Accesses 10x more behavioral data to deeply and contextually understand the behavior, communications, and processes of every employee and every vendor across the entire organization.
Go ahead, be human.
Abnormal AI keeps your email protected.
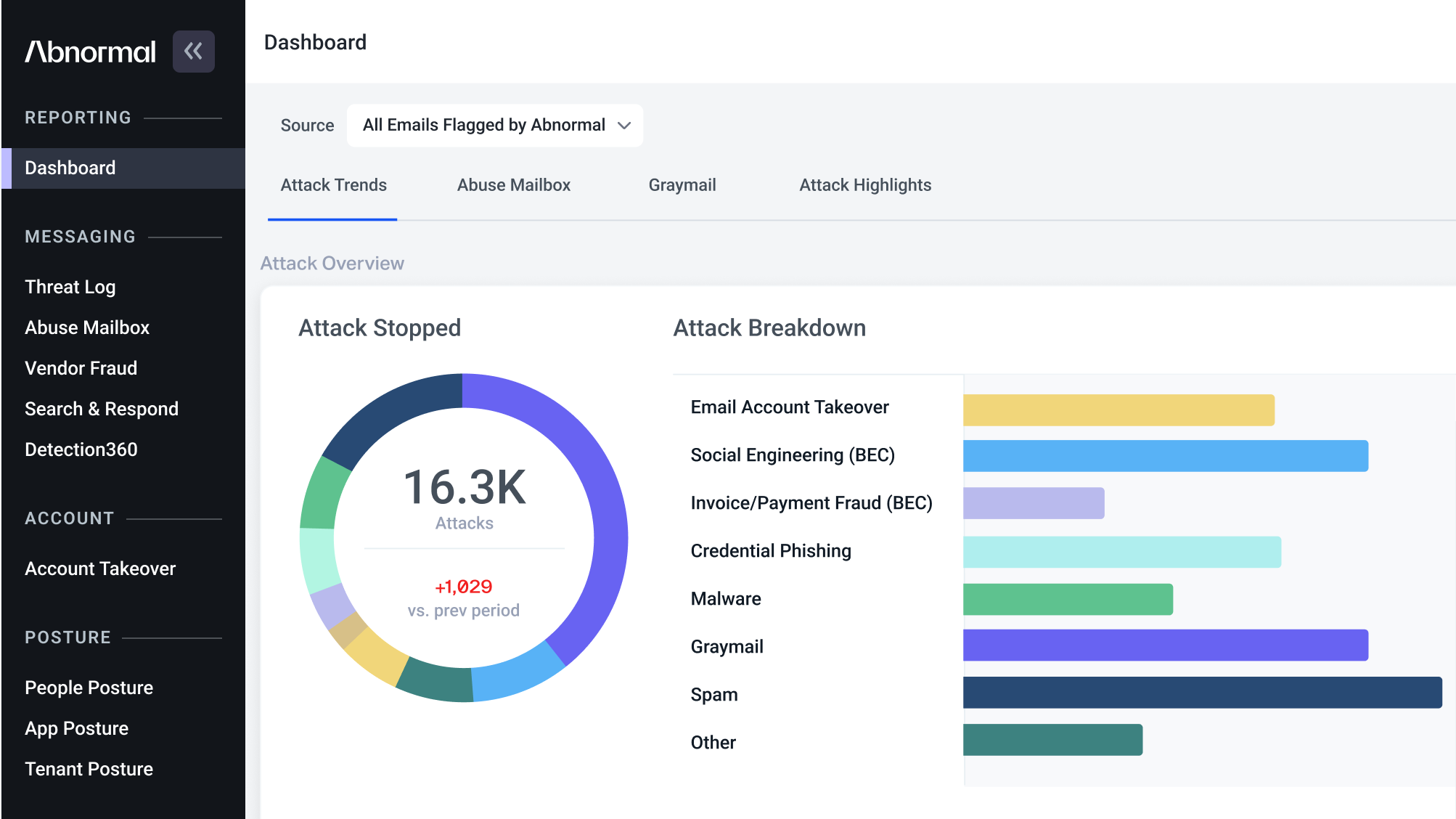
Get comprehensive email protection against attacks that exploit human behavior, including phishing, social engineering, and account takeovers, with a platform that deeply understands human behavior.
See a Demo
Trusted By More Than 15% of the Fortune 500
The Problem
Email Attacks are the #1 Threat to Organizations Today
Humans are the biggest vulnerability to your organization, and email is how they're targeted.
Today's breaches exploit the inherent trust humans place in digital communications—primarily email, the most extensive and vulnerable communications channel. Targeted email attacks on employees pose the highest cybersecurity risk and can lead to data breaches or significant financial losses.
What's Making the Problem Worse
Modern Trends Worsen the Human Vulnerability
The way we work is changing, so the way attackers work is changing too.
Shift to Cloud Email
has created
New Attack Vectors
Attackers can now directly infiltrate email accounts by defeating authentication and exploiting misconfigurations.
Rise of Generative AI
has created
Hyper-Personalized Attacks
With ChatGPT and similar platforms, it’s
now easier for even petty criminals to launch highly sophisticated and targeted attacks
at scale.
Interconnected Cloud Ecosystem
has created
A Larger Impact of Breaches
Gaining access to email accounts gives attackers unconstrained access to all other connected cloud accounts and the data within them.
The Unique Way We Solve It
The Abnormal Human Behavior AI Platform
Abnormal takes a different approach to email security with our AI-native solution and API-based architecture.
Products You Will Love
Abnormal Products to Protect Your Humans
Achieve complete protection with products that stop email attacks, automate workflows, and boost productivity.
See All Products
The Value You Can Expect
Enabling Abnormal Business Value
With a platform designed for our customers, you can do more and worry less.
Why Customers Choose Abnormal
See It For Yourself
Get AI Protection for Your Human Interactions
Protect your organization from socially-engineered email attacks that target human behavior.
Request a Demo
DISCOVER MORE