: Office 365
- Email Security Bypassed: Proofpoint
- Payload: Malicious Link
- Technique: Impersonation
Overview of the SharePoint Impersonation Attack
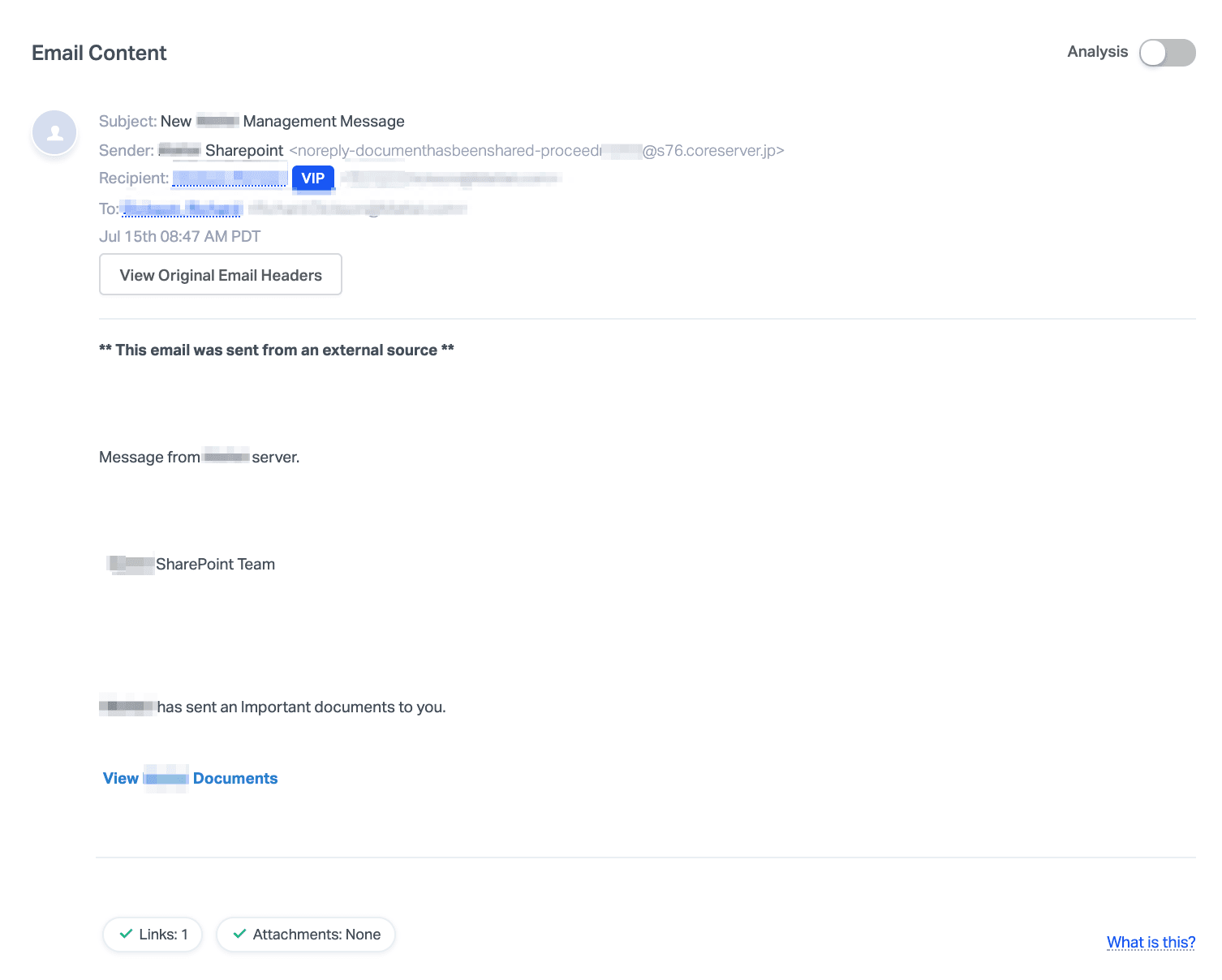
This attack impersonates an automated message from SharePoint to send phishing emails. The email itself is not addressed to any specific individual and is instead meant to cast a wide net to phish for employee credentials. Here, attackers are leveraging the probability that at least one employee will fall for the attack, and—if successful—can use their credentials to gain access to sensitive corporate information or to launch additional, more successful attacks using the compromised account.
The body content is brief and uses language similar to automated file-sharing notifications. The name of the target company is inserted at every possible point, including the sender display name, and is pretending to originate from within the user’s organization. The content of the email is vague and encourages the user to click the link to see the SharePoint documents.
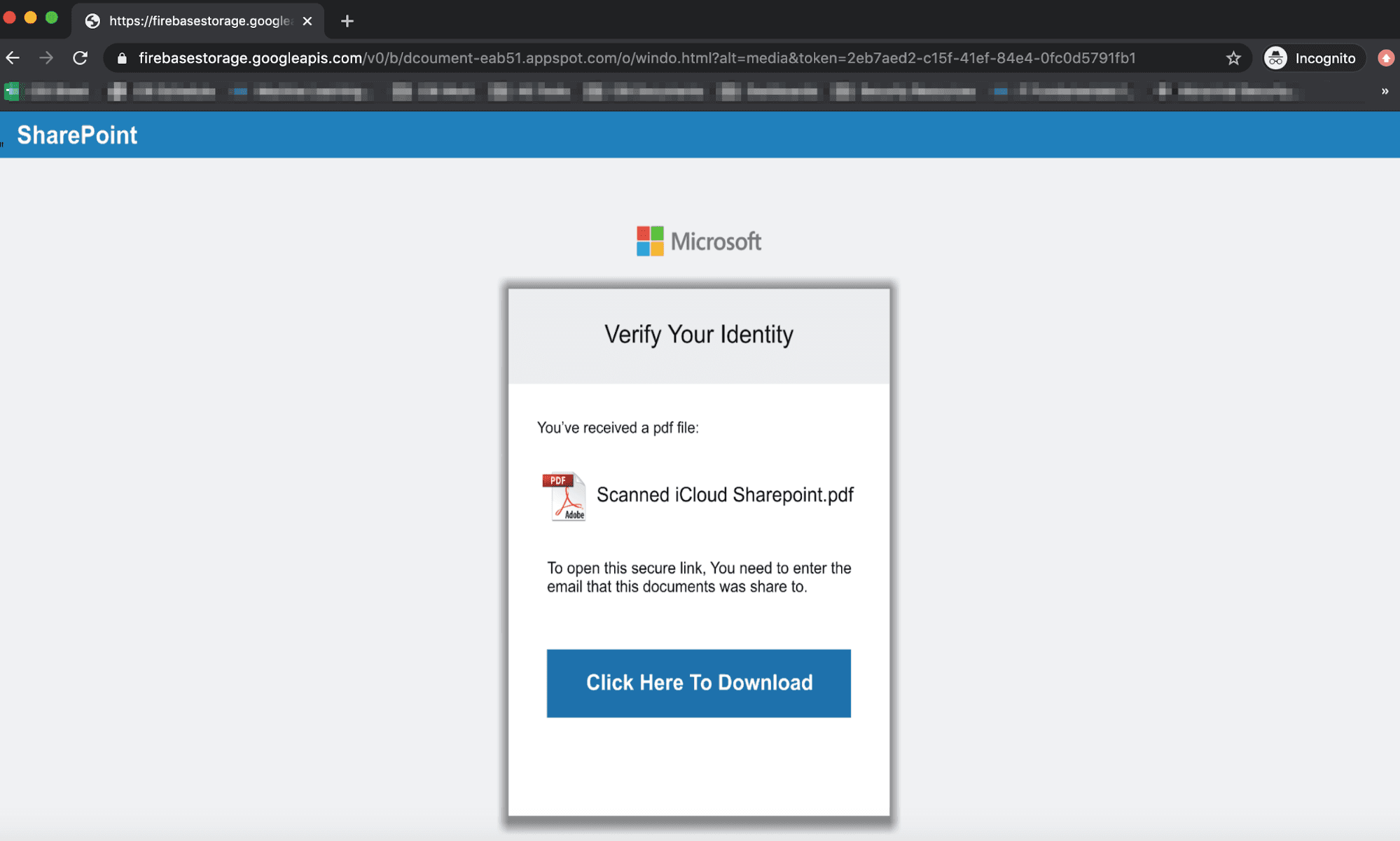
After clicking on the link, the landing page is reached through multiple redirects and ultimately lands the recipient on an impersonated SharePoint page where they are encouraged to click to download the file.
Clicking on it either redirects to a submission form where the recipient can enter their credentials, or downloads a PDF that redirects to another site. If the recipient falls victim to this type of attack, their credentials are compromised, as well as any data stored on their account. This places employees and their networks at considerable risk as attackers can launch internal attacks to steal more credentials and information from the organization.
Why the SharePoint Impersonation Attack is Effective
Within the email, the malicious URL is disguised as text via hyperlink. If the link was not disguised, the recipient might spot an inconsistency, as the landing page does not lead to a SharePoint link. That said, the landing page itself looks identical to a secure SharePoint file that requires the recipient's credential information.
The landing page utilizes the Microsoft and SharePoint logos to impersonate these official brands and masquerade as a legitimate site. In the email body, the recipient’s company name was also used numerous times to impersonate an internal document shared by this service. Recipients may be convinced that the email is safe and coming from their company because of the repetitive inclusion of the company name.
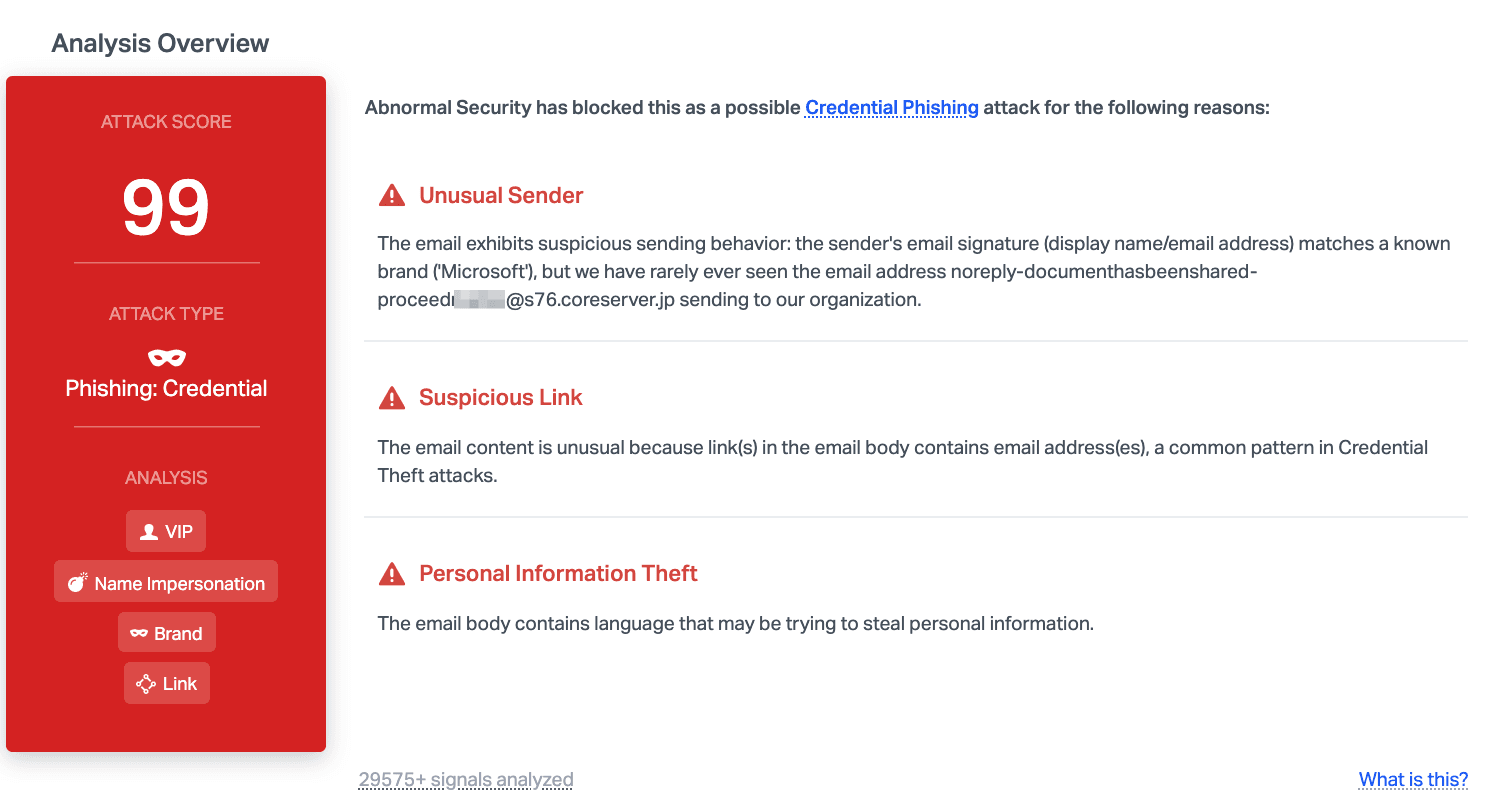
Abnormal can detect and stop this attack due to the unusual sender, where the display name matches the Microsoft band, but the email does not. Further analysis shows the suspicious link and the language that conveys that it might be attempting to steal credentials. Combined, these are all indicators that the email is malicious, prompting Abnormal to block it before it reaches inboxes.
To learn how Abnormal can protect your organization from credential phishing attempts, request a demo today.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.

