Outlook Update Sent in Credential Phishing Attempt
Office 365 and its associated apps (Excel, PowerPoint, Word, and Outlook) are an integral business tool for many organizations. Hackers consistently target the Microsoft accounts of employees, as these accounts are linked to a treasure trove of sensitive business information. In this attack, attackers impersonate an official notification from the Outlook team in order to steal user account credentials of employees.
Summary of Attack Target
- Platform: Office 365
- Email Security Bypassed: IronPort
- Payload: Malicious Link
- Technique: Spoofed Email
Overview of the Outlook Credential Phishing Attack
The attacker impersonates an automated notification from the Outlook team on behalf of the recipient's company. Recipients are urged to “upgrade” their Outlook services within 24 hours, or email deliveries to them will be delayed. The email also states that the upgrade is compulsory and the email mailbox is monitored 24/7.

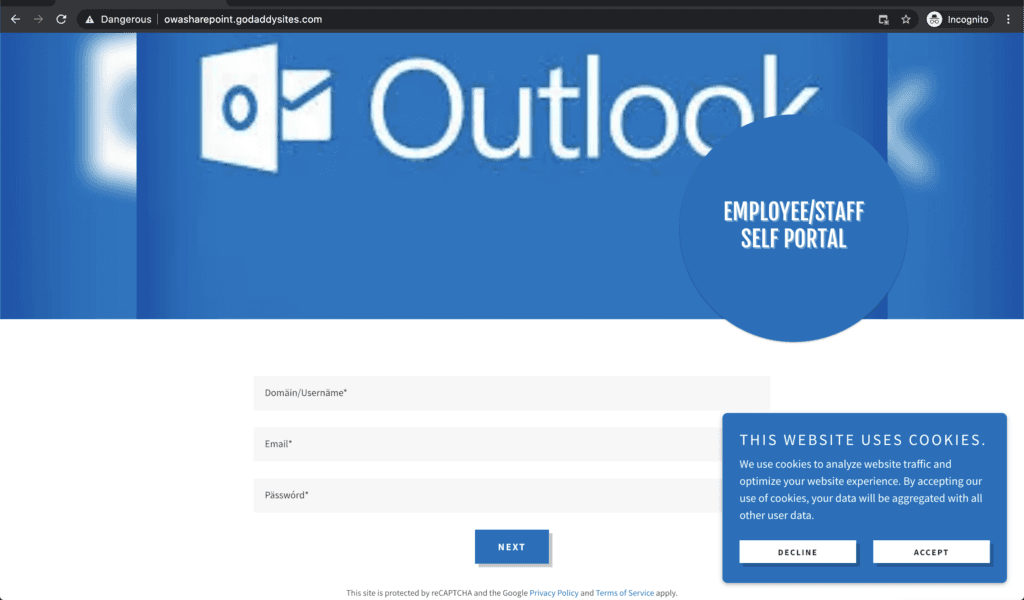
Within the email, the payload link is hidden by text, which directs to a fake Outlook login page hosted on a website controlled by the attacker and is used to store input user credentials. The phishing website is hosted on GoDaddy, which allows the site’s use of cookies. This may allow the attacker to track the email recipient's movement on the site.
Once user credentials are submitted, a notice pops up that the upgrade will be completed within the next 48 hours. In that time, the attacker can compromise the recipient's account—including access to Outlook, OneDrive, and other collaboration tools.
Why the Outlook Impersonation Attack is Effective
The message urges the recipient to click on a link within 24 hours and enter their credentials immediately in order to avoid a delay in mail delivery. Because attackers are leveraging this urgency, recipients may scramble to resolve the issue without being as vigilant as they might otherwise be—only to find out later that they have given a malicious entity control over their account.
In addition, the attackers are hiding the real URL for the landing page they're directing recipients to, hoping to avoid the suspicion that would arise from displaying the full (non-Microsoft) URL. And given that this email is being sent by someone on the Outlook team on behalf of the company's IT team, the landing page aligns with the content of the email.
Oddly, there's ambiguity in this email that might aid in its effectiveness: the email is written as though it could be coming from either the official Microsoft Outlook team, or the team within the company's IT department that handles Outlook. This means that recipients can project their assumptions onto the email and reconcile any inconsistencies with the idea that they may have misread or misinterpreted it initially.
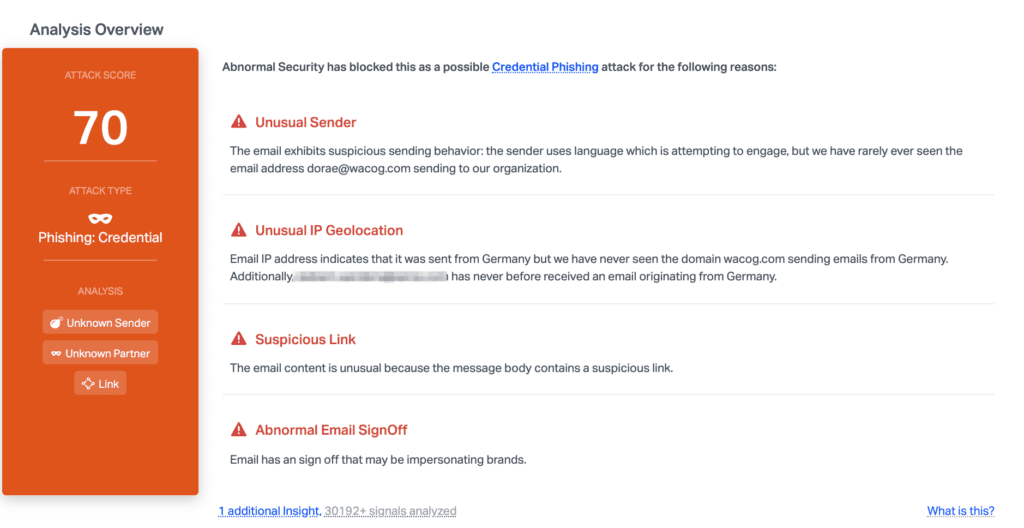
Abnormal detected this attack due to the unusual sender email, combined with the unusual IP geolocation—this domain does not usually send email from Germany. Add the suspicious link and the brand impersonation signoff, and it quickly becomes clear that this email is a malicious credential phishing attempt.
Discover how Abnormal can protect you from brand impersonation attacks by requesting a demo today.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.